contextual marketing
What is contextual marketing?
Contextual marketing is an online marketing strategy model in which people are served with targeted advertising based on their search terms or recent browsing behavior.
By tying the ads users see to their demonstrated interests, advertisers hope to decrease user annoyance with online marketing and, simultaneously, increase clickthrough and conversion rates.
How does contextual marketing work?
Contextual marketing uses behavioral targeting to serve relevant or contextual ads to the target audience members based on their interests. To demonstrate this, we'll use an example.
Suppose a web user searches for mid-size car reviews on a mobile device, reads one or two reviews, and then reads an article about fuel-efficient models. Next, the user might visit a general news webpage and be shown ads for mid-size, hybrid vehicles.
To the user, the appearance of relevant ads -- on seemingly unrelated sites -- may seem like a pure coincidence or even synchronicity.
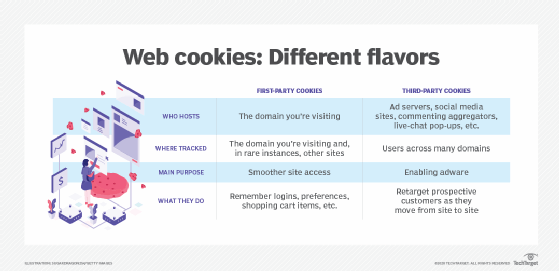
Each time the user performs a search, reads an article or clicks on an ad, a third-party cookie stored on the computer tracks the activity, which is used to create a behavioral profile of the consumer for marketing purposes.
It's also worth noting that contextual marketing is no longer limited to computer users. It can also be done for users visiting sites via their mobile device or cellphone.
Who implements contextual marketing?
Any website that displays ads can use or offer contextual marketing. Here are a few examples.
Search engines
An example of contextual marketing is Google's AdSense program, which generates an advertising profile for every search by using the terms entered to select an appropriate ad for that person.
News sites
Contextual marketing can also be used by news sites when serving ads. For example, a news site like The New York Times or Fox News can serve contextual ads to readers browsing their site.
Social media sites
Contextual marketing is also used on social media sites like Facebook, LinkedIn and Twitter to serve ads to users based on their browsing activity on the site. Often this activity can be search queries or keywords used in comments and open forums.
Retail sites
Online retailers also serve contextual ads to customers who have previously visited the retailer's website and searched for similar items.
For example, someone who has visited the Amazon website to look for a book on a particular topic might be shown an ad for a related DVD when revisiting the website.
The benefits of a contextual marketing campaign
Technology companies, online retailers, and travel companies are some of the most common contextual ad users. However, any business seeking a higher return on investment (ROI) for digital advertising can utilize contextual marketing.
Here are a few more benefits of contextual marketing.
- Higher click-through-rate. Contextual marketing shows the right content to customers based on their needs and wants. This increases the chances of customers engaging with digital advertising.
- Relevant content. Buyer persona refers to the ideal customer for a particular product. Once the buyer persona is defined, a company can look at customer demographics and online behavior to develop a marketing campaign.
- Higher revenue. Through targeted advertising, customers are shown marketing content for items that they are more likely to buy, thereby increasing companies' sales revenue. Due to this, e-commerce companies rely on this form of online advertising.
- Better customer experience. Contextual marketing ensures that customers see highly personalized ads that align with their interests. This results in a better user experience and enhanced customer satisfaction.
The challenges of a contextual marketing campaign
There are some challenges to overcome when it comes to contextual marketing. We review some of those challenges below.
- Privacy concerns. contextual marketing involves using cookies to track a customer's browsing activity. Some customers may not feel comfortable with this and find it to be an invasion of privacy. Thanks to recent legislation such as the General Data Protection Regulation and California Consumer Privacy Act, websites must get permission from users before collecting their information with cookies.
- Lack of standardization. Contextual marketing is still a relatively new field, and as such, there is no one-size-fits-all approach to implementation. This can make it difficult for businesses to determine the best way to use contextual marketing for their needs. Incorrect use can also raise the risk of noncompliance.
- Incorrect targeting. Because contextual marketing relies on analyzing a customer's browsing history, there is always the possibility that incorrect targeting will occur, resulting in ads being served for irrelevant websites.
Despite these challenges, when executed correctly, contextual marketing is still a powerful tool that offers great potential for businesses looking to improve ROI for their digital advertisements.
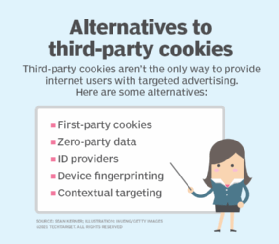
See also: ad blocker, click fraud, clickbait, context awareness, contextual computing, cost per sale, cost per engagement, social media analytics, web analytics, business metric, digital marketing and push notification.








