degrees of freedom (mechanics)
What is degrees of freedom (mechanics)?
In mechanics, degrees of freedom (DOF) is the number of independent variables that define the possible positions or motions of a mechanical system in space. DOF measurements assume that the mechanism is both rigid and unconstrained, whether it operates in two-dimensional or three-dimensional space. The number of degrees of freedom is equal to the total number of independent displacements or aspects of motion.
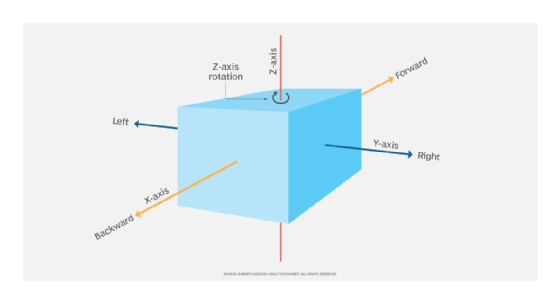
Degrees of freedom applies to two types of motion: translational and rotational. Translational motion refers to movement that is both linear and non-rotational. Rotational motion is just the opposite. An unconstrained, rigid mechanism in two-dimensional space (planar space) can potentially have three independent degrees of freedom: two translational and one rotational.
For example, Figure 1 shows a block in a planar space. The block, which can represent any rigid, unconstrained mechanism, can move linearly forward and backward along the x-axis, or it can move left or right along the y-axis. Both types of movements are considered translational motion. The block can also rotate around the z-axis, which means that it also supports rotational motion. However, the block cannot rotate around the x-axis or y-axis, nor can it move linearly up and down the z-axis.
A mechanism in three-dimensional space can support up to six degrees of freedom: three translational and three rotational. Figure 2 shows the same block in a three-dimensional space, but it now includes one more translational motion and two more rotational motions.
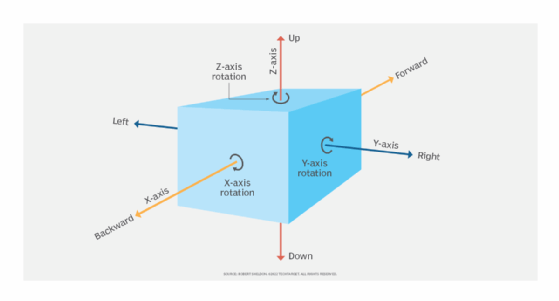
Because it is in a three-dimensional space, the block can move linearly along all three axes, and it can rotate around all three axes.
- The block can move forward or backward along the x-axis, and it can rotate around the x-axis. In nautical terms, these motions are referred to as surge and roll, respectively.
- The block can move left or right along the y-axis, and it can rotate around the y-axis. In nautical terms, these motions are referred to as sway and pitch, respectively.
- The block can move up or down the z-axis, and it can rotate around the z-axis. In nautical terms, these motions are referred to as heave and yaw, respectively.
Given the use of nautical terms, it's easy to see how a ship can have six degrees of freedom. It exists in a three-dimensional space, and it is capable of all three translational motions and all three rotational motions.
Not all mechanisms in a three-dimensional space have six degrees of freedom. A typical office chair, for example, has four degrees of freedom: three translational and one rotational. The chair can move linearly in any direction, including up and down (to a limited degree), and it can turn in circles around the seat's axis.
Degrees of freedom in robotics
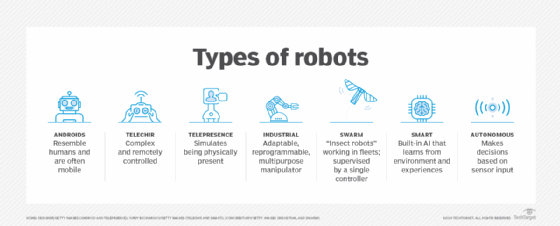
The term degrees of freedom is widely used to define the motion capabilities of robots, including androids (humanoid robots). In this context, the term generally refers to the number of joints or axes of motion on the robot.
Consider a robotic arm built to work like a human arm.
- The shoulder can rotate in any direction, giving it three degrees of rotational freedom.
- The elbow can bend in only one direction, resulting in one degree of rotational freedom.
- The wrist can rotate in any direction, adding three more degrees of rotational freedom.
This type of robotic arm is considered to have seven degrees of freedom. However, a robot can potentially have more than seven. An android, for example, will likely have two arms, two legs and one head, each with its own degrees of freedom.
Fully functional androids and multi-legged mobile robots can have over 20 degrees of freedom. For example, the Nao robot from SoftBank Robotics is an intelligent android designed for the consumer market. The robot, which looks like a large space-age doll, offers 25 degrees of freedom.
See also: mathematical symbols, robotics, uncanny valley, mobile robot, social robot, probabilistic robotics, smart robot, robot economy, mechatronics, 3D modeling
