document
What is a document?
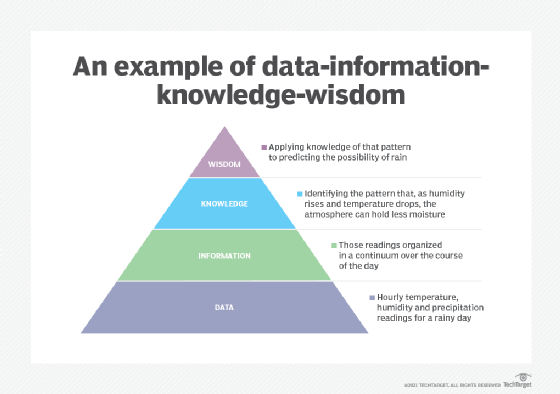
A document is a form of information that might be useful to a user or set of users. This information can be in digital and nondigital forms. Accordingly, a document can be either digital or nondigital. Different methods are used to store digital and nondigital documents.
A nondigital or paper document can be physically stored in a file cabinet, whereas an electronic or digital document is stored in a computer as one or more files. Digital documents can also be part of a database. Electronic document management programs deal with the management, storage and security of electronic documents.
How a document works
In general, a document refers to a permanent record of information that can be retrieved at some later time by a user. An entire document or individual parts in it can be treated as individual data items in a document storage system.
Here are some common examples of documents:
- letters
- sales invoices
- wills and deeds
- newspaper issues
- individual newspaper stories
- oral history recordings
- executive orders
- meeting minutes
- product specifications
- financial statements
- certificates
- licenses
- manuscripts
Documents are used by a variety of users in a wide range of fields, including the following:
- business
- law
- media
- education
- government
- politics
In pre-computer days, documents were usually written by hand or typed out on typewriters. These documents contained text, pictures, photographs, tables and other elements. Today, millions of documents are created and saved in digital format. However, physical or paper documents remain in use, and the idea of a "paperless" world seems improbable for now.
Digital documents
In the past, the term document referred only to handwritten or typed records of information. Now, the term also includes records created and stored in a digital format using computers and other digital devices such as tablets and smartphones.
When created with a computer application such as a spreadsheet or word processor, a document is a unit of saved work. Also, each digital document is saved as a file with a unique name that differentiates it from all other documents. A unique name also makes it easier for users to retrieve the document they need without having to waste time opening multiple documents.
The structure of a document
Most documents, especially those created in organizations or other professional settings, usually adhere to some conventions and standards that are universally accepted across that organization. Such adherence ensures that each new document is similar to previous documents in form and basic structure, bringing greater standardization and transparency into the organization's documentation workflows and ecosystem.
Generally, a document can take on any form or structure. For example, one document might contain only text, while another contains a mix of text, tables, images and other graphical elements. A third document might be a form, while another contains only charts or graphs.
Depending on the purpose and audience, a document can be unstructured or semistructured. A handwritten note or letter is a type of unstructured document, while newspapers, books and online blogs are all types of semistructured documents.
Document classification
There are many ways to classify documents, depending on the user or organization doing the classification. One popular method is to classify documents as public, private, and secret or classified.
Public documents are usually freely available to anyone who wants to access or read them. These include documents available on the web, newspapers, library resources, and information recorded and filed by public agencies, known as public records. In some countries, the access and use of public records is guided by law. In the United States, the law is called the Freedom of Information Act.
Private documents are only accessible to those users who are authorized to do so by a governing party. This party can be the original creator, a company's IT department, senior management, etc.
To protect private documents from being accessed by unauthorized users, they must be protected with appropriate safeguards. Physical private documents must be placed under lock and key, and the physical area must be guarded by security personnel and closed-circuit cameras. Digital documents can be protected by requiring all authorized users to provide a password to open or edit the document. These documents can also be encrypted or stored in a safe digital location that can only be accessed by authorized users with some kind of authentication, such as a password or multifactor authentication.
Secret or classified documents are typically restricted to a very small group of authorized users. These documents can belong to a company, a government, a military group, etc. Classified information belonging to a government is always protected via encryption, access control and security clearances. Further, access to these documents can be restricted by law, usually on a need-to-know basis. Finally, the mishandling, loss or compromise of classified documents -- whether done maliciously or inadvertently -- can incur criminal penalties on the responsible party.
Document vs. documentation
A document is not the same as documentation. A document is a record of some information that can be used as an authority or for reference, further analyses or study. Documentation refers to the ongoing process of creating, disseminating, managing and using documents.
The original term for collecting, preserving, organizing, describing, retrieving, reproducing and disseminating documents was bibliography. Today, all those activities fall under the description of documentation. This general term, which has been in use for more than a century, encompasses bibliography, information services, records management and document archiving.
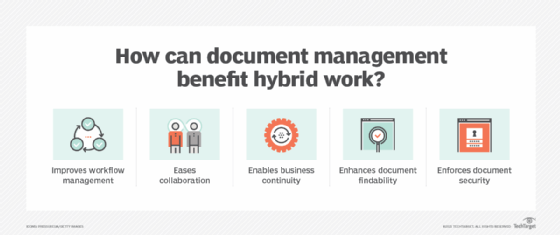
Electronic document management systems
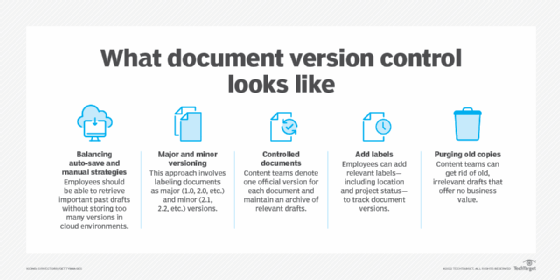
An electronic document management system (EDMS) is a type of software application to manage, secure and control electronic information and records. Most EDMS applications include functionalities such as the following:
- document versioning and history
- security and access control
- metadata capture
- secure document storage and retrieval
Some EDMS applications also include capabilities for records management, free text search and format conversion.

Organizations that create and manage a large number of documents can benefit from an EDMS. An EDMS can automate several document workflows and streamline access to information. It can also minimize duplication and help control access to documents. An EDMS can also automate document classification and help the organization comply with regulatory requirements related to records retention and security.
See also: document capture, document lifecycle, document sanitization, working draft, digital signature, document-oriented database
