data residency
What is data residency?
Data residency refers to the physical or geographic location of an organization's data or information. Similar to data sovereignty, data residency also relates to the data laws or regulatory requirements imposed on data based on the data laws that govern a country or region in which it resides.
Organizations that use cloud computing store data in the country where the data originated or beyond its borders. However, when businesses deliver hosted services over the internet, they can create data residency concerns. Often, cloud computing customers are unaware of their data's physical location. So, as cloud providers store data globally across different data center locations, users need to be aware of their data's local residency laws and regulations.
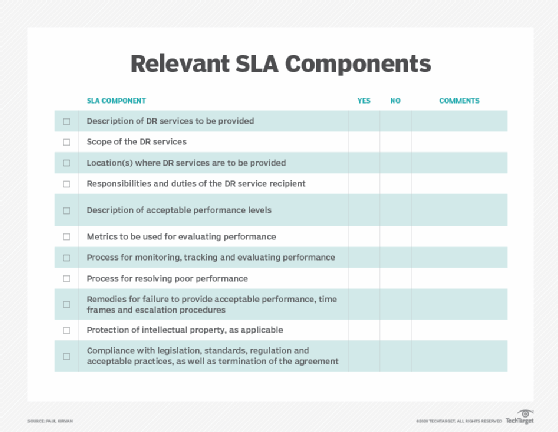
To understand which data laws and regulations govern their data, users need to know where their cloud provider's data centers are located and research the data residency policies for each respective location. Additionally, cloud users should make sure that their service-level agreements (SLAs) with cloud providers establish where their data can and cannot be stored.
What are data residency requirements?
In most parts of the world, businesses operate under local data regulations that dictate how the data of a nation's citizens or residents must be collected, cleaned, processed and stored within its borders. The primary reason enterprises choose to store data in different locations is often related to regulations, data policies and taxes.
However, companies are allowed to transfer data after complying with local data protection and privacy laws. In this scenario, businesses must notify users and get their consent before obtaining and using their information.
How do data residency, data sovereignty and data localization differ?
Data residency, sovereignty and localization are terms that often cause confusion because of some overlap. However, businesses must understand the differences in these terms to avoid significant fines for regulatory violations.
Data residency refers to where the data is physically and geographically stored. Data sovereignty is not just about where the data is stored but also about the laws and regulations that govern the data at the location where it is physically stored. In the case of data sovereignty, various data subjects will have different privacy and security regulations depending on the location of the data centers where the information is stored.
In contrast, data localization demands that all data generated within a country's borders remains within them. Unlike data residency and data sovereignty, data localization is consistently applied to the creation and storage of personal data.
Many government policies and regulations deal specifically with data privacy and residency issues. The Health Insurance Portability and Accountability Act (HIPAA) is a data privacy and security law designed to protect medical information. Payment Card Industry Data Security Standard (PCI DSS) is a set of policies to secure credit and debit cardholder information.
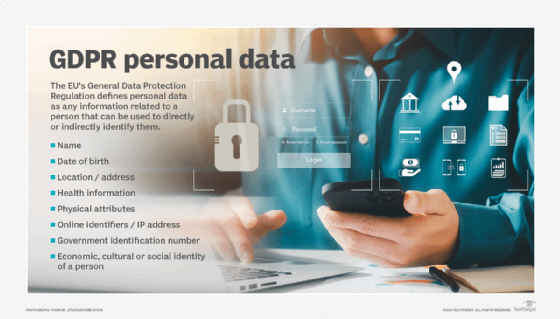
Outside of the United States, data residency and privacy regulations include Germany's Federal Data Protection Act, the United Kingdom's Data Protection Act and the European Union's (EU) General Data Protection Regulation (GDPR). However, GDPR data residency requirements only regulate the processing of EU residents' personal data, a critical component of the EU's privacy and human rights laws.
The EU's data residency laws do not have specific localization requirements. However, many businesses in the region take steps to ensure data localization of the regulated data before transferring data out of its country of origin.
Organizations can use cloud data encryption tools to protect data from unwanted access and ensure data residency compliance regardless of its geographic location. Cloud encryption services transform user data into ciphertext before storing it in the cloud.
In April 2015, the Object Management Group created the Data Residency Working Group to study data residency issues. Some issues investigated include controlling and documenting data within cloud computing environments, automated source code data protection measures and unified component models for distributed, real-time and embedded systems.
What is data residency in Azure?
Microsoft Azure is a leading cloud services provider offering tools to most global regions with multiple scales and data residency options to help bring apps close to their users. However, according to Microsoft's data policy, users maintain complete ownership of their data. This includes the personal content and other data provided by the users to be hosted and stored in Azure services. Users can also control when and where they want to deploy solutions in additional geographies or to replicate data.
What is a redacted data residency model?
In a redacted data residency model, businesses can only store a designated subset of protected data within the country. Flow control is not allowed, and companies cannot copy, process, view or store data beyond national borders.
See also understand the principles of data residency, 3 steps to ensure data sovereignty in cloud computing and cloud data residency: addressing legal and regulatory risks.






