intelligent agent
What is an intelligent agent?
An intelligent agent is a program that can make decisions or perform a service based on its environment, user input and experiences. These programs can be used to autonomously gather information on a regular, programmed schedule or when prompted by the user in real time. An intelligent agent is also referred to as a bot, which is short for robot.
Typically, an agent program, using parameters the user has provided, searches all or some part of the internet, gathers information the user is interested in, and presents it to them on a periodic or requested basis. Data intelligent agents can extract any specifiable information, such as keywords or publication date.
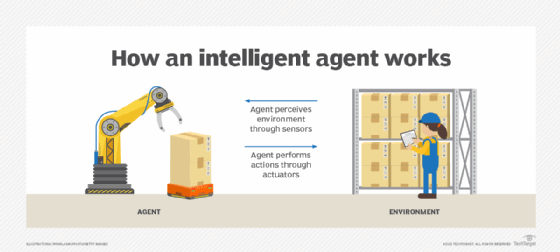
Agents that use artificial intelligence (AI) and machine learning use sensors, such as microphones and cameras, to collect user input. They also use effectors, such as fingers and wheels, to affect their environment, as well as actuators, such as speakers and screens, to deliver agent output. The practice of having information brought to a user by an agent is called push notification technology.
Common characteristics of intelligent agents are adaptation based on experience, real-time problem-solving, analysis of error or success rates, and the use of memory-based storage and retrieval.
This article is part of
A guide to artificial intelligence in the enterprise
For enterprises, intelligent agents can be used in data science applications such as data mining and data analytics, as well as for customer service and support. Consumers use intelligent agents to compare the prices of similar products and get notifications when a website update occurs.
Intelligent agents are also similar to software agents, which are autonomous computer programs.
Types of intelligent agents
Types of intelligent agents are defined by their range of agent functions and capabilities and their degree of intelligence:
- Simple reflex agents. These agents function in a current state, ignoring past history. Responses are based on the event-condition-action rule, or ECA rule, where a user initiates an event and then the agent refers to a list of preset rules and preprogrammed outcomes.
- Model-based reflex agents. These agents take action in the same way as a reflex agent, but they have a more comprehensive view of their environments. A model of the world is programmed into the internal system that incorporates the agent's history.
- Goal-based agents. These agents, also referred to as rational agents, expand on the information that model-based agents store by also including goal information or information about desirable situations.
- Utility-based agents. These agents are similar to goal-based agents, but they provide an extra utility measurement that rates each possible scenario on its desired result, and then choose the action that maximizes the outcome. Rating criteria examples include the probability of success or the resources required.
- Learning agents. These agents have the ability to gradually improve and become more knowledgeable about an environment over time through an additional learning algorithm or element. The learning element uses feedback on performance measures to determine how performance elements should be changed to improve gradually. This concept describes how an AI system should operate.
Examples of intelligent agents
AI assistants such as Alexa and Siri are examples of intelligent AI agents that use sensors to perceive a user request and automatically collect data from the internet without the user's help. They can gather information about their observable environments, such as weather and time.
Google Assistant is another example of an intelligent AI agent. It uses machine learning and natural language processing technology to answer users' questions and perform tasks, such as calling contacts stated in voice commands.
Autonomous vehicles can also be considered intelligent robotic agents. They use sensors, Global Positioning System navigation and cameras for reactive decision-making in the real world to maneuver through traffic.
Tech vendors are now developing more autonomous AI agents that require less human intervention and oversight, as demonstrated by OpenAI's release of GPT-4. A fully autonomous agent would be considered artificial general intelligence, where AI agents are sentient and don't require guidance from human agents at all, but that's currently theoretical and not yet realistic.
Learn about artificial intelligence in the enterprise, including the role intelligent agents are expected to have as AI continues its mainstream prominence.