File Allocation Table (FAT)
What is File Allocation Table (FAT)?
File Allocation Table (FAT) is a file system that was developed by Microsoft to support small disks and simple folder structures. The file system is named File Allocation Table because it uses a table to track the clusters on a storage volume, as well as how those clusters are linked together through their associated files and directories. Because of the table's important role, the acronym FAT is sometimes used to refer to the table itself, rather than the file system, although it's not uncommon to see it used both ways in a single resource.
The FAT file system got its start with the introduction of MS-DOS, or Microsoft Disk Operating System, and is still in use today, but it has evolved over the years to accommodate growing data volumes. During that time, there have been multiple versions of the file system. The original version was FAT8, followed by FAT12, then FAT16 and finally FAT32. Several variants have also been developed based on the last three versions -- FAT12, FAT16 and FAT32 -- further extending the file system.
The number associated with each FAT version (e.g., FAT16) refers to the number of bits that are used for each entry in the allocation table. For example, an allocation table entry for a FAT16 volume is 16 bits long. However, it's not just the number of entry bits that differentiates the FAT versions. Each version also supports larger volumes and file sizes than its predecessor. Even so, FAT is still limited to small-scale storage compared with more modern file systems. The largest file size FAT32 can support is 4 gigabytes, and the largest volume size is 2 terabytes.
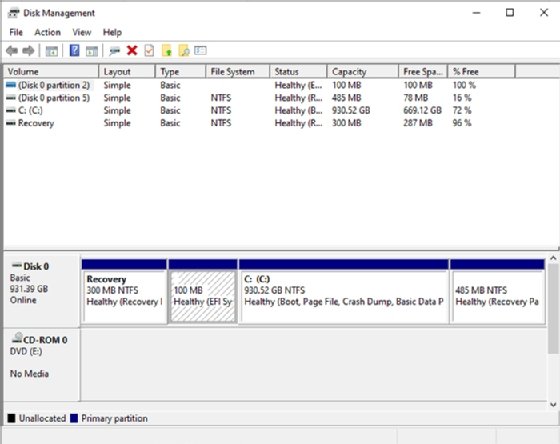
At one time, the FAT file system was used extensively for Windows computers. However, today, most Windows systems use the New Technology File System (NTFS) -- or, to a lesser degree, the Resilient File System (ReFS), which Microsoft introduced in 2012 promising to support greater availability, resiliency and scalability.
Although the FAT system has been superseded on most Windows computers, current Windows editions still support FAT, as do macOS, Linux and Unix. In addition, FAT is still used for floppy disks, USB flash drives and storage media in smaller, portable devices such as digital cameras.
What is the function of File Allocation Table?
FAT plays a pivotal role in facilitating file and directory access on a FAT volume, and is directly integrated into the volume's layout. A FAT volume is organized into multiple sections that follow a prescribed order, starting with the boot sector:
- Boot sector. Stores the information needed by the file system to access the volume, including the volume's layout and file system structure.
- Allocation table region. Stores the primary allocation table, as well as a duplicate of the table that serves as a backup in case the primary table cannot be accessed.
- Root directory. Stores a directory table containing entries that describe the files and folders stored on the volume. Each entry includes information such as name, size, created date and last modified date. An entry also includes the starting cluster number, which corresponds to an entry in the file allocation table. For FAT12 and FAT16, the root directory exists at a specified location on the storage media -- right after the allocation tables -- and has a fixed number of maximum entries. The root directory for FAT32 is maintained in the data region and does not have a fixed number of maximum entries.
- Data region. Stores the actual file and directory data. This area is divided into clusters that make up the bulk of the volume. The clusters are numbered sequentially and correspond to the listings in the allocation table.
Clusters are the basic units of logical storage on a FAT volume. A cluster can range in size from 512 bytes to 64 kilobytes, depending on volume size and type of FAT file system. Each file written to a FAT volume is stored in one or more clusters, with each cluster available to only one file at a time. A file's clusters might be adjacent to each other in consecutive order or be scattered across the volume, resulting in a fragmented file.
The allocation table on a FAT volume tracks each cluster in that volume, mapping the allocation chains associated with the volume's directories and files. Each table entry corresponds to a cluster and is typically in one of four states:
- The cluster is unused.
- The cluster is in an allocation chain associated with a specific file or directory; the table entry references to the next cluster in the chain.
- The cluster is the last cluster in an allocation chain associated with a specific file or directory.
- The cluster is bad.
The first cluster entry in the allocation table is typically used for the volume's FAT ID, and the second entry indicates that the cluster is reserved. In a FAT32 volume, the third entry usually corresponds to the first cluster used for the root directory. The rest of the cluster entries in the allocation table are devoted to the directory and file allocation chains. Each chain begins with the cluster identified in the root directory listing for that directory or file. A chain might be made up of only one cluster, in which case it's marked as the last cluster in the chain.
When reading a file from a FAT volume, the operating system reassembles the file from the clusters -- referencing the allocation table for the file's chain linkage -- and then renders the file in its entirety in memory.
Explore the differences between FAT16, FAT32, NTFS and ReFS.
