font
What is a font?
The word font refers to a set of printable or displayable typography or text characters in a specific style and size. Font styles are used in both print and digital text.
While typographic font styles have custom spacing and design, once determined, this style will apply to both lowercase and uppercase letters as well as punctuation marks.
The type design for a set of fonts is the typeface, and variations of this design form the font family.
For example, Helvetica is a font family, while Helvetica italic is a typeface, and Helvetica italic 10-point is a font. In practice, font and typeface are often used as synonyms even though they represent slightly different aspects of a specific font.
What are examples of commonly used font typefaces and styles?
There are seemingly limitless types of fonts available for use today. In addition to numerous fonts that are free to use, graphic designers are also capable of designing new fonts. Thus, the number of available fonts will continue to grow.
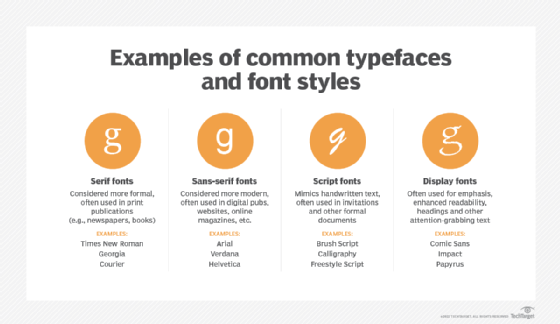
The following are some of the most traditional font styles in circulation.
Serif fonts
Serif typefaces have small embellishments, called serifs, on the ends of the letterforms. Serif fonts are considered more formal and are often used in print publications, such as newspapers and books.
Examples of serif font styles include Times New Roman, Georgia and Courier.
Sans-serif fonts
Sans-serif font styles do not have serifs. Sans-serif fonts are considered more modern and are often used in digital publications, such as websites and online magazines.
Examples of sans-serif font styles include Arial, Verdana and Helvetica.
Script fonts
Script font styles mimic the appearance of handwritten text. They are often used for invitations and other formal documents.
Examples of script font styles include Brush Script, Calligraphy and Freestyle Script.
Display fonts
Display font styles are designed to be used in specific sizes to emphasize a particular message or enhance readability. They are often used for headings and other attention-grabbing text.
Examples of display font styles include Comic Sans, Impact and Papyrus.
What are the different font file formats available?
There are a variety of font file formats that can be used on both Windows and Mac computers. Some of the most common file formats are highlighted below:
- TrueType (.ttf) is a font file format developed by Apple and Microsoft. It is the most common format for fonts on both Windows and Mac computers.
- OpenType (.otf) is a file format for scalable, or outline, font files that extend the existing TrueType font file format.
- PostScript Type 1 (.pfb and .afm) is a font file format developed by Adobe. It is commonly used on Windows and Mac computers.
- Web Open Font Format (.woff) was developed to provide a compact format for font files that can be used on websites.
- Bitmap (.bmp) uses a unit called a pixel to build symbols called glyphs that make up a total bitmap font. Bitmap fonts are most commonly seen in Adobe software.
How can fonts be accessed?
Most modern word processors, such as Microsoft Word and Google Docs, give you access to numerous fonts. They also allow you to change the font face, font point size, font color and font style of the text in your document.
When downloading a commercially licensed font or commissioning a custom font from a graphic designer, font files are usually installed in the C:\Windows\Fonts or C:\WINNT\Fonts folder on a Windows computer. On a Mac, font files are installed in the Library/Fonts or System/Library/Fonts folder.
Printers and fonts
Printers use two kinds of fonts: resident and soft fonts. Resident fonts are built into the printer's hardware. Users can add soft fonts -- free or purchased -- from a font cartridge, hard drive or flash drive, or after downloading from the internet. Resident fonts cannot be erased, while soft fonts can.
