ghost imaging (disk imaging)
What is a ghost image?
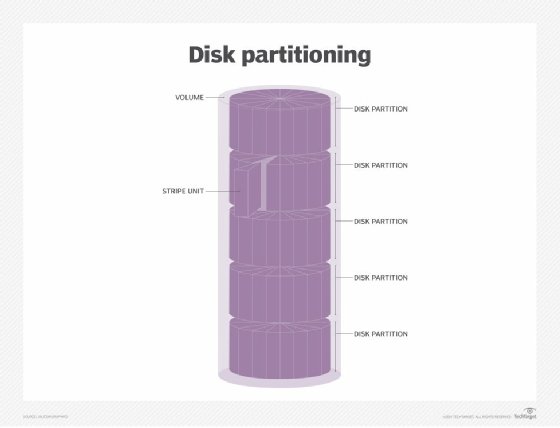
In computing, ghost imaging, also called disk imaging, is a data backup process that creates an image of a computer's hard disk drive (HDD), solid-state drive (SSD) or one of the drive's partitions. The image contains an exact copy of all the contents on the disk or partition. The contents can include the operating system (OS), configuration settings, master boot record, applications and their data, and user data -- everything needed to restore the disk or partition to its original state or to replicate it to another system.
A ghost image is typically saved as a single compressed file, which might also be encrypted. In some cases, the image is split into multiple files for easier storage, or it is not compressed. However, it is commonly created as a single compressed file, making it easier to work with the image and support various use cases. Because the image file can be so large, it is often saved to a file server or external storage device.
Ghost imaging and disaster recovery
Ghost imaging is often used to back up a computer disk so it can be easily restored to a point in time in case of drive failure or other disaster. Having a loadable image for a specific disk or partition makes disaster recovery (DR) easier and more efficient.
For example, if a PC fails for some reason, a ghost image can be used to restore the user's environment to that computer or a new computer. The image will contain the OS, configuration settings, applications and user data, making recovery much faster and easier than trying to configure the system from scratch. The same is true at the server level, except that the image also includes network and security settings.
Disk images are often generated as part of a larger backup strategy. If a computer fails, a backup image can be used to restore the computer within minutes and with minimal data loss. When the image is applied to a computer, the disk or partition is restored to a specific point in time, based on when the image was created. The greater the amount of time between image creation and computer failure, the greater the chances of data loss.
A disk image is usually thought to include all the content necessary to restore a drive or partition. However, disk imaging software can often generate multiple types of backups:
- Full image. The image includes all the content on the drive or partition, such as the OS, configuration files, applications, and user data. This is the most complete option, but it also takes longer to create the image and transmit it over a network, when compared to the other two options. In addition, a full image takes up more storage space than the other options.
- Differential image. The image stores only the changes that have been made on the drive or partition since that last full image was created. The image's size is often determined by the amount of time that occurred between when the differential backup image was created and when the full image was created. However, the file is still smaller than a full image and is quicker to create and transmit.
- Incremental image. The image stores only the changes that have been made on the drive or partition since the last full or incremental image was created. Incremental backup images are the smallest of the three options, and they're the quickest to create and transmit.
Differential and incremental images are always used in conjunction with full images. If differential and full images are used together, a complete restore requires the most recent full image and the most recent differential image (unless trying to restore a system to an earlier point in time). If incremental and full images are used together, a complete restore requires the most recent full image and all incremental images since the full image was created. For this reason, the restore process usually takes longer to complete than the other options.
In addition to disaster recovery, ghost imaging can also be used to replace or upgrade a drive. For example, if a user is moving from an HDD to an SSD, the user can create a disk image, upgrade to the new SSD, and then apply the image to the new drive. IT administrators can also use ghost imaging to create a disk image for deploying the same desktop environment to multiple computers. In this way, a single image can be applied to the computers simultaneously, greatly simplifying the deployment process.
Ghost imaging vs. disk cloning
Ghost imaging, or disk imaging, is sometimes referred to as disk cloning. However, the two differ in important ways. Although they can both create exact copies of a drive, the copies themselves are not the same. Disk cloning duplicates the drive's content and saves it to another drive, without creating an image file or compressing the contents. The new drive is, in effect, a clone of the original drive.
Because the contents are not compressed into a single file, restoring a drive from the clone is faster and easier than from a disk image. This approach can be especially beneficial when upgrading a drive or moving to a new system. However, users cannot clone a single partition, only the entire drive. In addition, they can save only one clone to the target drive. With ghost imaging, they can save multiple disk images to the same drive and, of course, you can clone partitions.
Ghost imaging also provides more flexibility for creating backups, in terms of granularity and image types. In addition, the disk image can be compressed to save space and speed up transfers, and it can be encrypted for security.
Ghost imaging can also be used to deploy multiple computers at the same time, even if they number in the hundreds or even the thousands. To prepare for such a deployment, administrators usually set up a master machine and create a ghost image of its drive. Next, they apply the image to the target computers and then run a customization process that gives each OS its own identity.
Pros and cons of ghost imaging
Organizations that need to configure multiple computers often turn to ghost imaging because it is much faster that setting up each machine individually, especially if there are many machines or the installation includes many applications. Disk imaging can save hours of setup time compared to loading and configuring the OS and applications one computer at a time. This approach also reduces errors in the deployment process.
However, administrators must exercise caution when using ghost imaging to update their managed computers (as opposed to deploying new systems). Disk images cannot be applied incrementally to a target computer. The new image will replace the entire drive or partition. As a result, all user data and customizations will be lost, so will any patches or software updates that were applied to that computer, unless they were also applied to the disk image.
Administrators should also keep in mind that a disk image is tied tightly to a specific hardware platform. If an organization manages many different types of target systems, the process of creating, managing and deploying images becomes increasingly complex. The more types there are, the greater the complexity.
Despite these challenges, ghost imaging is still an effective strategy for streamlining large-scale computer deployments consistently and reliably. Disk images might not be as simple to restore as cloned images when it comes to replacing a single disk, but they provide a reliable approach to system backups and DR, especially with their support for compression and incremental disk images. They also offer greater flexibility than cloning when it comes to creating the initial images.
History of ghost imaging
The term ghost imaging has been steadily giving way to disk imaging as the predominant label used to refer to this type of imaging. It is now the term most favored by vendors and others in the industry.
The use of the word ghost is a carryover from when the technology was first introduced by New Zealand-based entrepreneur Murray Haszard, when he developed the Ghost imaging tool in the mid-1990s. The term ghost was an acronym for "general hardware-oriented system transfer." Symantec Corp. acquired the tool in 1998, integrated it into its Norton product line and later renamed it the Symantec Ghost Solution Suite.
At the time, Ghost was the only readily available product that could easily create an image of an entire hard drive. Ghost could either save the image as a file on another drive or transfer the image to another hard drive, making the new drive an exact copy of the old one.
Broadcom acquired Symantec in 2019 and continues to offer the Ghost Solution Suite. There are also many other alternatives now available for imaging drives and partitions.
Examples of ghost imaging software and alternatives
Organizations take different approaches to creating ghost images, depending on the specific use case. For example, IT teams that support numerous desktops -- whether in the hundreds or the thousands -- need an imaging tool that can deploy images to the computers in batches and can also perform individual restores. In contrast, cloud providers are more likely to use the imaging tools that are part of the cloud software stack.
Unlike the early days of ghost imaging, there are now many products available for creating disk images. As already noted, Broadcom offers the Ghost Solution Suite, which is still sometimes referred to as the Symantec Ghost Solution Suite. In addition to being able to capture and deploy disk images, the suite supports scripted OS installations, user and application settings migration, driver to device mappings, and remote task execution and sequencing.
Although Ghost Solution Suite has a long history, IT teams are also turning to alternative products such as the following:
- Acronis True Image 2021.
- Macrium Reflect.
- EaseUS Todo Backup.
- StorageCraft drive imaging tools.
- NetApp for rapid image distribution.
- Open source tools such as Clonezilla, Partimage and the dd command-line utility.
In addition, cloud platforms such as OpenStack include image management capabilities, while major cloud service providers maintain their own imaging tools and libraries for use on their platforms. Windows, Linux and macOS also include tools for creating and restoring disk images.
Check out the seven critical backup strategy best practices to keep data safe and the advantages and disadvantages of cloud backup vs. traditional backup.







