decompile
What is a decompile?
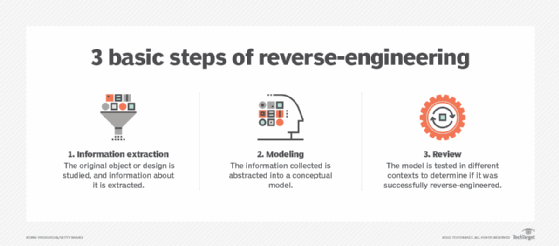
To decompile means to convert executable or ready-to-run program code -- sometimes called object code -- into some form of higher-level programming language that humans can easily understand. Decompilation is a type of reverse-engineering that performs the opposite operations of a compiler. Decompilation was first used in the 1960s to facilitate the migration of a program from one platform to another.
To convert a programming code into a working program, it must first be compiled -- i.e., converted into a series of binary bits or digits (that is, 1s and 0s) that can be understood by the computer. This operation can be reversed by decompiling the final program (which is why decompiling is described as a type of reverse-engineering).
The tool used to decompile software code and translate it into a human-understandable form is known simply as a decompiler.
A decompiler is a computer program that receives input in the form of an executable file. If the file's source code is lost or corrupted for some reason, the decompilation process attempts to recover the code, or at least most of it. Unlike a compiler, whose recipient (or final user) is the computer, a decompiler's recipient is a human user.
A disassembler is a similar tool that translates object code into assembler language. It provides a "dump" of the machine code that makes a program work. Some reverse compilers are in fact disassemblers.
Why decompile?
There are many valid reasons to decompile source code, such as:
- to understand a computer program and the functionality of its code;
- recover the source code for archiving or updating;
- find viruses in the program and, thus, enhance its security;
- debug the program and correct errors;
- translate obsolete code;
- remove for legal purposes code restrictions (like passwords), copy protection or time limits; and
- make software compatible with third-party components and enable interoperability.
Decompilers can also be used for unethical and/or illegal reasons, especially to break a software's copyright protection and to use it without permission.
Decompilation challenges
Decompilation can rarely reconstruct the original source code perfectly or completely. One reason is successful decompilation depends on available code information. It also depends on the reverse engineer's skills, expertise, and the tools and techniques they use.
The meaningful names given to variables and Functions by programmers to make them easily identifiable are not usually stored in executable files, and are therefore not always recovered in decompiling. In short, because the source code rarely includes such "identifiers," perfect decompilation almost never happens.
As code complexity increases, decompilation becomes even more difficult. It is also not possible to decompile all programs. Furthermore, it is not easy to separate data and code because both are represented similarly in most current computer systems.
Is it legal to decompile code?
Decompilation is sometimes used unethically without the permission of the copyright holder to reproduce source code for reuse or adaptation. The decompilation of copyrighted software is illegal in many countries, although the specifics differ from country to country.
In the U.S., for example, copyright laws don't fully restrict decompilation. The Digital Millennium Copyright Act (DMCA) allows reverse-engineering, if a person has lawfully obtained a right to use a copy of a computer program, only to identify and analyze its elements to achieve interoperability with other programs. However, decompiling a program to circumvent a system that controls access to copyrighted work is considered illegal. Similarly, the EU also allows decompilation for some uses, including interoperability.
Programs can be designed to be resistant to decompilation through the use of protective means such as obfuscation.
Popular software decompiler tools
Several decompiler, disassembler and reverse-engineering tools are available to use for legal purposes. Many of these tools are open source or free, while others are commercial and not free.
Some of the most popular tools are:
- IDA Pro. Interactive disassembler with a built-in command language
- Hex-Rays Decompiler. Plugin that converts native processor code into a more readable, C-like version
- ClassInformer. For use on binaries built by Visual Studio
- CFF Explorer. Includes tools for portable executable (PE) editing, including a disassembler
- Hiew. Binary file editor with a built-in disassembler
- PEiD. Analyzes entropy to detect if an application is packed
