mobile device
What is a mobile device?
A mobile device is essentially a portable, handheld computer that enables users to access information, perform tasks and connect with other people and devices. Although the mobile device concept might seem to include any electronic device small enough to be carried around, the term implies wireless communications and the capacity for general mobile computing, along with other features.
The National Institute of Standards and Technology (NIST) defines a mobile device as a portable computing device that includes the following:
- Has a small form factor such that it can easily be carried by a single individual.
- Is designed to operate without a physical connection (e.g., wirelessly transmit or receive information).
- Possesses local, nonremovable or removable media for data storage.
- Includes a self-contained power source.
In addition, NIST states that mobile devices might also include voice communication capabilities, onboard sensors or built-in features for synchronizing local data with remote locations.

What are the types of mobile devices?
Mobile devices can include a wide range of features and capabilities. Many also offer performance on par with desktop computers. In addition, mobile devices can come in a variety of shapes and sizes, with form factors determined by the vendor. Regardless of their shape, however, they must still be portable enough for individual users to carry them around.
The exact capabilities of a mobile device depend on the type of device and its model. Many of today's mobile devices fall into one of the following categories:
- Smartphones. This type of mobile device rolls the features of a cellular phone into a small computer to provide a diverse set of capabilities. In addition to making phone calls, users can run productivity apps, send texts, get directions, check the weather, take pictures, reply to email, browse the internet and perform a variety of other tasks. Smartphones also provide touchscreens to easily carry out these tasks and to interface naturally with the system.
- Tablets. In one sense, tablets function a lot like overgrown smartphones, but without the calling capabilities. Users can take advantage of the increased screen real estate to perform the same tasks more efficiently than on a smartphone. The larger screen also makes it easier to carry out certain types of tasks, such as manipulating graphics or interfacing with the device through a soft keyboard. In this sense, a tablet behaves more like a small laptop than a smartphone. In fact, many users now opt for tablets over laptops because they provide all the power and capabilities they need in a more portable unit.

- E-readers. These devices are similar to tablets but are designed specifically for reading digital content, most notably e-books, such as those available through Amazon Kindle or Barnes & Noble Nook. E-readers are also designed to make reading easier on the eyes, while providing a lightweight form factor for more comfortable viewing.
- Wearables. Wearable technology includes devices such as smartwatches, smartglasses and fitness trackers. Some wearable devices provide an environment similar to a smartphone or tablet; a wearable device runs an operating system, includes touchscreen capabilities and lets users download apps. At the same time, wearable devices often pair with other devices, such as smartphones, for transferring data and more easily managing settings on the wearable device.
- Gaming consoles. These devices are specifically designed to provide users with dedicated handheld consoles for streaming games. Consoles such as Nintendo Switch, Steam Deck and Sony PlayStation Portal let users play games on the go, while offering high-definition graphics for an optimal experience.

To facilitate wireless communications, mobile devices usually support Wi-Fi, cellular or Bluetooth connectivity. Many provide two out of the three communications capabilities or even all three, as is the case for most of today's smartphones. In addition, users can often use their devices to access internet resources, participate in online platforms (such as social media) and stream content to their devices. They can also send emails or texts, as well as participate in video conferencing.
Mobile devices typically run a mobile operating system that manages the hardware and software resources. For example, Apple iPhones use iOS, and Android smartphones use the Android OS. Many mobile operating systems also let users download apps from an app store for their specific device types. In addition, mobile devices often provide features such as touchscreen interfaces, GPS and location services, built-in cameras and much more.
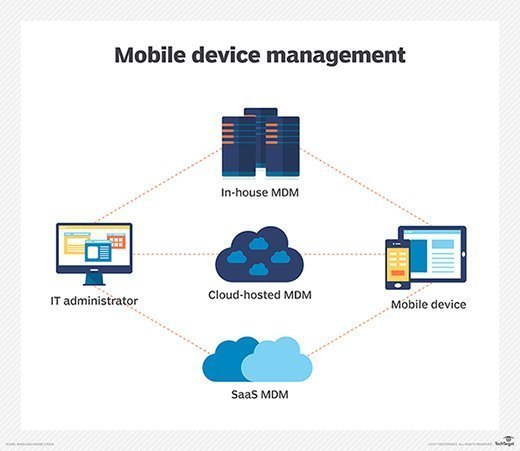
Within the enterprise and in the context of mobile device management (MDM), laptops are also considered a type of mobile device because they're portable and travel with the employees. They also require similar oversight and security requirements to those of smaller devices. Other than device management, however, the category of mobile device is generally confined to smaller form factors.
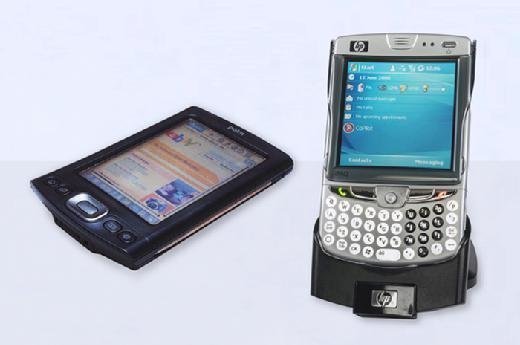
The first mobile device, in this sense, was the personal digital assistant (PDA). Popular in the 1990s and early 2000s, PDAs are considered the precursors to smartphones. However, because they could not make phone calls, they more closely resembled very small tablets. Most PDAs had a physical keyboard and limited software. Some had an electronically sensitive pad for written input.
The size of a mobile device involves compromise between the functionality of a larger interface and the ease of carrying a smaller device. Over the years, smartphones have grown larger. Some are even considered to be phablets, which are essentially overgrown smartphones. The phablet is larger than the average smartphone but smaller than most tablets. In theory, a phablet is considered pocket-sized, although that's still up for debate.
Learn seven key benefits of mobile device management for businesses and how to successfully implement mobile device management (MDM) for bring your own device (BYOD). Check out this ultimate guide to mobile device security in the workplace and explore the key differences between MDM and mobile application management (MAM).
