dual SIM phone
What is a dual SIM phone?
A dual SIM phone is a mobile phone, typically a smartphone, with the capacity to use two subscriber identity module (SIM) cards.
SIM cards are small cards inserted into phones that carry the user's mobile number, calling plan and other data that connects them to a specific cellular network. A dual SIM phone can, therefore, have two different numbers and networks on a single device.
Technical specifications for dual SIM phones
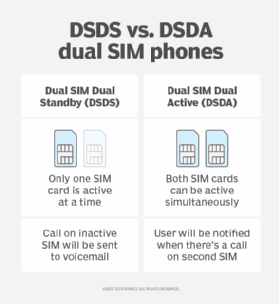
The foundation of a dual SIM phone lies in its ability to support and differentiate between two separate mobile networks simultaneously. There are two primary types of dual SIM implementations:
- Dual SIM Dual Standby (DSDS). Both SIM cards can receive calls or texts, but only one can be used for active data or calls at a time.
- Dual SIM Dual Active (DSDA). Both SIM cards can be active simultaneously, meaning you can receive calls or texts on one while using data or making a call on the other.
The demand for dual SIM phones
Historically, mobile phones were designed to support only one SIM card because of the limitations of early mobile communication technology.
As communication needs evolved and the global nature of business and personal life expanded, the industry saw a demand for more flexible mobile solutions. This led to the introduction of dual SIM technology, catering to the need for multiple networks on a single device.
Various manufacturers have recognized the demand for dual SIM functionality. Some examples of models in the market include offerings from major players like Samsung, Google, Motorola, Apple and OnePlus.
Benefits and drawbacks of a dual SIM phone
Dual SIM phones cater to a diverse range of user needs. For professionals, they offer the convenience of maintaining separate personal and business lines on a single device.
Travelers can seamlessly use their primary SIM in tandem with a local SIM, becoming digital nomads and sidestepping hefty international roaming charges. Additionally, there's the advantage of cost optimization, as users can take advantage of varying network promotions or plans available across different carriers.
However, the technology isn't without its considerations. Running two networks concurrently might lead to accelerated battery depletion. There's also the potential need for users to keep track of and manage contacts, call logs and messages across the two SIMs to avoid confusion.
Moreover, one must be wary of compatibility issues, particularly if the two SIMs function on distinct network frequencies or standards.
The future of dual SIM technology
With technological advancements, the concept of SIM cards is evolving. The introduction of the eSIM, or electronic SIM, hints at a future where physical SIM cards might become obsolete. This development could redefine the traditional understanding of dual SIM phones, as users could potentially switch between networks digitally without the need for physical SIM card slots.
The dual SIM phone, once a niche product, has found its place in the mainstream as communication needs have become more complex and varied. With its ability to offer flexibility and optimize costs, it caters to both professionals and everyday users alike.
As with any technology, its evolution is ongoing, and the industry will continue to adapt to the changing needs of the global mobile user base.
Read about seven key benefits of mobile device management for businesses and explore the key differences between mobile device management (MDM) and mobile application management (MAM). See how to successfully implement MDM for BYOD.
