image compression
What is image compression?
Image compression is a process applied to a graphics file to minimize its size in bytes without degrading image quality below an acceptable threshold. By reducing the file size, more images can be stored in a given amount of disk or memory space. The image also requires less bandwidth when being transmitted over the internet or downloaded from a webpage, reducing network congestion and speeding up content delivery.
What are the two types of image compression?
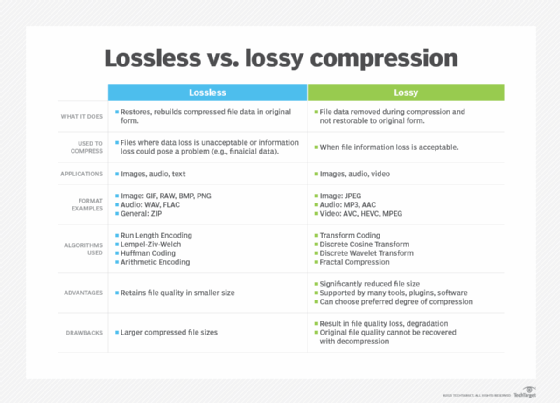
The methods used to compress image files typically fall into one of two categories: lossy and lossless. Lossy compression reduces an image file size by permanently removing less critical information, particularly redundant data. Lossy compression can significantly reduce file size, but it can also reduce image quality to the point of distortion, especially if the image is overly compressed. However, quality can be maintained when compression is carefully applied.
One of the challenges with lossy compression is that it's irreversible. Once it has been applied to an image, that image can never be restored to its original state. If lossy compression is applied repeatedly to the same image, it gets increasingly distorted. That said, lossy compression has proved to be a valuable strategy for the web, where a moderate amount of image degradation can often be tolerated.
The most common example of lossy compression is JPEG, an image compression format used extensively on the web and in digital photography. This widely recognized format is supported by numerous tools and applications. Additionally, compression can be applied in degrees, making it possible to use JPEG compression that best strikes a balance between file size and quality.

The other approach to image compression is referred to as lossless. This method applies compression without removing critical data or reducing image quality and results in a compressed image that can be restored to its original state with no degradation or distortion. However, lossless compression doesn't reduce the file size nearly as much as lossy compression, offering little advantage in terms of storage space, network bandwidth or download speeds. Lossless compression is generally used in situations where image quality is more important than disk space or network performance, such as for product images or to showcase artwork.
One of the most common lossless formats is PNG, a widely used format that reduces file size by identifying patterns and compressing those patterns together. Although PNG files are generally larger than JPEG files, websites use them extensively when more image detail is needed, such as for logos, icons, screenshots or images with text. Another familiar lossless format is BMP, a proprietary approach to image compression introduced by Microsoft and used primarily for Microsoft products, particularly Windows computers.
GIF is compression format that falls into the lossless category, although there is some confusion as to whether it is lossy or lossless. GIF images are limited to 256 colors, so converting an image with more colors to GIF results in a loss of quality, which is sometimes attributed to lossy compression. But the compression algorithms used by GIF are lossless. If quality is lost, it's due to issues related to converting the file. Currently, the GIF format is used primarily for simple videos and animations.
A compression format that's making headway is Google's WebP, an image format developed exclusively for the web. Unlike most compression techniques, WebP supports both lossless and lossy compression, making it highly versatile. WebP images generally use less disk space than other formats but offer comparable quality. Most major browsers support WebP images.
Compression can also be used for non-image file types such as text or program files, but its use tends to be limited to lossless compression. In text and program files, it is crucial that compression be lossless because a single error can damage the meaning of a text file or cause a program not to run. The zip file format is an example of lossless compression commonly used for text files or even entire directories of files.
In image compression, a small loss in quality is usually not noticeable. In situations where there is some tolerance for loss, greater compression can be applied to files than when there is no tolerance for loss. For this reason, graphic images can usually be compressed to a much greater degree than text or program files.
See also: codec
