What are Internet data caps and why do providers use them?
What is an Internet data cap?
A data cap, also known as a bandwidth cap, is a limit that service providers impose on the amount of data a user account can transfer at a specified level of throughput over a given time period, for a specified fee. The term applies to both home internet service and mobile data plans.
Data caps are usually imposed as a maximum allowed amount of data in a month for an agreed-upon charge. As a rule, when the user exceeds that limit, they're charged at a higher rate for further data use or their internet speed might be throttled to a slower rate.
Data caps are uniformly unpopular with customers. As a result, internet service providers (ISPs) often refer to them by other names such as fair use or fair access policies, use-based billing or band caps.
How do Internet data caps work?
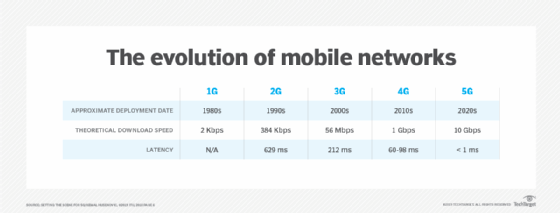
Data caps place a restriction on the amount of data a user can consume over their internet connection within a given billing cycle. ISPs measure data use in gigabytes (GB) or terabytes (TB). Once a user reaches their data cap, their internet speed may be throttled, leading to slower connection speeds, or they may incur additional charges for exceeding the limit. For example, a mobile user paying for a 5G plan may be downgraded to 4G for mobile data beyond their data cap.
Many ISPs offer tools or online portals where customers can monitor their data use throughout the billing cycle. These tools often display real-time data consumption, so users can track their data use and avoid additional data use when they're close to exceeding their data cap.
The Federal Communications Commission has a Data Caps Experience Form available. On it, consumers can share their experiences with data caps and let the FCC know of various issues.
Why do internet providers use data caps?
ISPs implement data caps for various reasons. The following are the most common ones:
- Network management. Data caps can help manage network congestion by preventing a small percentage of users from consuming an excessive amount of bandwidth. Excessive bandwidth use can degrade the internet experience for other customers.
- Revenue generation. Data caps can serve as a revenue stream for ISPs, as users who exceed their data limits can be subject to overage fees or encouraged to upgrade to higher-priced plans with larger data allowances. Service providers also sometimes impose data caps when they have a monopoly in a given area.
- Tiered pricing models. Some ISPs use data caps to differentiate between service tiers, offering unlimited data plans at a premium price while providing lower-cost plans with capped data allowances.
- Terms of use breach. An ISP might impose a data cap when a customer shares access with other users, employs file-sharing software or otherwise breaks terms of use.
Challenges and hidden costs of data caps
Data caps imposed by ISPs present several challenges and hidden costs that can affect consumers' internet usage and monthly budgeting. Some of the most important include the following:
Impact on online activities
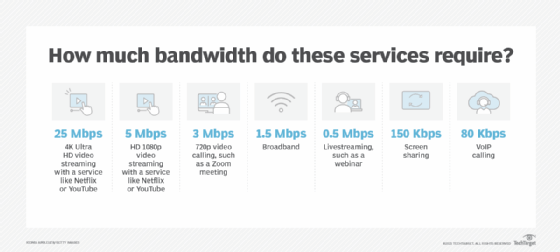
Data caps can disrupt everyday online activities such as using social media, playing audio through smart speakers, watching high-quality video content on streaming services like Netflix, online gaming and video calls. Each of these activities consumes significant data, and as households increasingly rely on high-speed internet for both leisure and work, data caps can limit these essential activities.
Extra charges and overage fees
Many ISPs enforce overage fees when users exceed their data cap. These add-on fees can increase a user's monthly bill for internet, especially for households that consume a lot of media or have multiple users connected to the same network.
Throttling and slower internet speeds
Exceeding an internet data cap can result in throttling. ISPs often deprioritize the internet speeds of users who exceed their data allowance, leading to slower Wi-Fi speeds. This can be frustrating at the end of the month when customers are most likely to hit their data cap. Data caps result in lower rates of internet access to online materials, especially multimedia and streaming content, which is a problem for content creators and their advertisers.
Variability in data caps among ISPs
The presence and strictness of data caps vary among ISPs. For instance, fixed wireless and satellite internet plans often have stricter caps compared to cable or DSL. This variability can make it challenging for consumers to choose an ISP that fits their data needs without incurring additional fees.
The cost of unlimited data plans
For users frequently exceeding their data caps, ISPs offer the option to upgrade to unlimited data plans. However, these plans are typically more expensive. This makes it crucial for consumers to evaluate their data needs against their budget constraints.
Cellular data privacy concerns
Increased reliance on cellular data due to insufficient home internet can raise data privacy and security concerns. The generation of personal data on mobile devices poses more risks than on secured home internet connections.
How to avoid data caps
Consumers can avoid data caps by researching their ISP's data cap policies and implementing best practices. Some of the best methods to avoid data caps include the following:
- Engage in data minimization and avoid applications with significant data use such as video games.
- Download the internet service provider's app to keep an eye on data use throughout the month.
- Check the built-in settings to monitor data usage if using personal routers.
- Use monitoring tools or software to track internet data use effectively.
- Use bonus times offered by ISPs and downgrade activities during peak hours to conserve data.
- Power down or disconnect devices when not in use to save data.
- Optimize settings on devices connected to your home Wi-Fi, including computers, smartphones and game consoles to minimize data drain.
- Keep antivirus, antispyware and firewall software up to date to prevent unwanted background data use.
- Install controls to manage and monitor internet use within the household.
- Consider switching to unlimited data plans if frequently exceeding data caps to avoid overage charges and throttling.
- Use low power mode on mobile devices to reduce data use.
Effective data management involves not only monitoring and adjusting how data is used but also making informed decisions about the type of internet plan that aligns with a consumer's needs. Households can optimize their internet experience and manage costs more effectively by understanding the specifics of data consumption for different activities and employing tools and strategies to control use.
What internet service providers use data caps?
ISPs have several different data policies. According to CableTV.com and other industry resources, providers with data cap policies for some types of services include AT&T, Cox, Hughesnet, Mediacom, Rise Broadband, Sparklight, Viasat and Xfinity.
Several ISPs don't impose any data caps. These providers include Astound Broadband, Breezeline, Brightspeed, CenturyLink, EarthLink, Frontier, Google Fiber, Optimum, Quantum Fiber, Spectrum, Starlink, T-Mobile Home Internet, Verizon Fios Home Internet, Windstream, WideOpenWest and Ziply Fiber.
Data caps limit the amount of data that can be used in a given time period. Learn 4 tips for network capacity planning and provisioning for the enterprise.
