cryptogram
A cryptogram is a word puzzle featuring encrypted text that the user decrypts to reveal a message of some sort. Once used for message security, cryptograms are now typically only used for entertainment purposes in newspapers and magazines. Cryptoquotes and cryptoquips are common variations that feature quotations.
Cryptograms in newspapers and magazines are usually based on a simple substitution cipher, often replacing each letter in the alphabet with a different one. The letter A, for example, might be represented by the letter K, while the letter K is represented by the letter R. Puzzle solvers use a number of methods to help them decrypt the messages.
Frequency analysis can be applied to note how often words or particular combinations of letters appear. Coupled with a knowledge of common short words, that information can yield helpful clues. A single letter usually represents either "A" or "I," common two-letter words include "if," "as" and "at," and a three-letter word is quite often "the" or "and." If a single letter also appears as the start of a three-letter word, then that word has a better-than-average chance of being "and," since "T" (the first letter in "the") is not a word.
Patterns of letters and words provide more clues for cryptanalysis. For example, a four letter word starting and ending with the same letter has a better-than-average possibility of being "that." You might then notice a three-letter word starting with the two same letters, which is likely to be "the" if "that" is correct. Penciling in every occurence of those letters that can be guessed will provide the solver with clues about the other letters and words.
Cryptograms have a long history. One of the best known is Caesar's cipher, which is said to be among the less complicated used by the Roman Emperor. According to Suetonius, who wrote a set of biographies of Julius Caesar in 121 A.D.:
"If he had anything confidential to say, he wrote it in cipher, that is, by so changing the order of the letters of the alphabet, that not a word could be made out. If anyone wishes to decipher these, and get at their meaning, he must substitute the fourth letter of the alphabet, namely D, for A, and so with the others."
From Caesar's day (at least), cryptograms were used to protect the content of military and personal messages. Cryptograms designed purely for entertainment purposes made their appearance in the Middle Ages as an intellectual pastime for monks. More recently, in 1929, the American Cryptogram Association was formed with the goal of making the cryptogram as valued by hobbyists with chess, in the words of the ACA: “thus contributing to the happiness of mankind.”
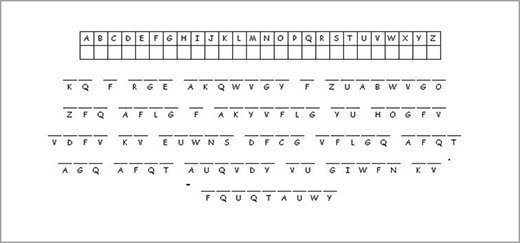
Here's an example of a cryptogram based on one of our Favorite Technology Quotes: