mobile hotspot
What is a mobile hotspot?
A mobile hotspot is a portable hardware device that serves as a wireless access point for connecting devices to the internet. It provides Wi-Fi routing capabilities similar to a home wireless router, except on a smaller scale. Nearby devices such as laptops, tablets or smartphones can interface with the mobile hotspot much as they do with other wireless routers. However, the mobile hotspot connects to the internet via a wireless cellular signal, rather than relying on a standard data signal.
Mobile hotspots are also known by various other names, such as portable hotspots, Wi-Fi hotspots, portable Wi-Fi hotspots and pocket routers. In some cases, mobile hotspots are referred to as travel routers, but travel routers are a different type of device that usually rely on public Wi-Fi or Ethernet connections, rather than cellular signals.
A mobile hotspot works by converting a 3G, 4G or 5G signal to a Wi-Fi signal and vice versa. It creates a Wi-Fi network that can be shared by multiple devices within about 10 meters of the hotspot. The device is meant to be portable so it can be used in locations such as cars, trains, coffee shops or hotel rooms, rather than be restricted to a specific location, as is the case with a home or business router. A mobile hotspot requires only a viable cellular signal.
Employees might enable their own mobile hotspots at work, a process sometimes referred to as bring your own network (BYON). Although they might have good reasons for doing this, they could be introducing risks into the corporate network. For example, an employee who uses a smartphone to create a mobile hotspot at work might be simultaneously connected to three networks: the carrier's cellular network, the employee's mobile hotspot and the corporate network. If the device, cellular network, or personal hotspot were compromised in any way, sensitive corporate data could be put at risk.

Types of mobile hotspot devices
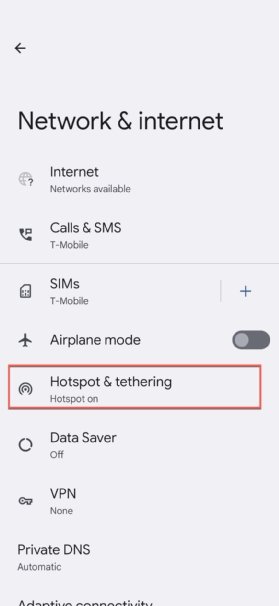
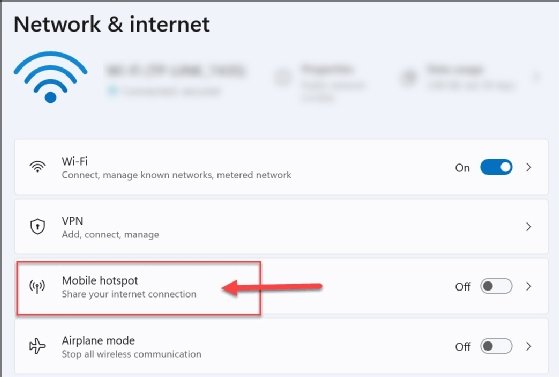
There are two types of mobile hotspot devices: smartphones with built-in tethering capabilities and dedicated hardware devices built specifically to act as mobile hotspots. When smartphones are used as mobile hotspots, they are sometimes referred to as cell phone hotspots or phone hotspots.
Dedicated mobile hotspots also go by various names, including dedicated hotspots, mobile hotspot devices, or simply mobile hotspots. In some cases, vendors and other sources might refer to these devices as MiFis or Mi-Fis, regardless of the manufacturer. However, the MiFi name is officially owned by Inseego Corp. (formerly Novatel) in the United States and many other countries.
Most of today's smartphones support tethering, which means that they can be used as mobile hotspots. To use this feature, the phone must be actively connected to a cellular network, with the phone's tethering feature enabled. The phone cannot be connected to a Wi-Fi network at the same time because the phone's Wi-Fi capabilities are used to create the hotspot.

Users can continue to use their smartphones as they normally would when tethering is enabled. For example, they can exchange email or text messages, browse the internet, or look at the weather. However, the phone's cellular service plan must support tethering, although this has become increasingly common in recent years.
As handy as smartphone tethering can be, it does come with limitations. Most service plans limit the amount of data that can be used for tethering; hence, this amount can be used up quickly. In addition, tethering can eat up the phone's battery, especially if multiple devices are connected. For these reasons, smartphone tethering tends to be better suited for occasional uses, rather than for ongoing hotspot services.
Instead of using their smartphones, many users purchase dedicated hotspot devices, especially if they frequently travel. A dedicated hotspot is a small, pocket-sized device that contains a SIM card for connecting to a cellular network. Most wireless carriers offer dedicated mobile hotspot devices, along with wireless data plans that support the devices.
Dedicated mobile hotspot devices typically run on batteries like smartphones, but some can also be plugged into a power source to provide more flexibility. Even when relying only on their batteries, however, dedicated devices can still provide hotspot services for a much longer time. In addition, dedicated mobile hotspots can support a greater number of connecting devices than a smartphone.
Learn how to troubleshoot when a hotspot is not working on Android and fix an iPhone Personal Hotspot. Find out if a hotspot works when a mobile device has no service. See how to improve mobile hotspot security in five steps and the differences between a wireless access point and a router.
