module
What is a module?
A module is a distinct assembly of components that can be easily added, removed or replaced in a larger system. Generally, a module is not functional on its own. In computer hardware, a module is a component that is designed for easy replacement. In computer software, a module is an extension to a main program dedicated to a specific function. In programming, a module is a section of code that is added in as a whole or is designed for easy reusability.
What are hardware modules?
For hardware, a module is an assembly of parts designed to be added and removed from a larger system easily. An example of a hardware module is a stick of RAM. Most modules are not functional on their own. They need to be connected to a larger system or be part of a system made up of several modules.
The concept of modularity or being made up of modules is common in computer hardware. A modular system has many advantages allowing for ease of repair, upgrade and extension of functionality. The various modules can be swapped out as needed. Standardization of hardware as interconnects enables several vendors to produce modules creating better choice for consumers.

While most systems are modular, the term module is not applied to all components in everyday speech. The expression module is often reserved for add-ins that are easy to remove and are boxy in shape. Some common examples are networking small form-factor pluggable modules, Mobile PCI Express Modules and dual in-line memory module RAM.
Embedded and industrial systems are beginning to use compute modules. These are entire single-board computers with connectors so they can be easily installed in a system. These are often used in digital signage or industrial equipment where the main equipment may have a long life span, but they want the ability to easily upgrade the computing performance in the future.
What are software modules?
Large software packages may have modules to define the sections of its functionality. This is often used to make the software easier to use for a specific use case or to define where boundaries exist in a program.
There are several ways that software can be modular.
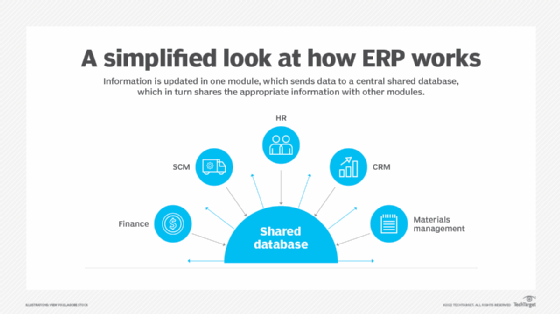
Enterprise resource planning (ERP) may implement separate modules for financing, ordering and human resources. This way, each job role only needs to know the functionality of its specific module within the program, instead of being familiar with the entire software suite.
The same underlying computer-aided design software, for example, may have different add-in modules for the various disciplines that may use it, such as an architecture or mechanical engineering module.
Photo editing software may have a RAW file development module to show the extra controls for RAW files and to signify that this portion must be done separately from the other software functionality.
What are computer programming modules?
Modular programming seeks to create separate portions of a program with isolated functionality. These smaller portions can be coded by different teams and then put together into the larger program. These may be called modules, assemblies or packages. In the Java programming language, a module is a distribution format combining the packages and how they are distributed.
These modules are often designed to be reusable. These can be called by the program as needed or used for different areas of the program. A program may import external modules programmed by others. These may also be called a library. Using modules maintained by others is increasingly becoming an attack vector for introducing malware through supply chain attacks.
See also: microservices, 3-tier application architecture, data center in a box, modular PC, hardware security module and ERP finance module.
