falsifiability
What is falsifiability?
Falsifiability is the capacity for some proposition, statement, theory or hypothesis to be proven wrong. The concept of falsifiability was introduced in 1935 by Austrian philosopher and scientist Karl Popper (1902-1994). Since then, the scientific community has come to consider falsifiability to be one of the fundamental tenets of the scientific method, along with attributes such as replicability and testability.
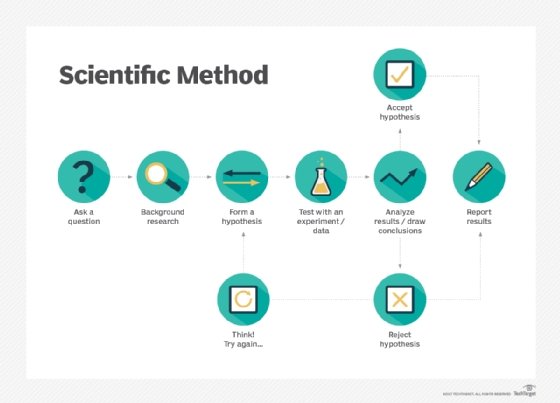
A scientific hypothesis, according to the doctrine of falsifiability, is credible only if it is inherently falsifiable. This means that the hypothesis must be capable of being tested and proven wrong. It does not automatically mean that the hypothesis is invalid or incorrect, only that the potential exists for the hypothesis to be refuted at some possible time or place.
For example, one could hypothesize that a divine being with green scales, mauve hair, ochre-colored teeth and a propensity for humming show tunes rules over the physical universe from a different dimension. Even if millions of people were to swear their allegiance to such a being, there is no practical way to disprove this hypothesis, which means that it is not falsifiable. As a result, it cannot be considered a scientific assertion, according to the rules of falsifiability.
On the other hand, Einstein's theory of relativity is considered credible science according to these rules because it could be proven incorrect at some point in time through scientific experimentation and advanced testing techniques, especially as the methods continue to expand our body of knowledge. In fact, it's already widely accepted that Einstein's theory is at odds with the fundamentals of quantum mechanics, not unlike the way Newton's theory of gravity could not fully account for Mercury's orbit.
Another implication of falsifiability is that conclusions should not be drawn from simple observations of a particular phenomenon. The white swan hypothesis illustrates this problem. For many centuries, Europeans saw only white swans in their surroundings, so they assumed that all swans were white. However, this theory is clearly falsifiable because it takes the discovery of only one non-white swan to disprove its hypothesis, which is exactly what occurred when Dutch explorers found black swans in Australia in the late 17th century.
Falsifiability is often closely linked with the idea of the null hypothesis in hypothesis testing. The null hypothesis states the contrary of an alternative hypothesis. It provides the basis of falsifiability, describing what the outcome would demonstrate if the prediction of the alternative hypothesis is not supported. The alternative hypothesis might predict, for example, that fewer work hours correlates to lower employee productivity. A null hypothesis might propose that fewer work hours correlates with higher productivity or that there is no change in productivity when employees spend less time at work.
Popper makes the case for falsifiability
Karl Popper introduced the concept of falsifiability in his book The Logic of Scientific Discovery (first published in German in 1935 under the title Logik der Forschung). The book centered on the demarcation problem, which explored the difficulty of separating science from pseudoscience. Popper claimed that only if a theory is falsifiable can it be considered scientific. In contrast, areas of study such as astrology, Marxism or even psychoanalysis were merely pseudosciences.
Popper's theories on falsifiability and pseudoscience have had a significant impact on what is now considered to be true science. Even so, there is no universal agreement about the role of falsifiability in science because of the limitations inherent in testing any hypothesis. Part of this comes from the fact that testing a hypothesis often brings its own set of assumptions, as well as an inability to account for all the factors that could potentially impact the outcome of a test, putting the test in question as much as the original hypothesis.
In addition, the tests we have at hand might be approaching their practical limitations when up against hypotheses such as string theory or multiple universes. It might not be possible to ever fully test such hypotheses to the degree envisioned by Popper. The question also arises whether falsifiability has anything to do with actual scientific discovery or whether the theory of falsification is itself falsifiable.
No doubt many researchers would argue that their brand of social or psychological science meets a set of criteria that is equally viable as those laid out by Popper. Even so, the important role that falsifiability has played in the scientific model cannot be denied, but Popper's black-and-white demarcation between science and pseudoscience might need to give way to a more comprehensive perspective of what we understand as being scientific.
See also: empirical analysis, validated learning, OODA loop, black swan event, deep learning.