electrostatic field
What is an electrostatic field?
When two objects in each other's vicinity have different electrical charges, an electrostatic field exists between them. An electrostatic field also forms around any single object that is electrically charged with respect to its environment.
Electrostatic fields form as a result of the static electricity inherent in certain atomic particles. Most atoms are made up of three fundamental particles: protons, neutrons and electrons. The protons and neutrons form the nucleus, and electrons orbit the nucleus, usually at a considerable distance from the nucleus and each other, relative to the atom's size.
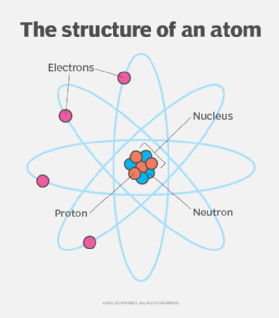
Protons and electrons have a measurable electrostatic charge. Neutrons do not. The amount of electrostatic charge is the same for both protons and electrons. The proton charge is considered to be positive (+), and the electron charge is considered to be negative (-).The positive and negative designations are somewhat arbitrary, but they're universally accepted within the scientific community, so that is the convention commonly used in describing a particle's charge state in relation to another particle.
Because of this charge, each proton and electron generates an electrostatic field that can interact with other particles. This field causes particles with different charge states to attract each other and particles with the same charge states to repel each other. As a result, protons and electrons attract each other, but protons repel other protons and electrons repel other electrons. The reason that protons can be bound so tightly together in the nucleus with other protons is the strong nuclear force that overrides the repelling electrostatic forces and holds the protons together.
Charged objects and their electrostatic fields
Most atoms have the same number of protons and electrons, so their electrostatic charges balance each other out, and the atom is said to be neutral. However, electrons can move much more freely than protons, making it possible for an atom to lose or gain electrons, depending on the type of atom and the electrostatic field generated by the particles.
Electron movement can result in an imbalance between the number of protons and electrons within an atom, causing the atom to be in a charged state. If there are more protons than electrons, the atom is positively charged. If there are more electrons than protons, the atom is negatively charged. A charged atom, whether negative or positive, forms an electrostatic field that can interact with other atoms.
Because atoms provide the building blocks for all objects, it is possible for entire objects to become charged and form electrostatic fields. Like an atom, an object is negatively charged if it has an excess of electrons relative to its surroundings, and it is positively charged if it is deficient in electrons. An object is considered to be in a neutral state -- no charge -- if the number of protons and electrons are fairly balanced.
If two objects have different charge states and are within relative proximity to each other, they form an electrostatic field whose strength depends on the amount of cumulative charge in each object and the distance between them. If two objects have the same charge states and are within proximity to each other, they each form their own electrostatic fields that repel each other. As with opposing charge states, the strength of the repelling force depends on the amount of charge in each object and the distance between them.
Most objects are in a neutral state, but they can become charged when different materials come into contact with each other in such a way that causes electrons to jump from one object to another. For example, if you rub an inflated balloon against your clothes, electrons move from the clothes to the balloon's surface, causing the balloon to have a negative charge. If you then stick the balloon up on a wall, it will hang there because the wall is more positively charged. An electrostatic field forms between the balloon and the wall, and causes the attraction between them.
Electrostatic fields and magnetic fields
Electrostatic fields bear some similarity to magnetic fields. Objects attract if their charges are of opposite polarity (+/-) and repel if their charges are of the same polarity (+/+ or -/-). The lines of electrostatic flux in the vicinity of a pair of oppositely charged objects are similar to lines of magnetic flux between and around a pair of opposite magnetic poles.
In other ways, electrostatic and magnetic fields differ. Electrostatic fields are blocked by metallic objects, while magnetic fields can pass through most, but not all, metals. Electrostatic fields arise from a potential difference or voltage gradient and can exist when charge carriers, such as electrons, are stationary -- hence the static in electrostatic. Magnetic fields arise from the movement of charge carriers -- that is, from the flow of current.
When charge carriers are accelerated, as opposed to moving at constant velocity, a fluctuating magnetic field is produced. This gives rise to a fluctuating electric field, which in turn produces another varying magnetic field. The result is a "leapfrog" effect in which both fields can propagate over vast distances through space. Such a synergistic field is known as an electromagnetic field and is the phenomenon that makes wireless communications, broadcasting and control systems possible.
See also: dielectric material, electric field strength, matter.
