
CRM (customer relationship management)
What is CRM (customer relationship management)?
CRM (customer relationship management) is the combination of practices, strategies and technologies that companies use to manage and analyze customer interactions and data throughout the customer lifecycle. The goal is to improve customer service relationships and assist with customer retention and drive sales growth.
CRM systems compile customer data across different channels and points of contact between the customer and the company. These can include the company's website, telephone, live chat, direct mail, marketing materials and social networks. CRM systems can also give customer-facing staff detailed data on customers' personal information, purchase history, buying preferences and concerns.
Why CRM benefits businesses
The benefits of CRM systems apply to all types of organizations, ranging from small businesses to large corporations. They include the following:
- Enhanced customer service. Having customer information, such as past purchases and interaction history, easily accessible helps customer support representatives provide better and faster customer service.
- Trend spotting. Collection of and access to customer data let businesses identify trends and insights about their customers through reporting and visualization features.
- Automation. CRM systems can automate menial, but necessary, sales pipeline and customer support tasks.
Components of CRM
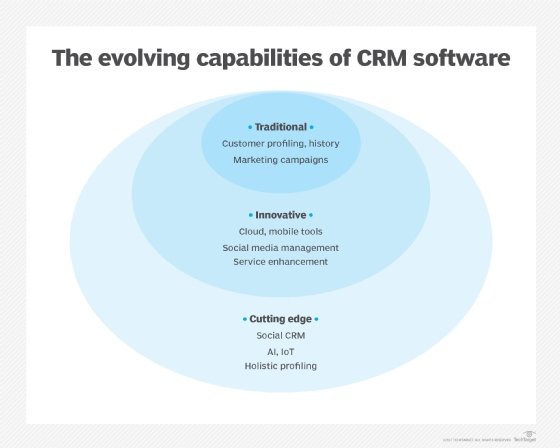
At the most basic level, CRM software consolidates customer information and documents it into a single CRM database. This lets business users more easily access and manage that information.
Over time, additional functions have been added to CRM systems to make them more useful. Some of these functions include recording various customer interactions over email, phone, social media and other channels. Automation capabilities have been added to many CRM systems, automating various workflow automation processes, such as tasks, calendars and alerts. Other CRM features enable managers to track performance and productivity based on information logged within the system.
Common components and capabilities of CRM systems include the following:
- Marketing automation. CRM tools with marketing automation capabilities automate repetitive tasks to enhance marketing efforts at different touchpoints in the lifecycle for lead generation. For example, as sales prospects come into the system, it might automatically send email marketing content with the goal of turning a sales lead into a full-fledged customer.
- Sales force automation. These tools track customer interactions and automate certain business functions of the sales cycle. Sales force automation tools target sales functions where it's necessary to follow leads, obtain new customers and build customer loyalty.
- Contact center automation. Designed to reduce tedious aspects of a contact center agent's job, contact center automation includes prerecorded audio that assists in customer problem-solving and information dissemination. Various software tools that integrate with the agent's desktop tools can handle customer requests to cut down the length of calls and streamline customer service processes. Automated contact center tools, such as chatbots, can improve customer user experiences.
- Geolocation technology, or location-based services. Some CRM systems include technology that creates geographic marketing campaigns based on customers' physical locations, sometimes integrating with popular location-based Global Positioning System (GPS) apps. Geolocation technology is also used as a networking or contact management tool to find sales prospects based on a location.
- Workflow automation. CRM systems help companies optimize business processes by streamlining mundane workloads, enabling employees to focus on high-level and creative tasks that help them close deals.
- Lead management. Sales leads can be tracked through a CRM platform, enabling sales teams to input, track and analyze data for leads in one place.
- Human resources (HR) management. CRM systems help track employee information, such as contact information, performance reviews and benefits within a company. This enables the HR department to more effectively manage the internal workforce.
- Analytics. CRM analytics examines user data to create targeted marketing campaigns that can increase customer satisfaction rates.
- Artificial intelligence (AI). AI technologies, such as Salesforce Einstein, have been built into CRM platforms to automate repetitive tasks, identify customer-buying patterns and predict future customer behaviors.
- Project management. Some CRM systems include features to help users track client project details, such as objectives, strategic alignment, processes, risk management and progress.
- Integration with other software. Many systems integrate with other software, such as call center and enterprise resource planning systems.
Types of CRM technology
The four main vendors of CRM systems are Microsoft, Oracle, Salesforce and SAP. These four tend to be the best systems for large companies; other providers are popular among small to midsize businesses. The types of CRM technology offered are as follows.
Cloud-based CRM
CRM that uses cloud computing is also known as software as a service or on-demand CRM. Data is stored on an external, remote network that employees can access anytime and anywhere there is an internet connection. Sometimes, a third-party service provider oversees system installation and maintenance. The cloud's quick and easy deployment capabilities appeal to companies with limited technological expertise or resources.
Data security is a primary concern for companies using cloud-based systems, as the company doesn't physically control the storage and maintenance of its data. If the cloud provider goes out of business or is acquired by another company, an enterprise's data could be compromised or lost. Compatibility issues can also arise when data is initially migrated from a company's internal system to the cloud.
Companies might consider cloud CRM as a cost-effective option. Vendors typically charge the user on a subscription basis and offer the option of monthly or yearly payments. However, cost might still be a concern because paying subscription fees for software can be more costly over time than investing in an on-premises model.
Popular cloud-based CRM providers include HubSpot, Salesforce, Zendesk and Zoho.
On-premises CRM
On-premises CRM puts the onus of administration, control, security and maintenance of the database and information on the company using the CRM software. With this approach, the company purchases licenses upfront, instead of buying yearly subscriptions from a cloud CRM provider. The software resides on the company's servers, and the user assumes the cost of any upgrades. It also usually requires a prolonged installation process to fully integrate a company's data. Companies with complex CRM needs might benefit from an on-premises deployment.
Many cloud-based providers, such as Aptean and Salesforce, also offer on-premises versions of their CRM software.
Open source CRM
An Open Source CRM system makes source code available to the public, enabling companies to make alterations at no cost to the company using the system. Open source CRM systems enable the addition and customization of data links on social media channels, assisting companies looking to improve social CRM practices.
Platforms such as Bitrix24, OroCRM, SugarCRM and SuiteCRM offer alternatives to the proprietary platforms from Salesforce, Microsoft and other vendors. Adoption of any of these CRM deployment methods depends on a company's business needs, resources and goals, as each has different costs associated with it.
CRM examples in practice
Examples of CRM use vary by the type and purpose of the specific CRM system. Common ones include the following.
Contact center
Traditionally, data intake practices for CRM systems have been the responsibility of salespeople and marketing departments, as well as contact center agents. Sales and marketing teams procure leads and update the system with information throughout the customer lifecycle. Contact centers gather data and revise customer history records through service calls and technical support interactions.
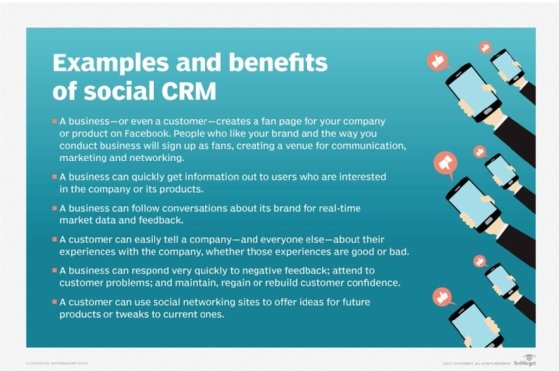
Social CRM
Social media in CRM involves businesses engaging with customers directly through social media platforms, such as Facebook, Twitter and LinkedIn. Social media presents an open forum for customers to share experiences with a brand, whether they're airing grievances or promoting products.
To add value to customer engagement on social media, businesses use various social CRM tools that monitor social media conversations. These tools look for everything from specific mentions of a brand to the frequency of keywords used to determine a company's target audiences and which platforms they use. Other tools are designed to analyze social media feedback and address customer queries and issues.
Companies are interested in capturing customer sentiments, such as the likelihood they recommend products and overall customer satisfaction to develop marketing and service strategies. Companies try to integrate social CRM data with other customer data obtained from sales and marketing departments to get a single view of the customer.
Another way in which social CRM adds value for companies and customers is through customer communities, where customers post reviews of products and engage with other customers to troubleshoot issues and research products in real time. Customer communities provide low-level customer service for certain kinds of problems and reduce the number of contact center calls. These communities also provide new product ideas and feedback that companies can use in lieu of focus groups.
Mobile CRM
CRM applications built for smartphones and tablets have become a must-have for sales representatives and marketing professionals who want to access customer information and perform tasks when they aren't physically in their offices. Mobile CRM apps take advantage of features that are unique to mobile devices, such as GPS and voice recognition capabilities, to give sales and marketing employees access to customer information from anywhere.
Business-to-business practices
A CRM system in a business-to-business (B2B) environment helps monitor sales as they move through the sales funnel, enabling a business to address any issues that might come up during the process. CRM strategies in the B2B market give sales reps more visibility into leads, increasing efficiency throughout the sales process.
CRM challenges
For all the advancements in CRM technology, without the proper management, a CRM system can become little more than a glorified database in which customer information is stored. Data sets must be connected, distributed and organized so that users can easily access the information they need.
Companies might struggle to achieve a single view of the customer if their data sets aren't connected and organized in a single dashboard or interface. Challenges tracking the customer journey also arise when systems contain duplicate customer data or outdated information. These problems can lead to a decline in customer experience (CX) because of issues such as long wait times during phone calls and improper handling of technical support cases.
CRM systems work best when companies clean their existing customer data to eliminate duplicate and incomplete records before they supplement CRM data with external sources of information.
Will CRM be affected by AI?
CRM systems benefit from nascent trends and technologies in the AI space. Sales forecasting is one area that will benefit. Predictive AI algorithms in a CRM system can analyze historical data about customers and companies to predict future sales outcomes and future market trends to shape an organization's decision-making.
AI also provides automation for routine and repetitive tasks, such as data entry and follow-up emails to customers or potential customers. Advanced chatbots and sentiment analysis capabilities help synthesize information from interactions to better identify customer needs and inform future interactions.
HubSpot and Salesforce are examples of enterprise-grade CRM providers that are integrating up-to-date AI capabilities into their platforms. It remains to be seen how quickly smaller organizations and startups with CRM offerings and significantly less resources will be able to integrate similar AI features. Still, these AI enhancements will become more commonplace in the future.
CRM tools are required to manage customer data, but it also helps for businesses to have a strategy that prioritizes CX. Learn some tips for building a valuable CX experience.






