digital divide
What is the digital divide?
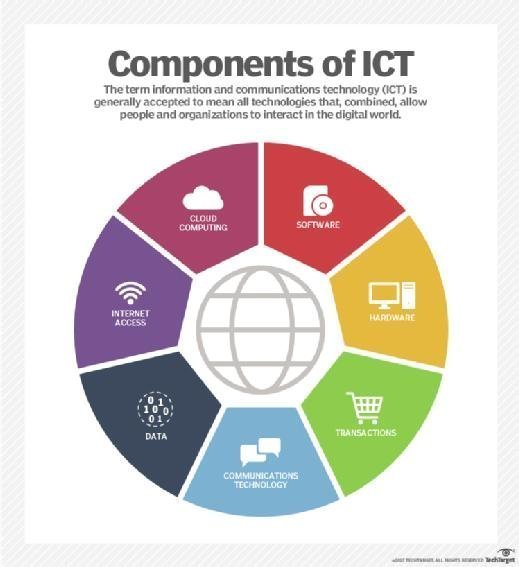
The digital divide is a term that refers to the gap between demographics and regions that have access to modern information and communications technology (ICT), and those that don't or have restricted access. This technology can include the telephone, television, personal computers and internet connectivity.
What are the origins of the digital divide?
Well before the late 20th century, the digital divide referred chiefly to the division between those with and without telephone access. After the late 1990s, the term began to be used mainly to describe the split between those with and without internet access, however, particularly broadband.
The digital divide typically exists between those in urban areas and those in rural areas; between the educated and the uneducated; between socioeconomic groups; and, globally, between the more and less industrially developing countries.
Even among populations with some access to technology, the digital divide can be evident in the form of lower-performance computers, lower-speed wireless connections, lower-priced internet use connections such as dial-up and limited access to subscription-based content.
What is the digital divide today?
According to studies and reports, the digital divide is still very much a reality today. According to a 2019 report, approximately 5 million rural American households and 15.3 million urban or metro areas still don't access broadband internet.
Meanwhile, a study by the Pew Research Center noted that 24% of adults with household incomes below $30,000 a year don't own a smartphone and 40% of those with lower incomes don't have home broadband services or a computer.
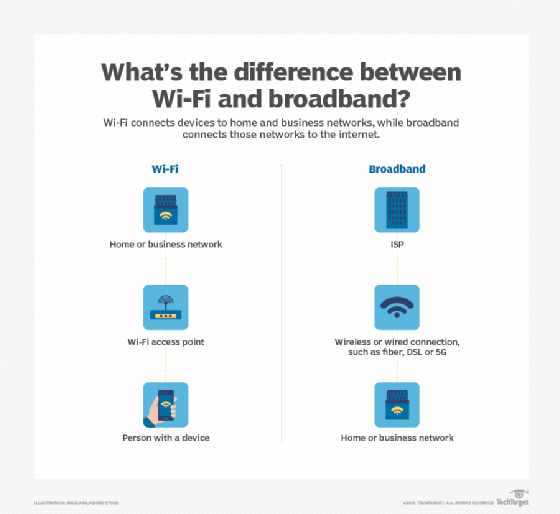
Globally, the digital divide in developing countries includes a lack of access to digital technology and internet service. It can also include a lack of accessibility to modern, high-quality new technologies such as mobile phones and Wi-Fi access.
Additionally, there is significant inequality across the globe in telecommunication bandwidth. For example, Venezuela and Paraguay feature some of the lowest digital access speeds followed by Egypt, Yemen and Gabon.
Bridging the digital divide
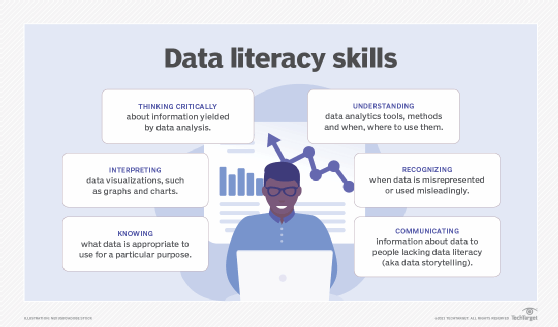
Proponents for bridging the digital divide include those who argue it would improve digital literacy, digital skills democracy, social mobility, economic equality and economic growth.
The United Nations, for example, has helped to raise awareness regarding the global digital divide through the yearly celebration of World Information Society Day. It has also created the Information and Communication Technologies Task Force in an effort to bridge the global digital divide.
However, overcoming the digital divide has not gotten easier, particularly in the aftermath of the COVID-19 pandemic.
A 2020 McKinsey report stated that learning loss will only increase as educators and students have taken to remote learning and internet usage from home is required by low-income families who may not have access to the right technology.
The reality of a separate-access marketplace is problematic because of the rise of services such as video on demand, video conferencing and virtual classrooms, which require access to the high-speed internet connections that those on the less-served side of the digital divide cannot access and/or afford.
To combat this, some nonprofit groups have taken to providing internet access and laptops to school districts and areas with internet users of a lower-income level.
