memory management
What is memory management?
Memory management is the process of controlling and coordinating a computer's main memory. It ensures that blocks of memory space are properly managed and allocated so the operating system (OS), applications and other running processes have the memory they need to carry out their operations.
As part of this activity, memory management takes into account the capacity limitations of the memory device itself, deallocating memory space when it is no longer needed or extending that space through virtual memory. Memory management strives to optimize memory usage so the CPU can efficiently access the instructions and data it needs to execute the various processes.
What are the 3 areas of memory management?
Memory management operates at three levels: hardware, operating system and program/application. The management capabilities at each level work together to optimize memory availability and efficiency.
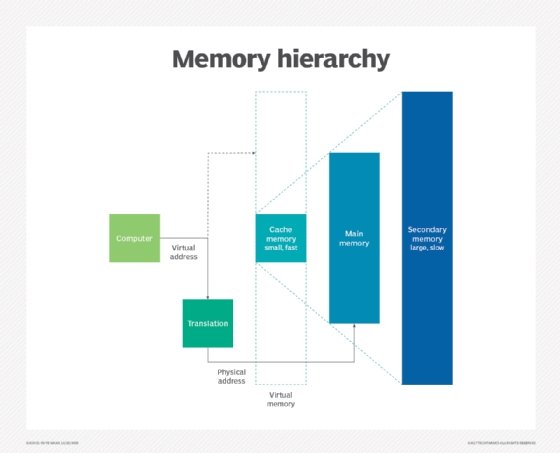
Memory management at the hardware level. Memory management at the hardware level is concerned with the physical components that store data, most notably the random access memory (RAM) chips and CPU memory caches (L1, L2 and L3). Most of the management that occurs at the physical level is handled by the memory management unit (MMU), which controls the processor's memory and caching operations. One of the MMU's most important roles is to translate the logical addresses used by the running processes to the physical addresses on the memory devices. The MMU is typically integrated into the processor, although it might be deployed as a separate integrated circuit.
Memory management at the OS level. Memory management at the OS level involves the allocation (and constant reallocation) of specific memory blocks to individual processes as the demands for CPU resources change. To accommodate the allocation process, the OS continuously moves processes between memory and storage devices (hard disk or SSD), while tracking each memory location and its allocation status.
The OS also determines which processes will get memory resources and when those resources will be allocated. As part of this operation, an OS might use swapping to accommodate more processes. Swapping is an approach to memory management in which the OS temporarily swaps a process out of main memory into secondary storage so the memory is available to other processes. The OS will then swap the original process back into memory at the appropriate time.
The OS is also responsible for handling processes when the computer runs out of physical memory space. When that happens, the OS turns to virtual memory, a type of pseudo-memory allocated from a storage drive that's been set up to emulate the computer's main memory. If memory demand exceeds the physical memory's capacity, the OS can automatically allocate virtual memory to a process as it would physical memory. However, the use of virtual memory can impact application performance because secondary storage is much slower than a computer's main memory.
Memory management at the program/application level. Memory management at this level is implemented during the application development process and controlled by the application itself, rather than being managed centrally by the OS or MMU. This type of memory management ensures the availability of adequate memory for the program's objects and data structures. It achieves this by combing two related tasks:
- Allocation. When the program requests memory for an object or data structure, the memory is allocated to that component until it is explicitly freed up. The allocation process might be manual or automatic. If manual, the developer must explicitly program that allocation into the code. If the process is automatic, a memory manager handles the allocation, using a component called an allocator to assign the necessary memory to the object. The memory manager might be built into the programming language or available as a separate language module.
- Recycling. When a program no longer needs the memory space that has been allocated to an object or data structure, that memory is released for reassignment. This task can be done manually by the programmer or automatically by the memory manager, a process often called garbage collection.
See also: paging, memory paging, address space, kernel, protected mode, segmented memory, virtual memory ballooning
