intelligent system
What is an intelligent system?
An intelligent system is an advanced computer system that can gather, analyze and respond to the data it collects from its surrounding environment. It can work and communicate with other agents, such as users or other computer systems. It can also learn from experience and adapt according to current data. An intelligent system might also support remote monitoring and management.
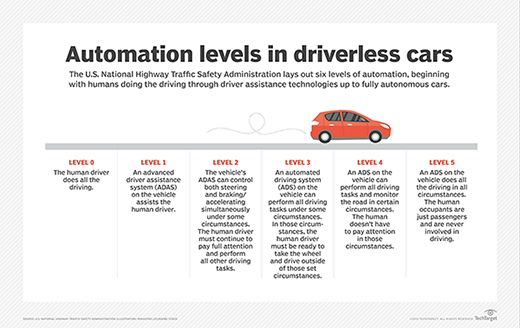
There is no single definition for an intelligent system. The term is applied in different ways by various sources. For example, a Roomba vacuum is often referred to as an intelligent system. However, some could argue that its limited capacity to learn, such as its inability to avoid the same obstacle, disqualifies it from this category. On the other hand, most would consider a self-driving car to be an intelligent system or a valid attempt at an intelligent system.
There is no single standard that defines an intelligent system. It is often determined by degrees of intelligence rather than a checklist of characteristics. Martin Molina, a professor in the department of artificial intelligence at the Technical University of Madrid, offered the following description of an intelligent system in his paper "What is an intelligent system?" (published February 2022):
An intelligent system (1) operates in an environment with other agents, (2) possesses cognitive abilities such as perception, action control, deliberative reasoning or language use, (3) follows behavioral principles based on rationality and social norms and (4) has the capacity to adapt through learning.
Molina added that his definition should not be taken as a "rigid characterization to determine whether a system is intelligent or not." Instead, the definition outlined the usual characteristics that might be present in an intelligent system. For example, a system might be considered intelligent if it has perception and can control action, even if it doesn't possess deliberative reasoning or a capacity to learn.
He further stated that the "concept of intelligent system has emerged in information technology as a type of system derived from successful applications of artificial intelligence." In fact, AI is commonly cited as a central characteristic of any intelligent system. Molina also said that one of the most important aspects in the construction of an intelligent system is the selection of AI methods which provide the system with the cognitive abilities necessary to function as a complete system.
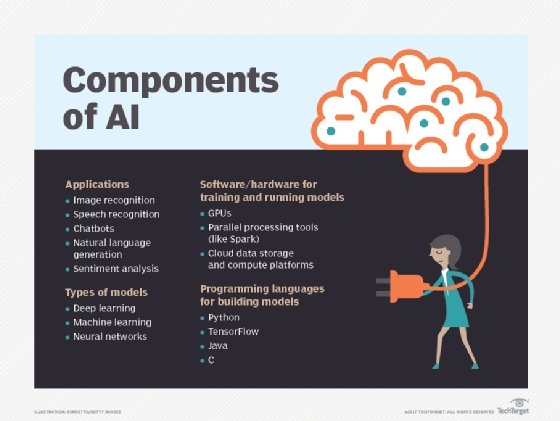
However, an intelligent system is not the same thing as AI, although the terms are sometimes used interchangeably. With AI, computers and other machines attempt to simulate human intelligence, but its presence does not automatically imply an intelligent system. For example, a computer running an AI-based application does not mean that the computer itself is an intelligent system, although it might contribute to such a system as one of its agents.
What are examples of intelligent systems?
Intelligent systems are omnipresent and offer endless possibilities. They can benefit many industries and affect both our personal and professional lives. The following table provides examples of how intelligent systems can be used in different industries. This is just a glimpse into the potential application of intelligent systems.
| Industry | Examples |
| Transportation |
Traffic control systems, traffic flow analysis and congestion monitoring, delivery fleet coordination, autonomous cars, public transportation systems, accident prevention |
| Aerospace |
Airline cockpit controls, drones, spacecraft monitoring, mission planning, advanced guidance and navigation, air traffic control |
| Human identification |
Visual surveillance, biometric monitoring (such as face or fingerprint recognition), character or speech recognition |
| Manufacturing |
Advanced robotics and automation, autonomous systems, diagnostics and repairs, inventory management, visual inspection |
| Education |
Tutoring, identifying student learning patterns, question and answer systems, course planning and scheduling, interactive online education |
| Climatology |
Forecasting, advance warning systems (such as tornados or tsunamis), field research and monitoring, satellite imaging and analysis |
| Retail |
Online shopping recommendations, point-of-sale (POS) terminals, digital signage, product planning and delivery |
| Home automation |
Smart appliances, climate and lighting control, entertainment |
| Public health |
Medical care, medical diagnostics, telemonitoring, health crisis management (such as the COVID-19 pandemic), violence pattern detection, biomedical engineering |
Built-in intelligence is an integral component of the internet of things (IoT). IoT devices have the ability to automatically transfer data over a network without human interaction. Used with AI and 5G, IoT can create intelligent systems with the potential to impact our lives on every level.
See also artificial general intelligence, IT automation and Alex Wissner-Gross' TED talk, "A new equation for intelligence."