farad (F)
What is a farad (F)?
A farad (F) is the standard unit of capacitance (C) in the International System of Units (SI). It indicates the ability of a substance to hold an electric charge. The value of most electrical capacitors is expressed in farads, microfarads (µF) or nanofarads (nF).
Named after the English scientist Michael Faraday, 1 F is equivalent to 1 second to the fourth power ampere squared per kilogram meter squared (s4 x A2 / kg x m2).
Farad explained
When an electric charge moves between two uncharged conductors, a potential difference is established between them, or the amount of electricity charged upon a conductor increases its potential. Additionally, one conductor becomes positively charged, and the other becomes negatively charged.
Capacitance refers to the amount of separated electric charge or electrical energy that can be stored on a conductor per unit change in electrical potential. Mathematically, it is expressed as the ratio of the amount of charge (q) on either conductor to the potential difference (V) between them:
C = q / V
Farad is the unit of capacitance. A capacitor has a capacitance of 1 F when 1 coulomb (C) of electricity changes the potential between the plates by 1 volt (V). Another way of saying this is that, when the voltage across a 1 F capacitor changes at a rate of 1 V/s, the result is a current flow of 1 A.
The SI base units of 1 farad are s4 x A2 x m-2 x kg-1.
Mathematically, it can be represented like this:
1 F = 1 s4 x A2 / m2 x kg
Farad, microfarad, nanofarad, picofarad
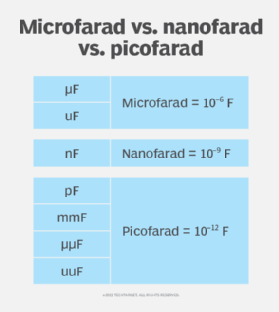
The farad is an extremely large unit of capacitance. In most electronic and electrical equipment, capacitors with values this large are rare -- but not impossible. Most capacitors are generally rated in microfarads, nanofarads or picofarads (pF). The older term for picofarad was micromicrofarad (μμF). A picofarad capacitor is sometimes known as a pic or puff.
1 µF = 10-6 F = 0.000001 F
1 nF = 10-9 F = 0.000000001 F
1 pF = 10-12 F = 0.000000000001 F
The millifarad (mF) is rarely used in practice. It is represented as the following:
1 mF = 10-3 F = 0.001 F
At radio frequencies, capacitances range from about 1 pF to 1,000 pF in tuned circuits and from about 0.001 µF to 0.1 µF for blocking and bypassing.
At audio frequencies, capacitances range from about 0.1 µF to 100 µF.
In power supply filters, capacitances can be as high as 10,000 µF.
Supercapacitors and kilofarads
Some capacitors with farad values as large as 1,000 F (kilofarad) are also in use. These capacitors are known as supercapacitors or ultracapacitors. The high farad values indicate that these capacitors can store larger amounts of energy per unit volume or mass -- typically 10 to 100 times more than electrolytic capacitors.
In addition, these capacitors can deliver a charge faster than rechargeable batteries. They can also tolerate more charge and discharge cycles than rechargeable lithium-ion batteries that tend to degrade with each charge cycle.
High-farad value supercapacitors are usually used in applications that require short-term energy storage, power delivery in burst mode, and multiple charge and discharge cycles. They are suitable for the following:
- automobiles
- elevators
- cranes
- wind turbines
Supercapacitors are not suitable for applications that require long-term compact energy storage, such as consumer devices, like smartphones or tablets. Nonetheless, there are some consumer devices where supercapacitors are used due to their quick recharge capability and prolonged lifecycles. These include MP3 players and professional camera flashes.
How larger capacitances are obtained
Most practical capacitors range between 0.001 μF and 10 F. Larger capacitances can be obtained by increasing the conductor's area, decreasing the space between the plates or using a dielectric medium with a larger permittivity value -- measured in farads per meter.
However, there is a limit to how much the plate spacing can be reduced to achieve a high capacitance (high farad value). This limit depends on the dielectric breakdown strength of the insulating material between the conducting plates. When this space limit is exceeded, a spark jumps between the plates. It also leaves a conducting track within the insulating material, damaging the capacitor.
Knowing the electric field strength of the dielectric material is also important. This value is used to calculate the voltage that can be safely applied to a capacitor of a given plate separation. Here, safe means the voltage value that won't cause arcing in the capacitor. This is why capacitors are stamped with both capacitance (farad) and voltage values.
Farad and Faraday constant
While both the farad and Faraday constant are symbolized by the capital letter F, they are two different things. One F indicates that the capacitor produces 1 V of potential difference for an electric charge of 1 C. The Faraday constant is a measure of the amount (magnitude) of electrical charge carried by a single mole of electrons (Avogadro's number). It is represented as C/mol.
The value of the Faraday constant is obtained by dividing the Avogadro constant by the number of electrons per coulomb or by multiplying the charge of a single electron with the number of electrons in 1 mol.
Faraday constant (F) = charge of a single electron x the number of electrons in 1 mol
= 1.6023 x 10-19 C x 6.02 x 1023
= 96,485 C/mol
See also: table of physical units, reactance, admittance, susceptance and henry.
