pixel
What is a pixel?
The pixel -- a word invented from picture element -- is the basic unit of programmable color on a computer display or in a computer image. Think of it as a logical -- rather than a physical -- unit.
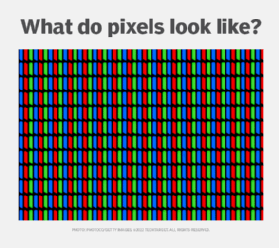
Pixels are the smallest unit in a digital display. Up to millions of pixels make up an image or video on a device's screen. Each pixel comprises a subpixel that emits a red, green and blue (RGB) color, which displays at different intensities. The RGB color components make up the gamut of different colors that appear on a display or computer monitor.
When referencing the resolution of a display, numbers like 1920 x 1080 refer to the number of pixels.
How do pixels work, and how are they used?
The number of pixels determines the resolution of a computer monitor or TV screen, and generally the more pixels, the clearer and sharper the image. The resolution of the newest 8K full ultra-high-definition TVs on the market is approximately 33 million pixels -- or 7680 x 4320.
The number of pixels is calculated by multiplying the horizontal and vertical pixel measurements. For example, HD has 1,920 horizontal pixels and 1,080 vertical pixels, which totals 2,073,600. It's normally shown as 1920 x 1080 or just as 1080p. The p stands for progressive scan. A 4K video resolution, for example, has four times more pixels than full high definition (HD), and 8K has 16 times more pixels than 1080p.
Other common display resolutions include the following:
- 480p, which is standard definition, is 640 x 480 and is often used for small mobile devices;
- 720p, which is HD, is 1280 x 720;
- 1440p, which is 2550 x 1440 and considered quarter HD (QHD), is often used for PC gaming monitors; and
- 4K video resolution, which is ultra HD, is 3840 x 2160 pixels.
The specific color information that a pixel describes is some blend of three components of the color spectrum -- RGB. Up to three bytes of data are allocated to specify a pixel's color, one byte for each major color component. A true color or 24-bit color system uses all three bytes. However, many color display systems use only one byte, which limits the display to 256 different colors.
A bitmap is a file that indicates a color for each pixel along the horizontal axis or row -- called the x coordinate -- and a color for each pixel along the vertical axis -- called the y coordinate. A GIF file, for example, contains a bitmap of an image along with other data.
Pixels are also either backlit by an additional panel or are individually lit. An LCD TV screen illuminates all pixels using an LED backlight. If the display is mostly black on an LCD screen, but only a single pixel needs to be lit, the whole back panel still must be lit. This leads to light leakage in the display. This is more noticeable during the credits of a movie, for example, where there's a slight glow around the white letters against the black background.
OLED displays, by contrast, don't need a backlight, as each individual pixel illuminates itself. This means when one pixel needs to be lit, no light is leaked to the surrounding pixels. In the movie credits example, this means an OLED display won't have the same light glow around each of the credits as it would in an LCD screen. OLEDs typically have better contrast, black levels and viewing angles than LCD screens but also suffer from burn-in. OLED screens can also be folded or bent, which is a feature in many modern smartphones.
Each pixel is a square that's arranged in a uniformly two-dimensional grid. Each pixel has a logical address.
How big is a pixel?
The physical size of a pixel depends on the set resolution for the display screen. If the display is set to its maximum resolution, the physical size of a pixel will equal the dot pitch, or the dot size, of the display. But if the resolution is set to something less than the maximum resolution, a pixel will be larger than the physical size of the screen's dot -- that is, a pixel will use more than one dot.
What is a megapixel?
A megapixel (MP) is a million pixels. The term megapixel comes up most often in photography; however, screen resolutions can be measured in megapixels. For example, 4K is approximately 12 MP and 1080p is 2.1 MP.
In photography, megapixels typically refer to the resolution of an image and the number of image sensor elements in digital cameras. For example, the Sony A7 III camera can take 24.2 MP photos, which is 24,200,000 pixels.
Smartphones typically have 12 MP cameras, while interchangeable-lens cameras typically have anywhere from 20-60 MP. Smaller action cameras like GoPros or Insta360 cameras can range from 12-48 MP.
The difference between PPI and DPI
Screen image sharpness is sometimes expressed as pixels per inch (PPI). PPI and dots per inch (DPI) are two similar and commonly conflated concepts. PPI is the number of pixels contained in one inch of a digital image. By contrast, DPI is the number of printed dots within one inch of a printed image. The main difference between the two terms is that PPI is the quality of a digital image displayed on-screen, while DPI is the quality of a physical, printed image. The dots in DPI refer to the number of printed dots of ink.
Although DPI is technically a term used for printing physical images, it has been misused so often that it's synonymous with PPI.
According to Sony, there are two reasons for the confusion between the two terms. One reason is that even though PPI refers to digital image quality, it still has an effect on an image when printed out, as prints with a higher MP count may have finer details. The second reason is that some professional print services mistakenly request images be a specific DPI in order to be printed, when they should instead be using the term PPI.
Learn more about how 4K is being used in the enterprise and where it makes sense.
