kill switch
What is a kill switch?
A kill switch in an IT context is a mechanism used to shut down or disable a device or program.
The purpose of a kill switch is usually to prevent theft of a machine or data or shut down machinery in an emergency. The degree to which a kill switch limits, alters or stops an action or activity depends on the production, process or program it is intended to protect.
How do kill switches work?
Kill switch is a broad term when it comes to the types of technology, software and tools used to create and facilitate it. In manufacturing, for example, a factory might use a kill switch -- also called a big red button -- to shut down machinery if a worker is in danger. Kill switch software, on the other hand, can sometimes include software-encoded kill switches such as anti-piracy mechanisms.
A kill switch's form, use and function can vary significantly, depending on the industry and business. For instance, when a business detects a data breach, it may encourage the network administrator to execute security protocols other than a kill switch based on the severity of the breach.
The big red button is a mechanical version of the same mechanism.
How are kill switches used?
Due to the broadness of the term, kill switches have a wide range of applications and uses that vary greatly based on their medium and objective. Below are a few of the more common uses and applications of a kill switch for cybersecurity purposes and in other applications and industries.
Kill switch software
Platforms for smartphones and other devices often encode software-based kill switches -- sometimes called virtual kill switches -- as an antimalware measure to protect devices from infected apps. Microsoft, Google and Apple are examples of companies that include kill switches in their products. After detecting a problem or discovering a product has been stolen, for example, a user or admin can send instructions to devices to alter or remove an offending application, for instance, or even shut down a device and make it unusable to a thief.
Cybersecurity mechanism
One of the most common uses of a kill switch is as a cybersecurity mechanism. In 2020, the number of digital assets exposed by cyber criminals rose by 141% from the previous year, according to Risk Based Security, resulting in approximately 37 billion compromised records. As a result, kill switch software has become an incredibly important tool for individuals and businesses to protect personal information and safeguard confidential data.
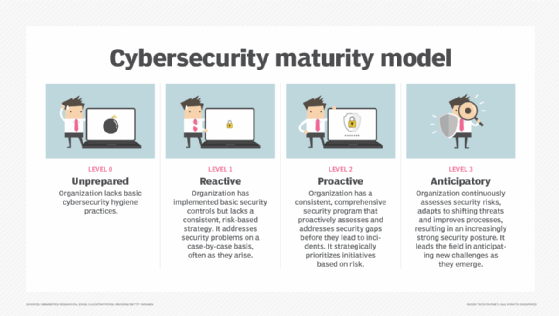
Unlike other cybersecurity mechanisms, kill switch software is a reactive tool, not a preventive or proactive measure. Its goal, in most cases, is to limit the degree of damage of a cyber attack should it be detected by a defending organization, other cybersecurity applications or the kill switch software itself. Oftentimes, malware acts so quickly that some cybersecurity programs and VPNs come with a kill switch built in. But security vendors almost always design these to be used on a localized basis (i.e., on laptop or in an application).
The reason: Activating a kill switch can be extremely disruptive and costly, especially if performed on a business critical feature. For example, if an activated kill switch shuts down a company server, it immediately halts all server-dependent activities, even those that are not affected by, say, malware. So, a kill switch that is not limited to a localized function can prove disruptive to critical infrastructure depending on the sensitivity of its trigger conditions.
Furthermore, having a network or server kill switch with an automatic trigger dramatically increases the risk of accidental detonation. As a result, enterprise IT managers control most large-scale kill switch software to avoid expensive accidents. They control the sensitivity levels of the trigger conditions, and the degree that the kill switch stops information transfers and other activities upon detonation.
Kill switches and communications
Defending companies may initiate a kill switch to block all external communications. This is typically the first of several steps taken to contain cyber attackers after the detection of a cybersecurity incident. By blocking communications, victims of a cyber attack can disrupt the connection between their own assets and cybercriminals.
The issue with this technique is that cybercriminals have become so sophisticated in their hacking methods, they can often disguise their communications -- sometimes through legitimate channels like an employee account. Traditionally, kill switches would assume all user activity on the inside of enterprise was safe. However, the more advanced kill switch systems of today will attempt to decipher whether certain activity is legitimate or fraudulent -- regardless of whether or not the activity is using sanctioned login credentials -- to better fight against credential harvesting tactics such as phishing and pass-the-hash attacks.
Kill switch malware
Kill switches aren't just used to defend organizations. Cybercriminals can use them as part of a cyber attack as well.
Even when used by a cybercriminal, a kill switch is typically still a safety mechanism. If malware authors build a kill switch into a virus, for example, they can program the malware to trigger an immediate response to specific situations. So, for example, kill switch malware may be used to shut down a cybercriminal's operations should they be caught, tracked or compromised.
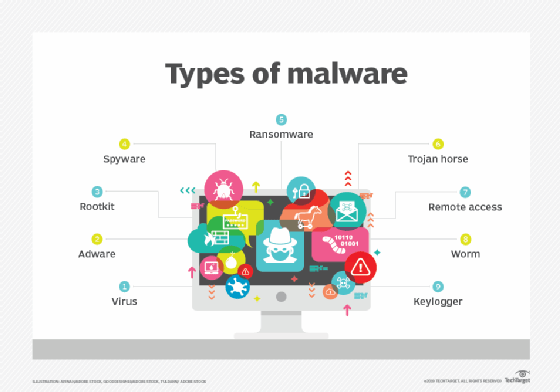
A malware kill switch would not only cease all external communications from the malware, but it would also remove the virus from all infected systems, thereby erasing the malware's existence. The kill switch would halt and delete all programs, documents and log files created by the hackers to eliminate their digital footprint. This kind of kills switch is part of what makes malware such a difficult threat to contain and control.
Additional kill switch applications
A wide variety of machinery both inside and outside the IT world -- including car ignition systems, boat motors, industrial machines and gas pumps -- use kill switches. A kill switch for vehicles and machinery is sometimes called a "dead man's switch" because its purpose is to automatically shut the vehicle or machine down if the operator becomes incapacitated. This is different from the aforementioned big red button, which often has to be enabled by an individual.
Kill switches in asset-intensive and industrial markets, such as dead man's switches and big red buttons, focus on user safety as opposed to asset safety. They must be regularly inspected to ensure their safety features remain usable in case of emergency.