micro USB
What is a micro USB?
A micro USB is a miniaturized version of the Universal Serial Bus interface developed for connecting compact and mobile devices, such as smartphones, MP3 players, Global Positioning System devices, printers and digital cameras.
Micro USB connectors exist in four connector types: micro USB type A, micro USB type B, micro USB 2.0, and micro USB 3.0. Micro USB 3.0 is much like micro type B but with an additional pin group on the side for twice the wires, enabling USB 3.0's greater speed.
As a standard USB, the micro versions are plug-and-play and hot-swappable.
Mini versions of the USB specification that preceded the micro versions have been phased out. The micro type A connector was also phased out to favor the thinner, sturdier micro type B connector.
Micro USB 3.0 ports can also accept standard micro type B cables. To help with compatibility, some devices include an A/B dual port.
How does a micro USB work?
The micro USB connector comprises four main parts: the plug, the housing, the contacts and the printed circuit board.
The micro USB cable includes a single twisted pair to carry the electrical currents and signals needed to transfer data faster.
Micro USB vs. other USB technology
The main difference between the micro USB and standard USB is size. While standard USB ports are about 15 x 21 millimeters, micro USB ports are only 10-11 mm wide.
This makes micro USB a more compact connector for mobile and compact devices, like smartphones and digital cameras.
One of the main benefits of micro USB is its power delivery and data transfer speeds, which are better than other connectors, such as micro Digital Visual Interface, mini USB and micro High-Definition Multimedia Interface.
Micro USB is also easier to connect and disconnect than different types of connectors.
The history behind the micro USB
The USB peripheral bus standard was developed jointly by Compaq, IBM, Digital Equipment Corp., Intel, Microsoft, NEC and Northern Telecom. The technology is available without charge for all computer and device vendors.
The micro USB was invented to make smaller, portable devices possible. It was first introduced in 2007 and quickly rose in popularity due to its versatility and ease of use.
Since micro USBs are so small, they can be easily connected to compact devices, such as cellphones, tablets, digital cameras, smartwatches and many more.
What are micro USBs used for?
Micro USBs are used for various applications, from powering and charging smaller devices to transmitting data between them.
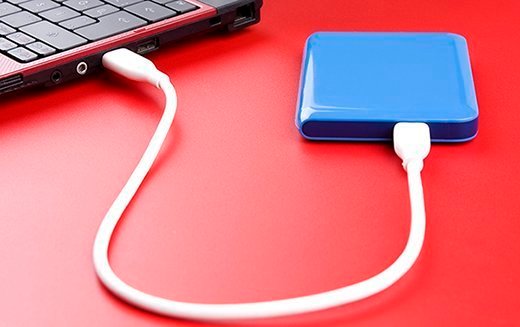
They are often used as fast-charging cables connecting smartphones and other compact devices to chargers or electrical outlets, computer peripherals, external hard drives, etc.
Additionally, micro USBs can be used as an adapter between different devices to facilitate data exchange, such as transferring photos from a digital camera to a computer.
Overall, micro USBs have become an essential tool for powering and connecting small devices central to our everyday lives.
See also: USB redirection, USB Killer, USB attacks and wearable computer.
