embedded device
What is an embedded device?
An embedded device is part of a larger computing system and serves a specific purpose. Also known as a dedicated or single-purpose device, an embedded device is embedded or included within the larger system. This larger system usually serves a greater purpose and one or more embedded devices support it in meeting this purpose.
An embedded device is an independent device responsible for executing a particular task or set of tasks. Unlike hardware devices that contain some circuitry and perhaps a battery, an embedded device is capable of digital processing -- albeit not at the same scale as a fully functional computing device.
While most embedded devices are incorporated in larger systems, some devices can also be standalone. Generally, its operating system (OS) runs a single application that helps the device do its particular job. As a result, the embedded device consumes a small amount of power.
In addition, the device hardware is small. So, instead of a full-featured CPU, it may only have an 8-bit microcontroller or an application-specific integrated circuit (ASIC) chip or a dedicated digital signal processor (DSP).
The following are some common examples items with embedded devices:
- dishwashers
- microwaves
- bank ATM machines
- routers
- retail point of sale (POS) terminals
- smartphones
Parking meters, drones, airplanes and spaceships consist of numerous embedded devices. In the modern digital economy, embedded devices are ubiquitous in almost all electronic equipment.
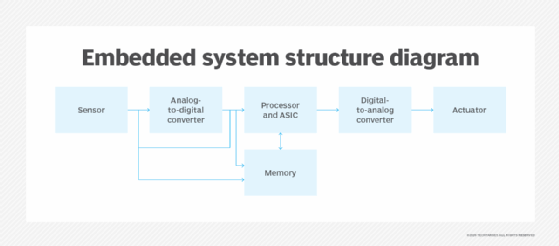
Components of embedded devices
All embedded devices consist of hardware and software. A microcontroller, microprocessor, ASIC or DSP are elements of an embedded device. Other hardware elements may include the following:
- graphics processing unit (GPU)
- memory (volatile and/or non-volatile)
- field programmable gate arrays (FPGA)
- communication interfaces and ports
- power supply or battery
Additionally, all embedded devices include software in the form of an OS or firmware. The software includes programming instructions for the device. Because embedded systems have limited computing resources and strict power requirements, writing software for embedded devices is a specialized field that requires knowledge of hardware components and programming. Peripheral devices, such as LCD displays, may also be connected to an embedded device or system.
Smart embedded devices vs. dumb embedded devices
Not all embedded devices connect to the internet. Traditional devices were built to fulfill a dedicated purpose within a larger system. They also had limited connectivity with other devices or to the internet. A device that cannot (or does not) connect to the internet is called a dumb embedded device. Examples of dumb embedded devices are legacy dishwashers, digital cameras and microwaves.
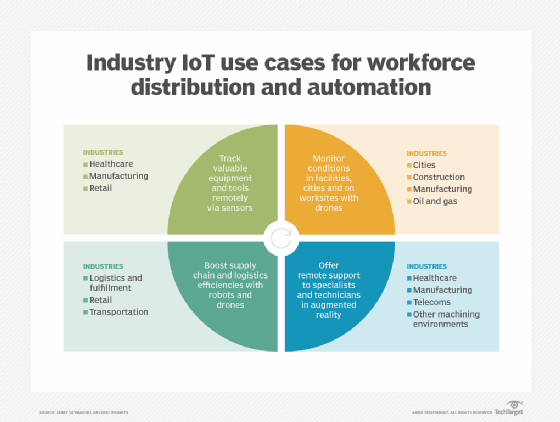
Embedded devices that connect to the internet are called smart or intelligent. These devices are vital for internet of things (IoT) applications. Following are examples of smart or intelligent embedded devices:
- smartphones
- smart watches
- smart refrigerators
- smart fitness trackers
- smart medical devices
In these devices, numerous embedded systems work together and communicate with each other via the internet. The system includes software, usually an OS or firmware, that supports connectivity and facilitates communication between the various embedded devices. The main difference between dumb and smart embedded devices is connectivity and internet-powered communication.
Headless embedded devices
Embedded devices in complex systems, such as automobiles or airplanes, are often headless. In a headless embedded device, the software does not have a user interface (UI) or built-in screen such as a monitor or LCD panel. In other words, it does not have a human-machine interface (HMI).
A headless device does not have an input device like a keyboard or mouse. This reduces the amount of system resources used. In such devices, an in-circuit emulator (ICE) is temporarily installed between the device and an external computer to debug or update the software.
Many of these systems require manual configuration to suit a user's specific preferences or requirements. An authorized user should be able to change certain operating parameters of the device. For example, a user may want to change the volume settings on a speaker system. Another may want to change the DNS server settings on a network router. Manual configuration eliminates the need to change the device's firmware or OS to satisfy individual user requirements.
Advantages and drawbacks of embedded devices
Since embedded devices are small and consume little power, they are suitable for systems with size, weight or power constraints. They also require less maintenance compared to the overall system. And since they are independent, they are ideal for executing specific tasks with little or no human inputs involved.
Most embedded devices operate in an uninterrupted manner and have a high degree of fault tolerance. Despite their independence and limited capabilities, they do contribute to the overall capabilities of a larger system. As part of IoT systems, embedded devices play a key role in smart devices for a range of real-world applications.
The size and limited capabilities of an embedded device are also its key drawbacks. Compared to a full-featured system, an embedded device cannot execute a range of tasks. Since its resources are limited, it can only handle specific tasks.
Applications of embedded devices
Embedded devices and systems are extensively used in a range of industries, including consumer electronics, commercial electronics, automotive, industrial and healthcare. These devices can be smart or dumb.
In consumer electronics, embedded devices are most commonly used in the following:
- household appliances
- entertainment systems
- POS systems
- ATMs
In commercial and industrial electronics, they are used in the following:
- enterprise security systems
- assembly line manufacturing systems
- data routers
- network switches
In the healthcare and automotive sectors, embedded devices are used in pacemakers, MRI scanners, PET scanners and vehicles. The aerospace industry uses embedded devices in air traffic control (ATC) systems, radar and flight control systems, navigation systems, aircraft management systems, flight recorders and collision avoidance systems.
Embedded devices and systems are also used in defense applications such as the following:
- unmanned aerial vehicles (UAVs)
- electronic warfare systems
- command and control systems
- weapons and guidance systems
See also: embedded operating system, embedded device hacking, embedded firmware, embedded software, embedded application security
