lowerCamelCase
What is lowerCamelCase?
A part of CamelCase, lowerCamelCase is a naming convention in which a name contains multiple words that are joined together as a single word. In terms of capitalization, the first word is always all lowercase letters, including the first letter. The proceeding words are all capitalized -- only the first letter of each word is an uppercase letter.
So, instead of lower camel case, it's lowerCamelCase.
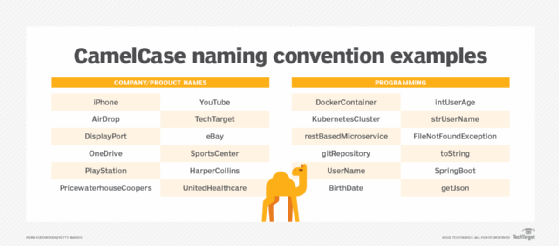
CamelCase gained popularity as a convention for naming variables, functions and parameters in various programming languages, such as Java, JavaScript, C++, Ruby, Simple Object Access Protocol, Synchronized Multimedia Integration Language and Extensible Markup Language (XML).
Why use lowerCamelCase?
The advantage of using CamelCase is improved readability by making the name stand out from the surrounding code. When lowerCamelCase is used, names are easy to understand without the need for comment documentation.
Another advantage is that lowerCamelCase names can be easily extended without fear of breaking existing code. For example, if a variable named myName needs to be renamed to myFullName, this can be done without affecting any code that uses the original name.
Additionally, lowerCamelCase provides a consistent way of naming things across different programming languages.
UpperCamelCase vs. lowerCamelCase
Another variation of CamelCase is UpperCamelCase in which the first letter of the new word is uppercase. This is the prime difference between the two variations.
UpperCamelCase is typically used for class names, while lowerCamelCase is used for method, variable and parameter names.
Specifically, lowerCamelCase should be used in cases where the variable name is already lowercase, such as when representing the lowercase versions of Hypertext Markup Language tags.
How to use lowerCamelCase
When using lowerCamelCase, there are a few things to keep in mind:
- Avoid abbreviations. Use full words instead.
- The first word should be lowercase -- for example, isConnected.
- Variable names should be descriptive. For example, userName is preferable to un.
Acronyms should be all uppercase, regardless of where they are in the sequence of words -- for example, XMLHttpRequest.
What are some alternatives to CamelCase?
Some alternatives to CamelCase include snake_case, PascalCase and kebab-case:
- Snake_case uses all lowercase letters and underscores to separate words -- for example, my_name.
- PascalCase is similar to CamelCase except that the first letter of every word is uppercase -- for example, MyName.
- Kebab-case uses all lowercase letters and hyphens to separate words -- for example, my-name.
Learn the difference between kebab vs. CamelCase and CamelCase vs. snake_case naming conventions.
