distributor
What is a distributor?
A distributor is an intermediary entity between a producer of a product, or manufacturer, and a downstream entity in the distribution channel or supply chain. The downstream entity is typically a retailer or value-added reseller (VAR), but it can also be a wholesaler.
The distributor is an integral supply chain component, acting as an intermediary between the manufacturer and the downstream entity. The distributor bridges the gap between upstream and downstream entities while adding important services that help smooth the distribution process.
A distributor typically works with multiple manufacturers and multiple downstream entities. For each manufacturer, the distributor serves as an agent that enters into an agreement with the manufacturer to sell its products to retailers, VARs or wholesalers.
What is the difference between a distributor and a wholesaler?
Today's supply chains can include both distributors and wholesalers, and it's not always clear how they differ from one another. Some sources treat them as the same, but there are important distinctions in terms of the services they provide.
To appreciate these differences, it's important to understand how distributors and wholesalers fit into the overall supply chain ecosystem. The following diagram provides an overview of the basic supply chain execution and flow. Although this is a simplified representation of the process, it can help to conceptualize the main entities that make up a typical supply chain and how they fit together.
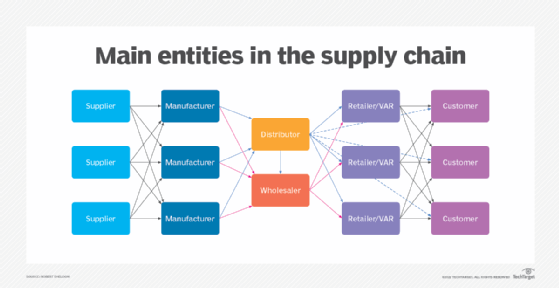
The distributor can play a pivotal role in moving products from the manufacturer to downstream entities. In a typical scenario, the supplier delivers materials to the manufacturer. The manufacturer uses these materials to build products, which it then ships to the distributor. The distributor delivers the products to the retailer or VAR, which then sells them to the customer.
Of course, supply chains are usually much more complex and might require supply chain management. Multiple suppliers can provide material for multiple manufacturers, a distributor can buy products from multiple manufacturers, and a retailer can sell products to multiple customers. A distributor might even sell products directly to customers.
In addition, the wholesaler might buy products directly from manufacturers -- as well as from other distributors -- and then sell the products to retailers. A manufacturer might also work with multiple distributors and wholesalers, and might even sell directly to retailers or customers.
Product delivery can also take forms other than what is reflected in the diagram, but it typically follows this pattern or something similar. This means that the wholesaler and distributor can both acquire products directly from the manufacturer, and then sell them to the retailer. It also means that the wholesaler and distributor roles are often confused.
Some of the confusion comes from the fact that a distributor performs some of the same functions as a wholesaler. However, the distributor's responsibilities are generally much more complex. In addition, the distributor takes a more active role with both the manufacturer and retailer, such as handling payment and procurement. The distributor also takes on more advanced capabilities. For example, manufacturers that lack the means to build out a channel strategy often outsource that work to distributors.
Distributors also frequently take a more proactive approach in educating resellers about new products by employing strategies such as presales training, roadshows or demos on behalf of manufacturers. Distributors might also provide services around the procurement process, including contract negotiation, marketing or product warranties. In contrast, wholesalers primarily focus on buying products in large quantities, breaking them into smaller units and selling them at profit.
See also: bullwhip effect, supply chain visibility, IT distributor, channel partner