user experience
What is user experience design?
User experience (UX) design is the process and practice used to design and implement a product that will provide positive and relevant interactions with users. UX design, sometimes called user-centric or user-centered design, involves all aspects of product development and design, including the following:
- packaging and branding;
- installation and setup; and
- operation, usability and performance.
In short, UX design helps designers create products that are both practical and usable. UX design addresses the following six major areas:
- Usefulness. The product must fill a practical need for the user.
- Desirability. The product must use attractive and consistent aesthetics, such as visual design.
- Usability. The product must be simple to use and provide a familiar suite of features and functions.
- Accessibility. The product must be usable by everyone, including users with disabilities.
- Supportability. The product must be well-supported so that users can resolve problems quickly and easily.
- Credibility. The product must be trustworthy -- such as from a reputable company or implementing careful security.
While UX design is often associated with software or digital services design, the term is also readily applied to any physical product or construct.
Why is UX design important?
The user experience is a critical consideration in attracting and retaining users or customers.
Consider any physical or digital product. If users don't need the product, don't enjoy using the product or can't reasonably use the product without undue difficulty, those users will simply stop using the product and adopt a competitor's product instead. This can adversely affect the reputation and revenue of the business.
Conversely, an effective and reliable product that fills a clear need and offers good performance and support can drive business revenue, boost business reputation and enhance user loyalty to the business and its brand.
Because users provide the business revenue derived from products or services, a good user experience can actually be a matter of survival for most businesses. Consequently, ignoring or taking shortcuts around UX issues -- such as usability testing or user acceptance testing -- can be a perilous decision for project managers and product stakeholders.
Finally, UX design should be treated as a dynamic part of any product design. UX design decisions made today aren't permanent, and user experience strategies are regularly updated and modified as market demands, competitive forces, user expectations and enabling technologies evolve over time. User research and user experience testing are often employed to periodically reassess UX design choices.
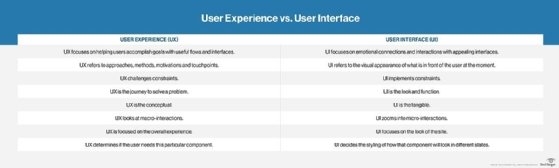
What are the differences between UX and UI design?
The terms user interface (UI) and UX are often used interchangeably. This is a common mistake because the UI is the primary mechanism for user interaction with a product and is central to the overall user experience.
In practice, UI design is a subset of UX design. User experience design involves all aspects of a product and its behavior, while user interface design focuses on the look, shape and other user interactions with that overall product.
Consider the analogy of a hammer where the handle is the UI -- the point at which a user interacts with the product. However, the UX might also involve the use of an ergonomic handle shape and an appealing dark nonslip handle coating, which make the hammer more comfortable and safer to use. The UI and UX are inexorably intertwined.
Consider a software product with a menu-based UI. Even though the software product may fill a practical need and operate flawlessly as part of the overall UX, a software UI with cumbersome, inconsistent, poorly defined, multilayered menus or visually confusing button placement can have a negative effect on the user experience.
What does a UX designer do?
In general terms, a UX designer plays a central role in product design and is typically responsible for the user's overall product or service satisfaction. A UX designer can often approach the role as a customer advocate by looking for new and innovative ways to improve the customer's experience through the product or service using the following why, what and how considerations:
- Why addresses user motivations in selecting and using a product.
- What addresses the features and functionalities of the product.
- How addresses the accessibility and aesthetics of the product.
In more specific terms, UX designers perform a variety of design-related tasks. They are as follows:
- Understand the business, the brand and the user base, as well as the problem the product is intended to solve.
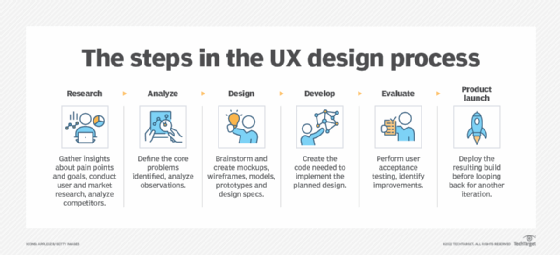
- Research users to identify behaviors, needs, goals and challenges through tools such as surveys, interviews, focus groups and user acceptance testing.
- Use that understanding and research to visualize how user workflows should operate; for example, what does a clear and concise software menu or interface look like?
- Design the product using mockups, wireframes, models or other prototypes to give other stakeholders and designers a clear picture of the product, including the UI.
- Test the product to validate user interactions and acceptance; make changes to the design as needed to optimize the design for user experience.
UX designers employ a wide range of technical and interpersonal skills to accomplish their tasks successfully. Technical skills can involve strong research, data organization and prototyping skills, as well as basic visual design and coding skills for software development environments. Interpersonal skills include strong communication, collaboration and critical thinking.
How to become a UX designer
There are no formal requirements to become a UX designer. Most engineers and developers start with a basic technical degree and become involved and gain experience in UX concepts through their day-to-day projects.
Professionals who seek a dedicated UX design role can do the following:
- Take advantage of educational opportunities to study UX concepts and tools.
- Become involved with projects that use UX design skills and perhaps volunteer as a member of a product design/UX team.
- Gain skills and experience in UX design.
- Develop a portfolio of successful UX designs.
- Apply for related UX design jobs inside or outside of the company.
UX roles can go by many names, including product designer, service designer, user interaction designer and UX designer. Smaller organizations typically provide a broader scope of UX roles and responsibilities, while larger organizations might expect greater levels of specialization from UX designers such as research, analysis or engineering. Senior UX designers can often move into management roles such as project manager or UX director.
History of UX
The user experience is basically the notion of how well people and machines interact. Thus, UX as a discipline can trace its roots back to the 20th century industrial era where factories emerged with people to operate factory production machines -- think early automotive production plants. The ways that production equipment and factory workflows brought efficiency to manufacturing is often considered the precursor to UX.
Eventually, these traditional factory environments and workflows evolved to improve working conditions for people, bringing concepts of human factors, safety and ergonomics into the design of equipment and devices -- designing systems and workflows that better fit human capabilities and behaviors.
As computer technology emerged and evolved, the ideas of UX translated into early computer designs. These early innovations included the graphical user interface (GUI) and the mouse -- physical and virtual mechanisms still standard today. The actual term user experience is thought to have originated in the 1990s when cognitive psychologist Donald Norman joined Apple with the title user experience architect. Norman's book, The Design of Everyday Things, is still standard reading for UX studies.
By the 1990s, the field of human-computer interaction emerged, blending fields of GUIs, cognitive sciences and human-centric design concepts to refine and expand what UX entails. As technology introduces devices such as PCs, tablets and smartphones, the role and importance of UX in technology continues to expand.
Learning how an application is performing is vital to understanding the effectiveness of the software development team, as well as gauging user satisfaction. Examine which metrics organizations should track to measure these key performance indicators.






