enterprise document management (EDM)
Enterprise document management (EDM) is a strategy for overseeing an organization's paper and electronic documents so they can be easily retrieved in the event of a compliance audit or subpoena. The term originally referred to electronic documents that were created on a computer or paper documents that were scanned into a digital format. The meaning has broadened to include email, images, internal-facing documents -- such as company memos -- and external documents -- such as marketing or sales content.
In the context of regulatory compliance, enterprise document management must address the following:
- How long the business should retain documents;
- where the business should store documents;
- how to trace changes to the documents; and
- how to recover documents if a disaster occurs.
EDM also stands for electronic document management, engineering data management and electrical discharge machine.

How does enterprise document management work?
An enterprise document management strategy enables an organization to have a clear plan for its document management processes. An organization can use an EDM strategy to decide how to receive, process, review, store, retrieve and dispose of documents, as well as when the business should complete each step. The EDM strategy determines how the business should adjust the process to increase efficiency.
An organization can use a document management system (DMS) to create a single view of all an enterprise's documents and provide workflow tools to monitor and control modifications. A DMS enables businesses to capture a document by either scanning the physical document or downloading the digital version.
After scanning or downloading the document, the user can tag and index the document with keywords and metadata to enable users to quickly find them by keyword or full text search. The DMS organizes and places the document into a folder which appropriate employees can access. These systems also help ensure compliance by placing permission restrictions on certain documents and providing extra security.
Why is enterprise document management important?
Organizations have vast amounts of content in both paper and digital formats which users may store in public or private networks, shared drives, email or filing cabinets. Storing physical files comes with risks, however.
An EDM system reduces the need -- and associated expense -- of physical storage space. Unforeseen circumstances such as a fire or flood could potentially damage or destroy physical files. EDM systems typically include a data backup and disaster recovery plan, which provides businesses with a digital backup.
Organizations with files in multiple locations may also struggle to find the information that they need -- which is crucial for meeting legal requirements. EDM systems enable greater organization because all files are in one central location and users can easily find files using full-text search. By having all files in one digital location, users can access the files anywhere at any time.
EDM systems can integrate with various other applications including content management systems, Microsoft Office and Salesforce. Because users generally work in other tools within their workflow, it is important for the company's EDM system to be able to integrate with other applications easily.
There are many moving parts within a company, and an EDM system can help decrease bottlenecks and maintain an organized workflow. Version control and security within the EDM system make it easy for users to see who has access to certain documents and what changes other users made, which also ensures an organized workflow.
Differences between EDM and enterprise content management
EDM systems and enterprise content management (ECM) systems may sound similar, but they are not interchangeable terms. Businesses use an EDM system to organize paper and electronic documents and structured content; ECM systems enable organizations to capture, manage, store, preserve and deliver many additional types of content. ECM systems can organize paper and digital documents, but they can also handle other unstructured content such as audio and video files, social media, web pages, contracts, purchase orders, invoices and receipts.
EDM software aims to control the lifecycle of documents and ensure compliance. It focuses on more than storing files, but also on the tools and processes that businesses use throughout the lifecycle of content.
EDM is a subcategory of an ECM, and as a result, an ECM system may not function properly without an EDM system in place.
Types of document management systems
Document management systems are available as on-premises and cloud-based software.
An on-premises DMS enables businesses to use their own storage and perform their own maintenance. Businesses with an on-premises DMS are responsible for their own security. This type of DMS does not rely on the internet -- if the internet connection goes down, the DMS users can still access all their documents. The downside of on-premises DMSes is the large upfront costs, plus yearly expenses for software updates. Files in an on-premises DMS do not automatically save to the cloud, so backing up frequently is important.
A cloud-based DMS is accessible to the business online. The cloud provider typically charges a monthly or an annual fee which includes maintenance and software updates. Unlike the on-premises option, a cloud-based DMS is not as expensive and there are no large upfront costs. Users of a cloud-based DMS do not need to back up their files because they automatically save in the cloud. Users can access the cloud-based system wherever there is internet, however, if the internet connection fails, the user won't be able to access his or her files. Cloud-based DMSes depend entirely on the provider to keep the system up and running, while the on-premises system depends on the business's own IT resources.
Key features and components of a DMS
A DMS enables businesses to scan, store and retrieve business documents, but it has additional features that include:
- Document classification: enables users to categorize documents with metadata fields;
- keyword search: increases findability of content within the DMS;
- document viewing: enables users to see an image of the document without having to install its additional software;
- document editing: enables users to edit and create new versions of documents;
- version control: enables users to see all changes that other users make to a document and to recover older versions of documents;
- document sharing: enables users to share documents with internal or external users;
- security and audit: provide users with the ability to control which individuals or groups can access documents and what level of access they have; and
- document workflows: enable administrators to determine the workflow of documents throughout an organization.
Benefits of using a document management system
A document management system can improve the way an organization runs and how it deals with compliance and collaboration processes. Here are some benefits of DMSes:
- Compliance requirements for documents can be complex, but a DMS can reduce the risk of not meeting compliance requirements, such as HIPAA security and privacy guidelines. A DMS can automate certain functions, such as records retention schedules, so businesses are less likely to risk noncompliance.
- Document security. A business's documents are more protected when they are in a secure common repository. A DMS requires users to log in to the system, which provides an extra layer of security to protect content from cyber attacks and hackers.
- Improved retrieval and search. It is time-consuming to find documents, but a DMS can retrieve files by looking for a keyword or phrase. DMS can also index categories within a document or folder and enable an even smoother search.
- A DMS enables internal collaboration, as well as external collaboration with people with authorized access. Users can access documents from different sources from multiple locations. DMSes also offer version control, which is necessary for users to recover older versions of documents.
Top document management systems tools and vendors
There are many DMSes to choose from with varying capabilities. Here are some top options to consider:
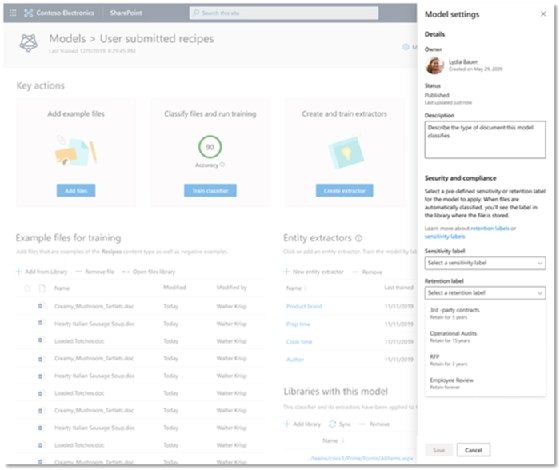
- Microsoft SharePoint
Microsoft SharePoint provides users with document management and collaboration capabilities. Businesses can create custom metadata fields that align with the organization's needs.
Pros:
- Easy to create, collaborate and edit documents
- Available separately or packaged with Microsoft Office 365
Cons:
- Many capabilities which may require more staff training
- M-Files
M-Files is a document management system that provides businesses with many features to organize, digitize paper records and automate workflow processes. M-Files offers on-premises, cloud-based or hybrid systems.
_mobile.jpg)
Pros:
- Easy-to-use interface modeled after Windows Explorer
- Integrates with Adobe Sign, which enables users to apply e-signatures to M-Files documents
- Integrates with Microsoft Office and Salesforce CRM
- Alerts users if there are duplicate documents
Cons:
- Pricing is unavailable online, so businesses must reach out to M-Files for a quote
- DocuWare
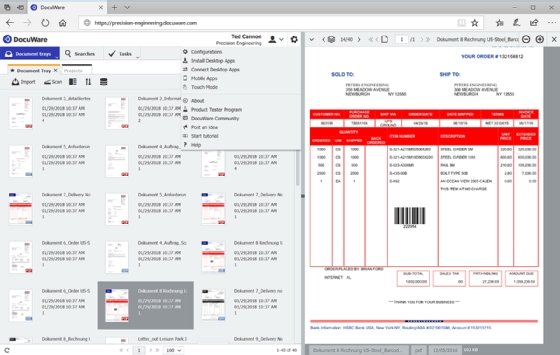
DocuWare is a cloud-based option for document management and workflow automation that enables businesses to transfer their digital and paper-based documents to a unified platform.
Pros:
- Provides mobile support
- Covers wide range of document tasks
Cons:
- Offers limited integrations
- Some features require a separate download from the application







