user interface (UI)
What is user interface (UI)?
The user interface (UI) is the point of human-computer interaction and communication in a device. This can include display screens, keyboards, a mouse and the appearance of a desktop. It is also the way through which a user interacts with an application or a website.
The growing dependence of many businesses on web applications and mobile applications has led many companies to place increased priority on UI in an effort to improve the user's overall experience.
Types of user interfaces
The various types of user interfaces include:
- graphical user interface (GUI)
- command line interface (CLI)
- menu-driven user interface
- touch user interface
- voice user interface (VUI)
- form-based user interface
- natural language user interface
Examples of user interfaces
Some examples of user interfaces include:
- computer mouse
- remote control
- virtual reality
- ATMs
- speedometer
- the old iPod click wheel
Websites such as Airbnb, Dropbox and Virgin America display strong user interface design. Sites like these have created pleasant, easily operable, user-centered designs (UCD) that focus on the user and their needs.
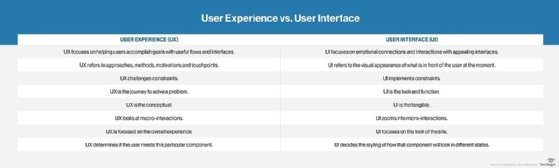
UI and UX
The UI is often talked about in conjunction with user experience (UX), which may include the aesthetic appearance of the device, response time and the content that is presented to the user within the context of the user interface. Both terms fall under the concept of human-computer interaction (HCI), which is the field of study focusing on the creation of computer technology and the interaction between humans and all forms of IT design. Specifically, HCI studies areas such as UCD, UI design and UX design.
An increasing focus on creating an optimized user experience has led some to carve out careers as UI and UX experts. Certain languages, such as HTML and CSS, have been geared toward making it easier to create a strong user interface and experience.
History of UI
In early computers, there was very little user interface except for a few buttons at an operator's console. Many of these early computers used punched cards, prepared using keypunch machines, as the primary method of input for computer programs and data. While punched cards have been essentially obsolete in computing since 2012, some voting machines still use a punched card system.
The user interface evolved with the introduction of the command line interface, which first appeared as a nearly blank display screen with a line for user input. Users relied on a keyboard and a set of commands to navigate exchanges of information with the computer. This command line interface led to one in which menus (lists of choices written in text) predominated.
Finally, the GUI arrived, originating mainly in Xerox's Palo Alto Research Center (PARC), adopted and enhanced by Apple and effectively standardized by Microsoft in its Windows operating systems.
Graphical UIs
Elements of a GUI include such things as windows, pull-down menus, buttons, scroll bars and icons. With the increasing use of multimedia as part of the GUI, sound, voice, motion video and virtual reality are increasingly becoming the GUI for many applications.
Mobile UIs
The emerging popularity of mobile applications has also affected UI, leading to something called mobile UI. Mobile UI is specifically concerned with creating usable, interactive interfaces on the smaller screens of smartphones and tablets and improving special features, like touch controls.







