line of sight (LOS)
What is line of sight?
Line of sight (LOS) is the imaginary line between an observer and the target. In communication, line of sight is the direct path from a transmitter to the receiver and the obstructions that may fall in that path. A clear line of sight is important to high-speed communication.
Line of sight is the direct path between two points. It's called the "line of sight" because if a person was standing at one point, the LOS would be the path they look along. If an object were blocking the view, it would be considered out of sight or an obstructed line of sight.
The concept of lines of sight have been important for much of history. Imagine a guard atop a watchtower. His high-up position would give him an unobstructed view, or clear lines of sight across a large area. If he lit a signal fire, everyone in the area would have a clear line of sight to see the fire and raise the alarm.
The curvature of the earth has been the limiting factor of lines of sight. As two objects get further apart, the earth will obstruct the LOS between them. Eventually it will disappear over the horizon and break the LOS.
Line of sight in wireless communication
Line of sight is a vital factor in wireless communication. Some forms of wireless transmission are completely blocked if anything comes between the transmitter and receiver. Other forms of transmission can penetrate less dense objects, like walls and building, but are blocked by large objects, like mountains.
Most wireless transmission uses radio waves, which travel in straight lines from the transmitter. Putting the transmitter up high will give it a clearer line of sight. Just like in visual lines of sight, the curvature of the earth will eventually block a radio wave. This sets the limit on how far any radio tower can transmit on its own.
Signal reflection or refraction can be used to extend the useable range of a radio signal farther than the line of sight. Reflecting radio waves off the earth's ionosphere at night was an early method to extend radio transmission beyond LOS.
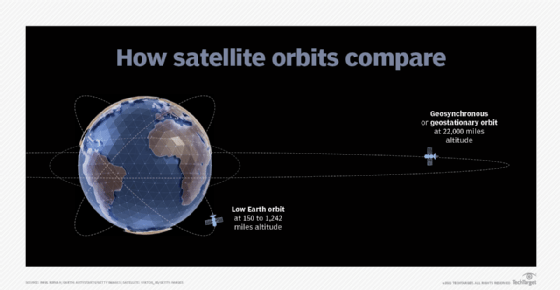
Communication satellites revolutionized wireless transmission. Their position high above the earth gives them a clear line of sight to terrestrial communication towers. A tower transmits to a satellite, and the satellite retransmits the signal to another tower beyond the first tower's LOS. The higher a satellite's orbit, the more of the earth it can cover. A single satellite in geostationary orbit has LOS over half the earth's surface. Low earth orbit (LEO) satellites may only cover a relatively small area.
Satellites often work together in constellations to cover the needed area. Satellites have tradeoffs between the greater cost of higher orbits, the greater latency to higher orbits, and the number of satellites needed to cover an area. For example, Starlink his high speed and low latency but requires thousands of satellites, while HughsNet only uses one satellite but with greater latency.
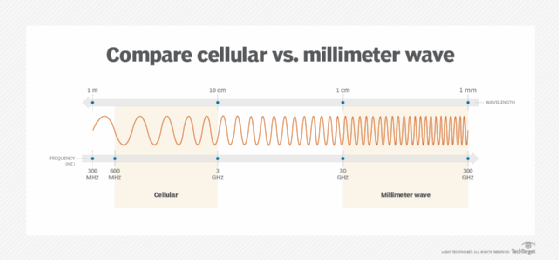
The ability of a radio signal to tolerate an obstructed line of sight is determined by the signal wavelength. The longer the wavelength, the greater its ability to penetrate through obstructions. Conversely, the shorter the wavelength, the less it can go through an obstruction, but the greater the data it can transmit.
The line of sight should be considered when placing Wi-Fi access points. Putting them up high will limit the obstructions from furniture. The thickness and composition of walls play a major factor. The slower 2.4 Ghz bands will go through walls better than the faster 5 GHz band of Wi-Fi AC and Wi-Fi 6.
The lines of sight for cellular base stations are also very important. They are often put in the highest points in a town, such as on water towers. 5G-NR data will have different abilities based on the wavelength used. Wideband signals cover greater distances and penetrate buildings well but won't offer the fastest speeds. Narrowband offers greater speed but doesn't work as well inside buildings. The fastest forms of 5G are heavily dependent on clear lines of sight. Millimeter waves can even be blocked by the hand holding the phone.
Most point-to-point wireless backhauls require a clear line of sight. Microwave data transmissions can be blocked or degraded by obstructing objects. Fog or rain can even degrade performance.
See also: transceiver, tropospheric propagation, Earth's mean radius, propagation delay, RFID
