magnetic field strength
What is magnetic field strength?
Magnetic field strength is a measure of the intensity of a magnetic field in a given area of that field. Represented as H, magnetic field strength is typically measured in amperes per meter (A/m), as defined by the International System of Units (SI). Ampere and meter (or metre) are SI base units constructed from the SI's defining constants. Ampere is the measure of electric current, and meter is the measure of length.
Magnetic field strength, also called magnetic field intensity, is sometimes measured in oersted (Oe) rather than A/m. The oersted is part of the Gaussian system of units, which is based on the centimeter-gram-second (CGS) system. One Oe is equal to 79.577472 A/m, and one A/m is equal to 0.012566 Oe.
Magnetic field strength is one of two ways a magnetic field can be measured. The other way is magnetic flux density, or magnetic induction. Magnetic flux density is represented as B and measured in tesla (T). A tesla is equal to one weber per square meter (Wb/m2). Weber is the SI unit of magnetic flux. In Gaussian units, magnetic flux density is measured in gauss (G or Gs). One tesla is equal to 10,000 gauss.
Magnetic field strength and flux density
Magnetic field strength and magnetic flux density are directly related to each other. This relationship can be expressed through the formula B = μH. The Greek letter Mu (μ) represents magnetic permeability, which is measured in henry per meter (H/m). Permeability is a measure of how a substance responds to an applied magnetic field.
When electric current runs through a conductor, a magnetic field forms around that conductor. The strength of the field depends on multiple factors, including the amount of current. If you increase the current, the magnetic field strength also increases; if you decrease the current, the field strength decreases. The shape of the conductor also affects magnetic field strength. For example, a conductor might be formed into a coil rather than a straight line. A solenoid is a common example of a coiled conductor. If you increase the number of coils in the conductor, without changing its length, you'll also increase the magnetic field strength.
A magnetic field can be visualized as a series of magnetic field lines that represent the magnitude and direction of the magnetic field. The pattern of those lines depends on the shape of the conductor carrying the electric current. For example, field lines around a straight conductor radiate out from each point along the conductor in a series of concentric circles. However, the field lines around a coil form a pattern similar to that of a magnet, circling around from the north to south poles and through the center of the coil, where the field lines are at their densest.
The strength of a magnetic field corresponds to the density of the field lines. In a straight conductor, the field lines are at their densest nearest the conductor, so that is where the magnetic field is at its strongest. Conversely, the lines are more spread out the farther they get from the conductor, indicating a weaker field strength. In a coiled conductor, the lines are at their densest at the center of the coil, where the field strength is at its greatest. The field lines are less dense outside the coil and continue to thin out the further away they are from the conductor, where the field strength is at its weakest.
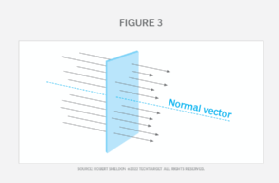
The total number of magnetic field lines penetrating through a defined surface in a specific amount of time is called the magnetic flux. It is directly proportional to the number of magnetic field lines that pass through the surface. The more concentrated the lines, the greater the flux density. If you increase the intensity of the magnetic field, you increase the number of field lines, indicating a greater level of flux. The rate of flux is also affected by the size of the surface area and the angle of the surface in relation to the field lines. Figure 1 shows two surfaces. The one on the right is much larger than the one on the left, but the field strength is the same in both cases. As a result, the surface on the right has a higher rate of flux.
Understanding magnetic field strength matters because of the use of magnets to store data on computer hard drives. (A variety of other devices, including generators, speakers and televisions, also rely on magnets or electromagnets.) Solid-state drives (SSDs), which read and write data on a substrate of interconnected flash memory chips, have emerged as a faster, more durable alternative to hard drives, though hard drives still have a role and a strong market presence.
Learn how much energy data centers consume, see how to create data center electrical safety guidelines and check out how multiphysics simulation might accelerate the advent of quantum computing -- and vice versa.
