business process outsourcing (BPO)
What is business process outsourcing (BPO)?
Business process outsourcing (BPO) is a business practice in which an organization contracts with an external service provider to perform an essential business function or task.
An organization typically contracts with another business for such services after it has identified a process that, although necessary for its operations, is not part of its core value proposition. This step requires a good understanding of the processes within the organization and strong business process management.
Many organizations consider processes that are performed the same or similarly from company to company, such as payroll and accounting, as good candidates for BPO.
BPO typically offers flexibility and cost efficiency to organizations that implement it. Companies calculate that outsourcing these processes to a provider that specializes in them could deliver better results.
BPO has its roots in the manufacturing industry. Manufacturers hired third-party vendors to handle parts of their supply chains after determining that the vendors could bring more skills, speed and cost efficiencies to those processes than an in-house team could deliver. Over time, organizations in other industries adopted the practice.
Today, the use of BPO has expanded with for-profit businesses, nonprofits and even government agencies outsourcing a range of tasks to service providers located in the U.S., throughout North America and across the world.
What is business process outsourcing used for?
Organizations engage in business process outsourcing for two main areas of work: back and front-office functions.
Back-office functions, sometimes called internal business functions, comprise support operations, including accounting, IT services, human resources (HR), quality assurance and payment processing.
Front-office functions are processes and business operations that serve or relate to existing and potential customers, such as customer relation services, marketing and sales.
Some organizations outsource an entire function, such as the HR department, to a single vendor. Other companies outsource only specific processes within a functional area, such as payroll processing, while having their own team perform all other HR processes.
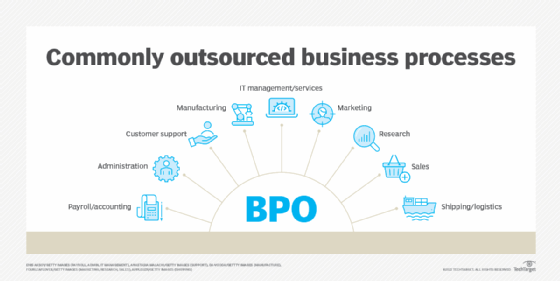
Commonly outsourced processes include the following:
- Payroll and accounting.
- Administration.
- Customer support.
- IT management and services.
- Manufacturing.
- Marketing.
- Research.
- Sales.
- Shipping and logistics.
Some companies also outsource strategic tasks, such as data mining and data analytics, both of which have become essential elements for maintaining a competitive advantage in a digital economy.
How does business process outsourcing work?
Enterprise executives opt to outsource a business process for a variety of reasons. Those reasons vary based on the type, age and size of the organization, as well as market forces and economic conditions.
Startup companies, for example, often need to outsource back-office and front-office functions as they do not have the in-house resources to perform them.
An established company may opt to outsource a task that it had been performing after determining that a third-party service provider could do the job better or cheaper. Management experts advise enterprise executives to identify functions that can be outsourced and then determine if shifting that task to an outsourcing provider makes sense.
If so, the organization must go through the process of not only identifying the best vendor for the work, but also shifting the work from in-house to the external provider. This requires a significant amount of change management, as the move to an outsourced provider generally affects staff, established processes and existing workflows.
The shift to an outsourced provider also affects the organization's finances -- not only in terms of shifting costs from the internal function to the outsourced providers, but often in terms of corporate taxes and reporting requirements.
The organization may also need to invest in new technology to enable the smooth flow of work to the outsourced provider. The extent and cost of that technology depend on the scope of the function being outsourced and the maturity of the technology infrastructure in place at both enterprises.
This process typically starts with enterprise leaders identifying specific functions or business processes to outsource as a way to save money, gain flexibility, improve performance and redirect resources to core business capabilities.
Business leaders then consider whether one vendor should handle all the work being outsourced or whether contracting multiple providers for the various tasks delivers the best value. For example, a company could decide to outsource most of its HR functions and then either contract for a single provider to perform all the outsourced processes or hire one for payroll and another for benefits administration.
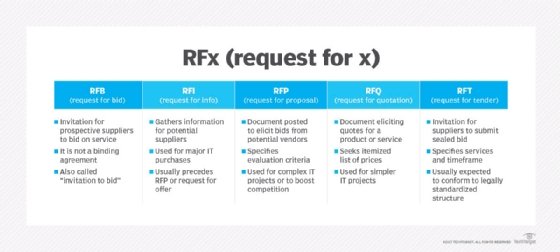
Those considerations should lead to a list of requirements, as well as a detailed scope of work, for outsourcing. Organizations use those to shape a request for proposal (RFP) to share with vendors that determine whether they can meet the requirements, at what price and with what value-adds.
Once an organization has selected the provider or providers it wants to hire, it must determine the type of contract. Such contracts generally fall into one of the following categories:
- Time and materials contracts, in which the business pays the provider for the time worked and the materials used.
- Fixed-price contracts, which set an upfront price for the specified work.
Additionally, organizations must, with their vendors, draft the service-level agreement detailing the quality of the provided services and the metrics for determining success.
Depending on the needs and nature of the outsourced work, some organizations also negotiate with providers on whether to have the following:
- Specific workers on teams dedicated to their outsourced work.
- Workers located only onshore or, conversely, globally distributed.
- Workers available 24/7 or only during set hours.
What are the benefits of business process outsourcing?
Benefits of BPO typically cited by proponents include the following:
- Financial benefits. BPO providers can often perform a business process at lower costs or save the company money in other ways, such as in tax savings.
- Improved flexibility. BPO contracts can offer the ability to modify how an outsourced business process is done, enabling companies to react more nimbly to changing market dynamics.
- Increased competitive advantage. BPO enables an organization to focus more of its resources on operations that distinguish it in the marketplace.
- Higher quality and better performance. Because business processes are their core business, BPO providers are well positioned to complete the work with greater accuracy, efficiency and speed.
- Access to innovations in the business process. BPO providers are more likely to know about advances in the process areas they specialize in. That means they are more likely to invest in new technologies, such as automation, that can improve the speed, cost and quality of the work.
- Expanded coverage. Organizations that need 24/7 call center operations can often quickly gain that capability by contracting with a BPO company with around-the-clock capabilities and multiple geographic locations, enabling a follow-the-sun business model.
What are the risks of business process outsourcing?
BPO risks include the following:
- Security breaches. The technology connection between the hiring company and the BPO provider creates another point of entry for bad actors, as organizations often need to share sensitive and regulated data with their service providers.
- Regulatory compliance requirements. An organization's regulatory requirements extend even to outsourced work, so it must ensure that the vendors it hires align with the laws the organization must follow. It must also ensure that the vendors adhere to the rules that govern the organization's outsourced work.
- Unanticipated or higher costs. Organizations can underestimate the amount of work that needs to be done, which can lead to higher-than-anticipated costs.
- Relationship challenges. Organizations can face communication problems with their outsourced providers, or they might find that there are cultural barriers.
- Overdependence on the external provider. An organization that outsources a function or service is tethered to the partner that performs the work. The organization must manage that relationship to ensure key objectives are met at the agreed-upon cost. If not, the organization may find it difficult to bring the operation back in-house or even move the contract to another outsourced provider.
- Increased potential for disruption. An organization must monitor for issues that could interrupt or permanently end the relationship with an outsourced provider. These include financial or workplace problems at the outsourced provider, geopolitical instability, natural disasters or changes in economic circumstances. Organizations must consider such risks and devise strategies on how to cope, which, in turn, adds complexity to their business continuity and disaster recovery.
- Public backlash. The public perception of an organization might negatively change if the public views that an organization is sacrificing domestic jobs for a better bottom line.
What are the different types of BPO?
BPO is often divided into the following types based on the service provider's location:
- Offshore outsourcing occurs when an organization contracts for services provided with a company in a foreign country.
- Onshore outsourcing, or domestic outsourcing, happens when an organization contracts for services provided by a company that operates in the same country as the hiring organization.
- Nearshore outsourcing is when an organization contracts for services provided by companies based in neighboring countries.
Research firm Gartner categorized BPO as either horizontal offerings or vertical-specific offerings. Horizontal offerings are functions that are used across multiple industries, while vertical-specific offerings are those that are industry-specific.
KPO, LPO and RPO
Business process outsourcing is sometimes categorized by the types of services being provided; the following three categories are commonly cited:
- Knowledge process outsourcing (KPO) is when the outsourced service provider is hired not only for its capacity to perform a particular business process or function, but also to provide expertise around it. KPO is ideal for receiving high-quality work that is quick and efficient.
- Legal process outsourcing (LPO) is a type of KPO that is specific to legal services; these range from drafting legal documents and performing legal research to offering advice.
- Research process outsourcing (RPO) -- another type of KPO -- refers to outsourcing research and analysis functions. Biotech companies, investment firms and marketing agencies are among the types of organizations that engage in RPO for services.
RPO can also refer to recruitment process outsourcing, which outsources an organization's recruitment process, including sourcing, screening, interviewing and finalizing offers.
Business process outsourcing examples
One example of an organization using BPO might be if it's struggling to maintain its HR department. In this example, it might need more skilled HR workers to keep up with this core business function. The organization can partner with a BPO provider that specializes in HR. It can begin to focus on its main work, while the outsourcer handles HR-related tasks, such as payroll, recruitment and benefits administration.
Another example is a business that hires a BPO provider for call center services. A small business might not have the time or resources to dedicate to investing in a call center. It can, instead, invest in a BPO provider that specializes in providing that business process.
How to choose a business process outsourcing provider
Enterprise executives should select BPO providers that can support their business objectives, as well as help them be more flexible, innovative and competitive. As such, organizations should consider more than just the price of a BPO contract when choosing a provider. They must also consider how well the provider can deliver on those other points, evaluating each provider to determine whether it has the following:
- An adequate understanding of the organization's business and industry.
- The capacity to meet current requirements, as well as to scale to meet future needs.
- An understanding and ability to meet compliance and regulatory requirements, as well as data privacy needs.
- Reporting metrics to demonstrate it is delivering on contractual standards.
- The geographical locations to meet business needs and regulatory requirements.
Organizations should conduct their own needs assessment to identify business processes that would benefit from outsourcing. They should then get in contact with different BPO providers to determine which one best suits their needs and which creates the best RFP. After it picks one and agrees to the terms of the RFP, the organization should begin the transition process of shifting agreed-upon processes.
Business process outsourcing market size
Research firms predicted that the global business process outsourcing market will continue to grow through the coming decade.
For example, in 2021, Grand View Research valued the global BPO market at $245.9 billion. A more recent report by GlobalData valued the BPO market at $329.9 billion in 2022. The same GlobalData report expects the market to experience a compound annual growth rate of 2.8% from 2023 to 2026.
The growth of the BPO market is driven by an increasing demand for outsourcing various business functions, like HR, customer services, data entry and other core competencies.
Future directions of the BPO industry
Executives continue to identify and reorder what they need and want from the vendors they contract with to handle their business processes.
Service provider CGS, which surveyed more than 200 business leaders and decision-makers about what they used to evaluate their BPO providers in 2021, found the following:
- 6% put data privacy and compliance as their top priority.
- 9% want their providers to be knowledge partners with advanced technology capabilities.
- 3% evaluate BPO providers on their technology platform capabilities.
- 3% want BPO providers with in-depth experience in the organization's own industry vertical.
Current trends involved in BPO include the following:
- Cloud-based BPO offerings. BPO vendors are increasingly offering cloud-based services that save on cost when compared to traditional models. This model also offers benefits such as added flexibility, real-time data and reporting.
- Hybrid working models. BPO vendors that provide traditionally outsourced business processes, such as call centers, are now able to work remotely.
- Nearshoring operations becoming more popular. Technology such as video conferencing, AI-enabled tools and robotic process automation (RPA) is driving down costs, enabling vendors that nearshore business processes to become more cost-effective.
BPO vendors, however, are contending with disruption as well, as the practice of business process outsourcing could be at least partially displaced in upcoming years by technology.
RPA and AI can handle some of the business processes now frequently outsourced, and these technologies can often perform those functions at lower costs and higher speeds.
Organizations are deploying RPA at increasing rates in an effort to boost efficiency and accuracy. Learn how RPA is adding AI to make it even more resilient and nimble.