initialization vector
What is an initialization vector (IV)?
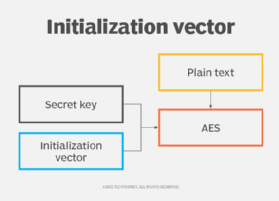
An initialization vector (IV) is an arbitrary number that can be used with a secret key for data encryption to foil cyber attacks. This number, also called a nonce (number used once), is employed only one time in any session to prevent unauthorized decryption of the message by a suspicious or malicious actor.
Importance of an initialization vector
The use of an IV prevents the repetition of a sequence of text in data encryption. Specifically, during encryption, an IV prevents a sequence of plaintext that's identical to a previous plaintext sequence from producing the same ciphertext. If an attacker can view the same encrypted data multiple times, they get clues to decrypt and interpret the original values. That's why encrypted ciphertext data is vulnerable to theft or compromise.
An IV is meant to prevent this from happening. A random unique nonce removes the need for repetition during encryption. The hacker cannot view the same encrypted information over and over, which makes it more difficult for them to decrypt the message via, say, a dictionary attack.
Properties of an ideal initialization vector
In a cryptographic algorithm, an IV is used as a "starting state." Adding the IV to the cipher hides patterns in the encrypted data that may allow a hacker to decrypt it by guesswork or trial and error.
The ideal IV is a random or pseudorandom number. It must also be nonrepeating. Both randomness and nonrepetitiveness are crucial to prevent attackers from finding patterns in similar parts of the encrypted message and then using this information to decrypt the message.
The IV need not be secret. In fact, the destination computer usually knows the IV so it can decrypt the encrypted data when it receives it. Thus, the IV would be agreed on in advance by both the sender and the recipient. In addition, the IV can be transmitted independently or included as part of the session setup prior to message exchange.
The IV length in terms of the number of bits or bytes depends on the encryption method. In most cases, the length is comparable to the length of the encryption key or block of the cipher being used.
Ways to make the IV available to a recipient
For a recipient to decrypt the encrypted message, they must know the IV. There are many ways to make the IV available to the recipient to facilitate decryption. One way is to transmit it along with the ciphertext. Another way is for both the sender and recipient to agree on the IV during the key handshake or exchange.
The recipient can also discover the IV by calculating it incrementally or by measuring parameters like current time, using the sender's or recipient's address, or by using the packet or cluster number.

Use of IVs in block ciphers and stream ciphers
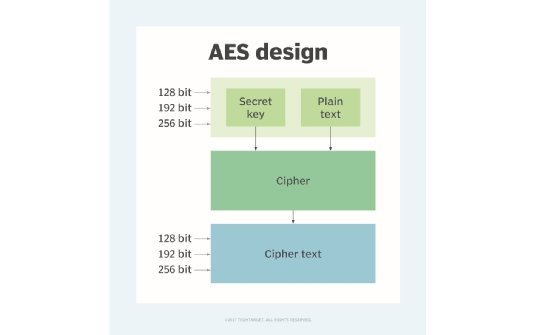
A block cipher is a way to encrypt data in blocks simultaneously to produce ciphertext. In contrast, a stream cipher encrypts and decrypts data one bit at a time. Both stream and block ciphers use a symmetric key and algorithm for data encryption. IVs are implemented differently in both types of ciphers.
In the Electronic Code Book (ECB) mode, which is a simple mode of operation with block ciphers, the same plaintext is always encrypted with the key into identical ciphertext. In other words, encryption of the same plaintext with the same key generates the same ciphertext, leaving the message vulnerable to compromise. Adding an IV to the plaintext's first block (XOR) addresses this problem and increases data security and integrity.
In stream ciphers, an IV is added to the keyed internal secret state. After this, multiple cipher rounds are executed before the first bit of output is released. Despite the presence of the IV, stream ciphers are not entirely secure.
Initialization vector in WEP IV
The Wired Equivalent Privacy or WEP algorithm is part of the 802.11 standard that describes communications in wireless local area networks (LANs). WEP relies on a secret key that is shared between a mobile station and an access point and is used to encrypt data packets before they are transmitted.
WEP uses the RC4 encryption algorithm, which is a stream cipher. It performs an integrity check to ensure that packets are not modified in transit. For this, it uses a 24-bit IV. The IV is included in the packet in the cleartext part of a message. Its goal is to ensure that two ciphertexts are not encrypted with the same key stream. However, because the IV is short, the same key stream is often reused, which allows hackers to perform statistical attacks to recover the plaintext and decrypt traffic.
WEP is vulnerable to many kinds of attacks, including passive attacks to decrypt traffic, active attacks to inject malicious traffic and table-based attacks in which attackers can easily decrypt all packets using the same IV. Due to such weaknesses, the WEP is no longer a popular encryption algorithm.
Using an initialization vector in different modes
Different cipher modes are used to mask the patterns within the ciphertext to prevent attackers from guessing it. Here's how an IV is used in various modes.
Cyber Block Chaining (CBC) Mode
CBC uses an IV to prevent having the same plaintext result in the same (guessable) ciphertext. It's important that the IV is random and unique. Otherwise, attackers may be able to guess the ciphertext and easily decrypt the data.
IV type: random and unpredictable
Ciphertext Feedback (CFB) Mode
In CFB, the IV is used as a source of the stream generated by the cipher. As with CBC, the IV must be random to prevent predictability and maintain the data's confidentiality and integrity.
Moreover, the IV must not be reused because doing so can reveal information about the common blocks shared by two messages, thus allowing a hacker to decrypt a subsequent message.
IV type: random and unpredictable
Counter and Output Feedback (OFB) Modes
These modes make a block cipher into a synchronous stream cipher. The cipher is initialized with an IV. When 12 bytes are allocated to the IV and 4 bytes to the counter, it enables the encryption of a message of length 2^32 blocks. As with the other modes, reusing the IV will result in the reuse of the key bitstream, increasing the chances of unauthorized decryption by an eavesdropper.
IV type: unique (counter)
Galois/Counter (GCM) Mode
This mode protects both plaintext and additional authenticated data (AAD). But again, IV uniqueness determines authentication and data security. GCM uses AES encryption with an IV length of 16 bytes. The first 12 bytes are assigned to the IV and the remaining 4 bytes to the nonce counter.
IV type: unique IV (12 bytes) + unique counter (4 bytes)
Explore the differences between symmetric vs. asymmetric encryption and learn the ABCs of ciphertext exploits.
