information asset
What is an information asset?
An information asset is a collection of knowledge or data that is organized, managed and valuable. An organization needs to classify, manage the lifecycle of and control access to information assets.
How to identify information assets
As Francis Bacon said, "Knowledge is power." If an organization's knowledge has power, it also has value. By classifying and managing valuable knowledge and data, it becomes an information asset.
How can an organization identify an information asset? A simple test is if the information has an associated cost to acquire. If an information asset were to be lost or leaked, it would be damaging to the organization.
An information asset needs to be organized into a distinct unit. This enables it to be classified and tracked. Generally, information that exists only in someone's head cannot be considered an asset.
Different types of information can be put together into a single asset if they are related. For example, all the text documents, spreadsheets and slide decks related to one project may be treated as a single information asset.
Broadly speaking, any document created by an organization could be considered an information asset. Some examples of information assets would be program source code, research documents, strategic slide decks and databases.
Some data has negative value. This data may need to be kept for legal or operational reasons but cannot be used constructively by the organization. It could be a liability if the information were to be leaked, though. This might be considered a toxic asset. Some examples might be historical tax information or customer data.
Classifying, managing and protecting information assets
Not all information assets are equal in value. For example, an employee office schedule leaking to the public is not as critical as a corporate acquisition plan leaking. Customer or human resources data leaking could have legal repercussions. A single employee losing one document is a minor issue, while a major database with decades of organizational data being lost could have a severe business impact.
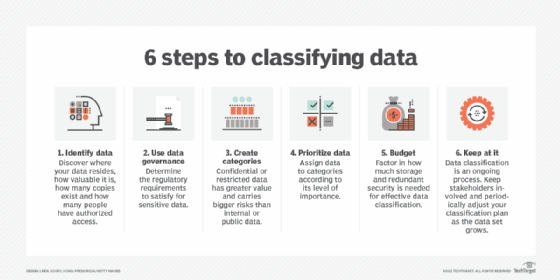
Information assets can, therefore, be classified by their sensitivity and how critical their loss would be. Some information assets may be confidential and require access control to limit access. Information assets critical to organization functioning may need to be backed up and be part of a business continuity plan.
An information asset can be digital or physical. Organizations can maintain physical assets in a filing system or with asset tracking tags. Particular attention needs to be paid to data retention for physical assets.
Enterprise document management (EDM) systems can be used to track information assets. EDM can be used to tag and classify information assets. EDM can limit access to authorized parties and prevent data leaks by tracking data access.

Ransomware gangs are a threat to information assets. They can encrypt important data, preventing access to it. Increasingly, they are beginning to extort organizations by copying this data and spreading it publicly. These threats show the importance of controlling access to information assets in the organization.
Information security standard International Organization for Standardization (ISO) 27001 involves managing all assets in an organization. It covers both physical assets and data assets. In order to be fully compliant with ISO 27001, all information assets would need to be accounted for. This may require tracking documents as they are checked in and out of an EDM system. Employee devices, such as desktops, laptops and mobile devices, would need to be tracked and protected against tampering.
Learn why asset management software is more important than ever, explore five key benefits of enterprise asset management software and see six benefits of asset performance management.
