glyph
What is a glyph?
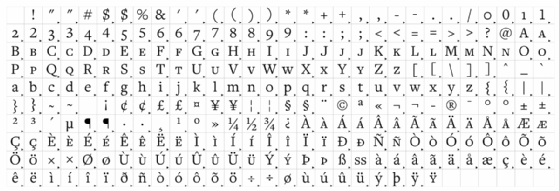
In information technology, a glyph -- from a Greek word meaning carving -- is a graphic symbol that provides the appearance or form for a character. It can be an alphabetic or numeric character, or a symbol. Glyphs can be found in a variety of fonts, and they can be used to represent characters in numerous languages.
History of glyphs
The first glyphs were created by ancient civilizations, such as the Sumerians and Egyptians, to represent words and ideas. They were carved into stone or clay tablets.
In the Middle Ages, illuminated manuscripts used glyphs that were often very elaborate, to add beauty and meaning to the text.
In the 15th century, the invention of the printing press led to the development of new fonts and typefaces. The use of glyphs became widespread in books, newspapers and other printed materials.
Today, glyphs are used in computer fonts, on websites and in mobile apps. They are also used in a variety of other contexts, such as in traffic signs, on maps and in product packaging.
Types of glyphs
Some of the most common types of glyphs include the following:
- Alphabetic glyphs represent letters of the alphabet.
- Numeric glyphs denote numbers.
- Symbol glyphs represent items, such as punctuation marks, and mathematical and currency symbols.
Features and capabilities of glyphs
Some of the most important features of glyphs include the following:
- Shape. The shape of a glyph is its most obvious feature and can be used to convey meaning, such as the difference between a capital "A" and a lowercase "a."
- Size. A large glyph might emphasize a word or phrase.
- Color. A red glyph, for example, might warn a user of danger.
- Position. A glyph at the beginning of a sentence might indicate the sentence is a question.
Benefits of using glyphs
Some of the most important benefits of glyphs include the following:
- Accuracy. Glyphs can represent characters with a high degree of precision.
- Speed. Glyphs can be used to input text quickly and easily. This is especially beneficial when working with computers and other electronic devices.
- Recognition. Glyphs are very recognizable because they are often used in a consistent manner. For example, the letter "A" is always represented by the same glyph, regardless of the font or typeface used.
