competitive differentiation
What is competitive differentiation?
Competitive differentiation is a strategic positioning tactic an organization can undertake to set its products, services and brands apart from those of its competitors.
To make an offering compelling in the marketplace, an organization must clearly articulate to consumers the benefits of a product, service or brand and contrast its unique qualities with other competing products.
The goal of competitive differentiation is to have the customer perceive an organization's offering as being superior when compared to other similar offerings.
Key elements of competitive differentiation
Competitive differentiation centers around three key elements: unique value proposition, target market identification, and product or service features. Here's a closer look at each of these components.
Unique value proposition
A unique value proposition is the core foundation of competitive differentiation. It represents the distinct benefits and value that a business offers to its target market. By identifying what sets them apart from competitors, businesses can position themselves favorably in the customer's mind.
For example, Apple's value proposition centers on sleek design, user-friendly interfaces and seamless integration across their product ecosystem, distinguishing them from other technology companies.

Target market identification
Understanding the specific needs and preferences of a target market is crucial for effective differentiation. By tailoring products or services to suit those needs, businesses can create a unique selling point (USP) that resonates with their target audience.
For instance, Tesla's electric vehicles cater to environmentally conscious consumers who prioritize sustainability and cutting-edge technology.
Product or service features
Highlighting distinctive features is another critical aspect of competitive differentiation. These features might include specific functionalities, metrics, or innovative design elements that provide a competitive advantage.
Consider the example of Dyson, a company renowned for its vacuum cleaners' innovative technology and superior suction power, which sets them apart from traditional vacuum brands.
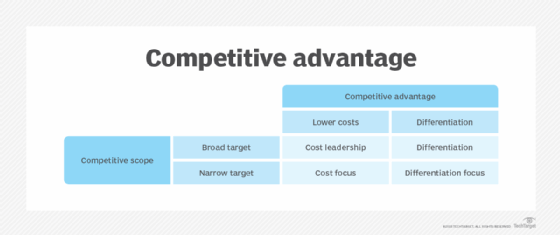
Strategies for developing competitive differentiation
To effectively differentiate themselves from competitors, businesses can employ several strategies starting with innovation and product development.
Continuous innovation ensures that businesses stay ahead of the competition. By consistently improving and introducing new features, products or services, companies can enhance their competitive differentiation.
Another strategy for competitive differentiation is quality and customer service. Providing high-quality products and exceptional customer service can significantly contribute to a company's competitive differentiation.
Finally, branding and reputation management are key strategies for implementing competitive differentiation. Building a strong brand identity and reputation helps establish competitive differentiation.
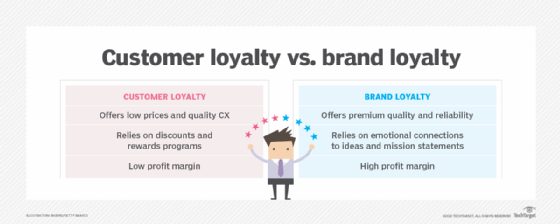
Companies like Coca-Cola have successfully differentiated themselves through their iconic brand image and emotional connections with consumers, creating long-lasting brand loyalty.
Benefits of competitive differentiation
There are several benefits that businesses can reap from competitive differentiation:
- Increased customer acquisition. Effective differentiation helps attract new customers as it sets a business apart from competitors. By clearly communicating their unique value proposition, companies can attract customers who resonate with their distinct offerings.
- Customer retention and loyalty. Competitive differentiation also cultivates customer loyalty. By consistently delivering on their unique value proposition, businesses can create an emotional connection with customers, strengthening brand loyalty and increasing customer retention.
- Pricing power and profitability. Differentiation can often support a premium price point for products or services, thus enhancing profitability. When customers perceive exceptional value, they are often willing to pay a premium.
Challenges in achieving competitive differentiation
While competitive differentiation offers significant advantages, there are challenges businesses must navigate:
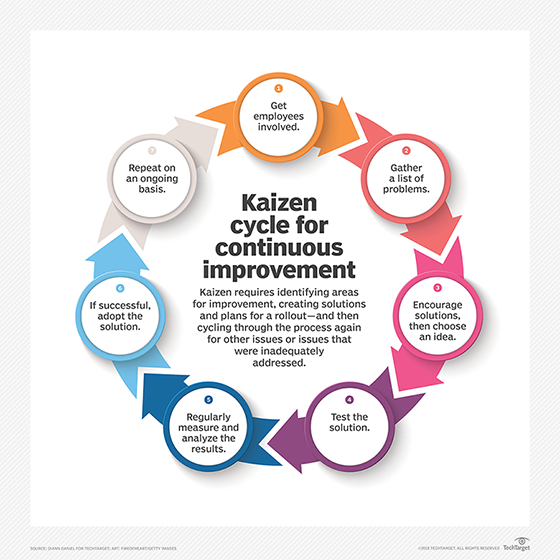
- Continuous improvement and adaptation. Businesses must embrace a culture of continuous improvement and adaptation to stay ahead. Markets and customer preferences change over time, and successful differentiation requires businesses to evolve alongside them.
- Competitive analysis and market research. To differentiate effectively, businesses need to conduct thorough competitive analysis and stay attuned to market trends. Understanding competitors' strategies and customers' evolving preferences helps companies refine their differentiation and seize new opportunities.
- Balancing differentiation with market demand. While differentiation is crucial, it must align with market demand. Businesses should ensure that their unique selling propositions meet customer expectations and solve their pain points. Avoiding excessive complexity and focusing on meaningful differentiation are essential.
Competitive differentiation is the key to standing out in today's competitive business landscape. By focusing on unique value propositions, understanding target markets and highlighting distinctive features, businesses can gain a competitive edge.
However, businesses must balance differentiation with market demand and continuously adapt to remain competitive. By embracing the power of differentiation, companies can position themselves for sustainable success in their respective industries.
Get to know the difference between personalization vs. segmentation marketing strategies and the most effective ways to connect with customers. Learn about the challenges involved in creating a culture of innovation, such as gauging an organization's readiness to accept risk and establishing guardrails.








