intellectual property (IP)
What is intellectual property (IP)?
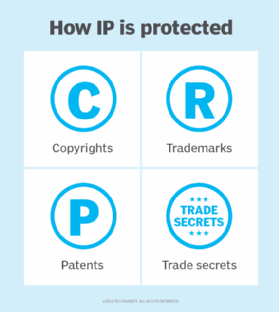
Intellectual property (IP) is a term for any intangible asset that is the product of someone's mind. IP is something proprietary that has value but doesn't exist as a physical object. Examples of intellectual property include designs, concepts, software, inventions, trade secrets, formulas, brand names and works of art. Intellectual property can be protected in law by copyright, trademark, patent or trade secret.
Types of intellectual property
The right of a person to own and receive the benefit from their creative works has long been established. These laws were first seen in the 15th century and enshrined in many legal systems in the early 18th century. Many nations now look to the United Nations' World Intellectual Property Organization (WIPO) for guidance on IP law.
While there are many types of creations that can be protected, the law provides four main types of protection: patents, copyright, trademarks and trade secrets. The WIPO broadly divides these into copyrights and industrial property.
Copyright protects creative works. This includes writing, pictures, sound recording, and video. Many computer programs are also protected by copyright to prevent illegal reproduction.
Patents protect the design of a device or system. This can include how an electrical or mechanical system works, the functioning of software or certain computational algorithms. Industrial design often falls under patent protection.
Trademarks protect the distinctive signs of a person or company. This might include names, branding or indicating icons. A product trade dress (packaging and looks) is often protected by trademark. Geographical indications protect goods produced in a certain region; for example, Champaigne coming from the Champagne region of France or Scotch whisky being made in Scotland.
A trade secret is any confidential information that has value. They can be bought and sold. To be a trade secret it generally must be valuable because it is secret, only known by a limited selection of people, and be reasonably protected. Examples of trade secrets might be a customer list, a business plan, gathered data or a process/recipe like a recipe.
Threats to copyrights
Artificial intelligence and machine learning are currently a major area of concern in intellectual property rights. These systems might be trained using protected copyrighted works, leading to the question: Should the copyright owners be compensated for their works being used in these training sets? These systems can produce extremely similar or sometimes almost exact copies of the original works.
What about the use of generative AI to produce a work "in the style of" a famous creator? For example, what are the moral and legal implications of asking a large language model (LLM) to write a book in the style of J.K. Rowling, or a text-to-image generator to create a character in the style of Hayao Miyazaki? Would this be the same or different as asking a human to create such a work?
Another area is the rights of a person to their likeness or voice. Generative AI and deep fakes can easily reproduce how a person looks and sounds. The exclusive use of your own image is called the right of publicity. While it's widely recognized that such images can't be used commercially without permission the right of publicity is not national law in the United States.
Threats to industrial property
Some companies might infringe on patents or trademarks. These companies might produce copycat products that almost exactly replicate the original.
Hacking groups are highly motivated to access the protected trade secrets of corporations. Nation state sponsored groups might be trying to access these to gain knowledge of industrial capacity or capability of systems. Ransomware groups might be trying to extort companies by threatening to release their trade secrets to the public.
Although most large corporations protect themselves from industrial espionage, theft of intellectual property is often a result of insider threats. In a study conducted by Peter Toren, out of 120 prosecutions for theft of trade secrets, more than 90 percent of the defendants were insiders who had access to the trade secrets because they were employees of the victim or worked for a vendor or contractor of the victim.
Toren offers the following best practices for protecting your organization's intellectual property:
- Have employees and vendors sign a code of conduct and confidentiality and nondisclosure agreements (NDA) before beginning work.
- Compartmentalize electronically stored confidential information and make it accessible only on a need-to-know basis.
- Immediately revoke a departing employee's ability to access any proprietary information.
- Conduct exit interviews with employees and require them to attest that they are not taking any confidential or proprietary information to a new employer.
- If suspicious activity on the part of a departing employee is uncovered, consider conducting a full-scale investigation of the former employee's recent conduct.
Crimes against intellectual property are big business. Check out this practical approach on how to tackle intellectual property crime.
