dense wavelength-division multiplexing (DWDM)
What is dense wavelength-division multiplexing (DWDM)?
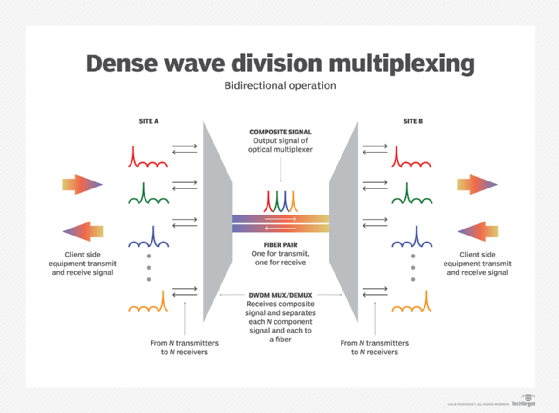
Dense wavelength-division multiplexing (DWDM) is an optical fiber multiplexing technology that is used to increase the bandwidth of existing fiber networks. It combines data signals from different sources over a single pair of optical fiber, while maintaining complete separation of the data streams.
A separate light wavelength carries each signal, and the dense in DWDM refers to its ability to accommodate up to 80 different wavelengths. Each wavelength is about 0.8 nanometer wide and shares a single optical fiber.
Fiber optic cables now commonly form the backbone of carriers' interoffice networks, representing the standard for the telecommunications infrastructure. DWDM enables enormous amounts of data to traverse a single network link by creating multiple virtual fibers, significantly multiplying the capacity of the physical medium.
As data flows through distinct wavelengths, the streams or channels do not interfere with each other. This approach helps maintain data integrity. As a result, this enables security-related partitioning or separate tenants in the same data center.
Because of its ability to handle so much data, DWDM is popular with telecommunications and cable companies. It is an integral part of their core networks. DWDM is also highly suitable for anyone running densely populated data centers, such as hyperscale cloud service providers operating infrastructure as a service or colocation providers with dense multi-tenant spaces.
DWDM is a predecessor to a similar technology: time-division multiplexing (TDM), which telecommunications operators use to routinely transmit information at 2.4 gigabits per second (Gbps) on a single fiber. Some also deploy equipment that quadruples that rate to 10 Gbps. However, demand for high-bandwidth applications created capacity demands that exceeded traditional TDM limits.
As a result, DWDM was developed to multiply the capacity of a single fiber.
How does dense wavelength-division multiplexing work?
DWDM has tighter wavelength spacing that helps fit more channels onto a single fiber. It is best used in systems with more than eight active wavelengths per fiber. Because DWDM finely dices the spectrum, it can easily fit over 40 channels into the C-band frequency range.
Dense wavelength-division multiplexing in optical fiber systems deployed today achieves a throughput of 100 Gbps. When DWDM is used with network management systems and add-drop multiplexers, carriers are able to adopt optically based transmission networks. This approach helps meet growing bandwidth demand at a significantly lower cost than installing new fiber.
DWDM wavelength channels can be implemented through an array of infrared laser beams. Each channel carries 100 Gbps and 192 channels per fiber pair, translating to 19.2 terabits per second capacity per pair. Because the channels are physically distinct and don't interfere with each other due to light properties, each channel can use different data formats and transmit at different data rates.
For example, Internet Protocol (IP) over DWDM permits 100 megabits per second and 10 Gbps data channels to share an optical fiber. This is in addition to sharing it with an Optical Carrier 192 Synchronous Optical Network data channel.
What is wavelength-division multiplexing?
Wavelength-division multiplexing (WDM) forms the foundation of DWDM. It is a technology used to modulate several data streams. For example, it helps control optical carrier signals of fluctuating wavelengths or colors of laser light onto a single optical fiber.
WDM enables bidirectional communication and signal capacity multiplication.
What is the difference between CWDM and DWDM?
Coarse wavelength-division multiplexing (CWDM) is a related technology that also uses laser beams to transmit information over fiber optic cables. However, it uses less sophisticated electronics and photonics, which make CWDM channels much wider than DWDM channels.
CWDM has nearly 100 times wider channel spacing needed for frequency stability.
This means that CWDM supports fewer channels than DWDM, accommodating up to 18 channels. However, the optical interface components CWDM uses do not have to be as precise as DWDM components. As a result, CWDM is usually much cheaper to deploy than DWDM and more tolerant of low-grade fiber, single-fiber strands and multimode fiber.
Both CWDM and DWDM optical transport solutions come in the form of active or passive systems. Whenever it is inactive or not powered, the CWDM or DWDM transceiver is inside a device, such as a router or switch.
An IP switch with a channelized small form-factor pluggable (SFP) optic transceiver tuned into a specific CWDM or DWDM wavelength is an excellent example of this. In this case, the output from the channelized SFP transceiver will connect to a corresponding passive multiplexer.
This approach helps combine and redistribute -- or multiplex and demultiplex -- different wavelength signals. Because the channelized CWDM or DWDM SFP transceiver exists inside the router or switch, its WDM functionality is inherently embedded within the device.





