personal computer (PC)
What is a personal computer (PC)?
A personal computer (PC) is a microcomputer designed for use by one person at a time.
Prior to the PC, computers were designed for -- and only affordable for -- companies that attached terminals for multiple users to a single large mainframe computer whose resources were shared among all users. By the 1980s, technological advances made it feasible to build a small computer that an individual could own and use as a word processor and for other computing functions.
The advent of the era of the personal computer was acknowledged by Time magazine in 1982, when it broke with tradition by choosing the PC as its Man of the Year.
What are personal computers used for?
Whether they are home computers or business ones, PCs can be used to store, retrieve and process data of all kinds. A PC runs firmware that supports an operating system (OS), which supports a spectrum of other software. This software lets consumers and business users perform a range of general-purpose tasks, such as the following:
- word processing
- spreadsheets
- instant messaging
- accounting
- database management
- internet access
- listening to music
- network-attached storage
- graphic design
- music composition
- video gaming
- software development
- network reconnaissance
- multimedia servers
- wireless network access hotspots
- video conferencing
Users can repurpose older PCs for tasks outside of standard computing, such as contributing processing power to distributed computing projects. The Folding@home project is an example where idle processing power is used to run simulations of cell protein dynamics to help scientists find cures for chronic illnesses such as Alzheimer's disease.

Types of personal computers
Personal computers fall into various categories, such as the following:
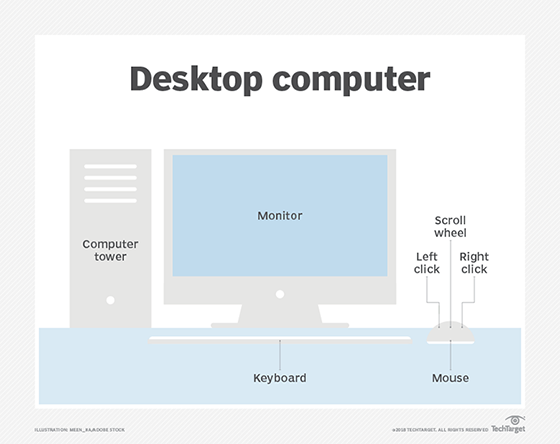
- Desktop computers usually have a tower, monitor, keyboard and mouse.
- Tablets are mobile devices with a touchscreen display.
- Smartphones are phones with computing capabilities.
- Wearables are devices users wear, such as smartwatches and various types of smart clothing.
- Laptop computers are portable personal computers that usually come with an attached keyboard and trackpad.
- Notebook computers are lightweight laptops.
- Handheld computers include advanced calculators and various gaming devices.
Other ways of categorizing PCs include the following:
- processing speed
- processing power
- power consumption
- memory capacity
Personal computing devices differ in other ways as well. For example, laptops and notebooks generally use less power than desktops, but often don't have as much storage. Tablets and smartphones typically have less input/output (I/O) capability than laptops and desktops.
PC components can be switched out to modify the devices. For example, people who play video games often construct gaming PCs that maximize processing power and speed using high-quality processors.
Components of personal computers
Personal computer systems generally consist of the following hardware components:
- Computer cases are the boxes that hold the main components of the PC. They come in different colors and sizes, and might have fans already installed.
- Power supplies deliver electricity to PCs. They come in different wattages.
- Motherboards are circuit boards that connect many parts of the PC's inner workings. They hold the central processing unit (CPU) and graphics processing unit (GPU).
- CPUs are the brains of the computer. They determine the PC's performance capability.
- GPUs are specialized processors that accelerate graphics processing. Sometimes these come integrated with CPUs, and sometimes they are discrete parts.
- Fans are the cooling units that keep PCs from overheating.
- Random access memory, also called short-term memory, holds data while it is actively being used by the CPU. RAM is volatile memory, which means it does not hold information after the PC is powered off.
- Storage provides the PC's long-term memory. It stores information when the PC does not have power. PCs can have hard disk drives, solid-state drives or non-volatile memory express SSDs.
- Optical drives and/or writers. These allow the PC to read and write CDs, DVDs or Blu-ray discs. These can also be external.
- Input ports are where external devices such as USB storage devices and external hard drives are plugged in.
- Operating systems provide a graphical user interface (GUI) and a platform to run other software on.
- Monitors display information to the end user.
- Keyboards are peripheral devices that let users type commands and other information.
- Mice and trackpads let users control the cursor.
History of personal computers
Some significant dates in PC history include the following:
- 1974. The first personal computer -- the MITS Altair -- was developed. It was popular with hobbyists, but lacked consumer appeal.
- 1977. Three PCs targeted at consumers were mass produced: Apple Computer's Apple II, Tandy Radio Shack's TRS-80 and Commodore International's Personal Electronic Transactor. Individuals, small and medium-sized businesses, and schools bought them because they were much less expensive than the mainframes that preceded them.
- 1981. IBM entered the market with IBM PC, which was faster and had more memory than rival machines. The first truly portable computers were released: Osborne Computer's Osborne I and the Epson HX-20.
- 1983. Apple introduced Lisa, the first PC with a GUI. Previous interfaces used command-based interfaces.
- 1985. Microsoft introduced the Windows OS as a GUI extension to the Microsoft Disk Operating System, or MS-DOS.
- 1988. The NEC UltraLite was introduced; it was the first laptop PC weighing less than 5 pounds.
- 1992. The IBM ThinkPad was introduced with features such as the pointer stick and touchpad, which many laptops retain today. The first personal digital assistant devices came out this year as well.
Examples of personal computers
The term personal computer traditionally has been used to describe an IBM-compatible PC as opposed to an Apple computer. The distinction is both technical and cultural, going back to the early years of PCs when IBM and Apple were the two major competitors.
Originally, the IBM PC was one with an Intel microprocessor architecture and a DOS or Microsoft Windows OS written to use an Intel microprocessor. The Apple Macintosh used a proprietary OS.
IBM-compatible PCs were associated with business use. Apple computers were known for having more intuitive user interfaces and were associated with graphic design and desktop publishing. Although those distinctions have become less clear-cut in recent years, people often still categorize personal computers as either Macs or non-Macs.
A few other notable examples of personal computers over the years include the following:
- BBC Micro
- Google Chromebook
- Microsoft Surface
- Xerox Alto
Personal computer vs. desktop vs. laptop
Laptop and desktop computers are both types of personal computers.

Laptops
These portable computers have a rechargeable battery, keyboard, trackpad and screen attached to a case that contains the storage, RAM, fan and other central components. Laptops are portable, but might have less memory and less powerful processing capabilities. Laptops are also harder to customize. Components are packed tightly in the case for the sake of portability and are often permanently attached.
Desktops
These computers are not portable and usually consist of a tower that encases the processor, RAM, storage and I/O ports. They typically have an external monitor and a keyboard that plugs into the tower. Desktops do not have the benefit of portability, but likely have better processing power and more memory than laptops. They are often customizable, with preexisting space in the case to add extra components.
Businesses often need desktop management software to track and manage the many PCs they own. Compare these eight desktop management software options to find the best way to manage desktops and other devices in the enterprise.
