data broker (information broker)
What is a data broker (information broker)?
A data broker, also called an information broker or information reseller, is a business that collects large amounts of personal information about consumers. The broker also analyzes and aggregates the collected data, and then sells or licenses the information to third-party individuals or organizations. Those third parties use the purchased information for marketing, risk mitigation, fraud detection and other purposes.
Data brokers collect personal information from a wide range of public and nonpublic sources. They might collect data from courthouse records, voter registries, census data, property records, motor vehicle departments or vital records offices, including marriage licenses or birth certificates. They might also purchase data from commercial sources, such as retail or credit card companies.
In some cases, data brokers gather personal information through browser cookies, either purchasing the information from a web service or deploying the cookies themselves. Data brokers might also gather data from other sources, such as mobile apps, social media sites or loyalty card programs. Data is collected in so many ways and in so many places around the world that data brokers have an almost endless supply of personal information.
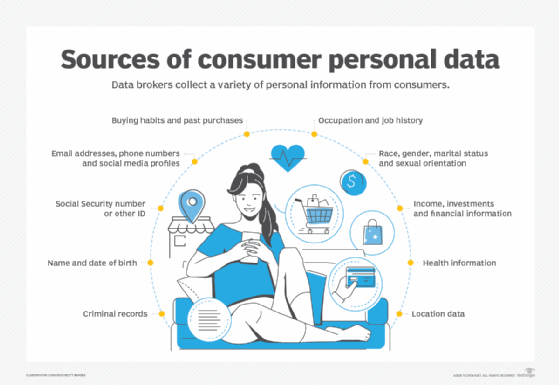
What information do data brokers collect?
Data brokers continuously update their data stores to ensure they have the most accurate and complete set of information available on each person. From this data, they can piece together detailed profiles that might include thousands of data points. The following are examples of the types of data that a broker might collect about an individual:
- Full name.
- Age and gender.
- Race and ethnicity.
- Sexual orientation.
- Social Security number or other national ID.
- Current and past addresses.
- Email addresses and telephone numbers.
- Marital status and family relationships.
- Occupation and job history.
- Income and financial history, including bankruptcies.
- Legal issues and criminal records.
- Education and military service.
- Real estate assets and other investments.
- Purchase histories and buying habits.
- Medical and mental health histories.
- Interests, hobbies and political views.
- Social media profiles.
- GPS location data.
Once they've collected all this information, data brokers run advanced analytics against the data to identify patterns and to group the profiles into categories that they can sell or license to other companies. For example, a data broker might offer data about pickleball enthusiasts. A retailer might purchase this data to help market a new line of pickleball supplies.
Some data brokers now also use artificial intelligence algorithms to infer additional details about each individual, resulting in profiles that include a greater number of details, some of which are now assumed. This could potentially expose even more personal information about an individual or lead to incorrect assessments that negatively affect that person.
What information do data brokers sell?
Data brokers sell a wide range of personal information to numerous organizations. There are no specific industry rules or standards that require data brokers to limit the types of information they gather or how they go about peddling it. Even so, the data they offer tends to fall into one of the following categories:
- Marketing and advertising. Organizations acquire this type of data primarily to market their products and services. In this way, they can better target their advertisements, special offers and other marketing strategies. For example, consumers might see the result of this process in the targeted ads they receive not long after conducting an internet search on a related topic.
- Risk mitigation. Financial institutions, insurance companies and other organizations use this data to assess the risks associated with a potential customer or transaction. The data might include credit scores, current debt levels, income information or other details that help the institution assess the level of risk. For example, a bank might use this information when determining whether to give a customer a car loan and what interest rate to charge.
- Fraud detection. Banks and other financial institutions typically use this data to monitor their customers' accounts and identify potential fraud. For instance, a credit card company might use this type of information when monitoring account activities to better detect fraudulent behavior.
- People search. Websites that sell information about specific individuals acquire this type of data to support their online services. For example, a property management company might use this service to do a background check on a potential tenant, or a business that's interviewing prospective employees might want to check for past criminal records.
These four categories aren't always interpreted in the same way, nor do they represent the only ways in which the data can be categorized. For example, some sources treat risk mitigation and fraud detection as one category, while other sources include a category for health data, which might be used by health insurance companies to set rates or pharmaceutical companies to market their products.
How are data brokers regulated?
Currently, there's no U.S. federal legislation that requires data brokers to share the information they have gathered about consumers or that prevents them from selling the information to legitimate businesses. However, some U.S. states are starting to take a much closer look at privacy protections. California has been at the forefront of this effort with its California Consumer Privacy Act, which gives consumers the right to know what data has been collected, as well as the right to have it deleted.
Countries outside the U.S. are also taking steps to protect private information. The most notable of these efforts is the European Union's General Data Protection Regulation (GDPR). Under the GDPR, consumers must give their unambiguous consent before an organization is allowed to process their personal data in any way. In addition, consumers can request that their personal data be deleted.
To provide greater transparency, data broker Acxiom created a web-based privacy center that offers U.S. and international consumers more control over their personal data. For example, U.S. consumers can see what information Acxiom has collected about them and request that it be deleted. Although some view the privacy center in a favorable light, critics maintain that the website is just another way for the company to gather more data.
To help consumers better understand their data privacy rights, the nonprofit organization Privacy Rights Clearinghouse addresses the issues surrounding access to information and provides resources, including reports, guides and law overviews.
Learn what security measures organizations are using to protect customer data from identity theft and other fraudulent activities.
