object
What is an object?
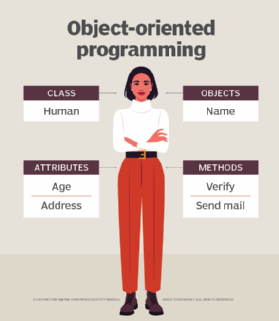
In object-oriented programming (OOP), objects are the things you think about first in designing a program and they are also the units of code that are eventually derived from the process. In between, each object is made into a generic class of object, and even more generic classes are defined so that objects can share models and reuse the class definitions in their code. Each object is an instance of a particular class or subclass with the class's own methods or procedures and data variables. An object is what actually runs in the computer.
Characteristics of an object
All individual objects possess three basic characteristics -- identity, state and behavior. Understanding these characteristics is crucial to knowing how objects and object-oriented logic work.
- Identity means that each object has its own object identifier and can be differentiated from all other objects. Each object's name, or identity, is unique and distinct from other objects.
- State refers to the properties of an object. For example, values of variables in the object contain data that can be added, changed or deleted.
- Behavior refers to actions that the object can take. For example, one object can respond to another object to carry out software functions.
Some of the things in programming that can be defined as objects include the following:
- variables, which hold values that can be changed;
- data structures, which are specialized formats used to organize and process data;
- functions, which are named procedures that perform a defined task; and
- methods, which are programmed procedures that are defined as components of a parent class and are included in any instance of that class.
Objects can do things and can have things done to them. For example, a function or method object can be programmed to modify the contents of a data structure or variable object.
Object-based languages
Object-based languages support the full complement of features of object-oriented programming. These features are as follows:
- Abstraction means that hiding implementation code that is not necessary for use by other objects. This helps make it easier for developers to change or add to objects over time.
- Polymorphism means that an object can mean or be used differently in different contexts.
- Inheritance means that object classes can reuse code from other classes. For example, relationships between objects can be assigned to create a class hierarchy, which enables developers to reuse coding logic to create families of related objects.
- Data encapsulation means that objects contain everything they need to function, including the object methods and any related data. The object can then make its interfaces available to other objects to enable them to use the object.
Most modern programming languages are considered object-oriented languages, but some are more object-oriented than others, depending on how the OOP principles are implemented in the language and how they are used. Some languages that were originally designed as procedural programming languages have, over the years, had OOP features added.
Some of the most common languages that are considered to be object-oriented currently in use include the following:
- Java
- Python
- C++
- C#
- Ruby
- PHP
- Lisp
- MATLAB
- R
- NET
- JavaScript
Non-OOP languages include the following:
In general, modern programming languages support some or all OOP features while non-OOP languages tend to be older or more specialized.
Object-based languages
Programming languages that use encapsulation and state -- including object-oriented languages -- are known as object-based languages. This category includes all OOP languages as well as some other languages that do not fully implement the OOP model. Some well-known object-based languages include the following:
- early versions of Visual Basic;
- early versions of JavaScript;
- Fortran 90; and
- Ada.
Many programming languages originated as object-based or even as non-object-based languages but added over the years features associated with OOP in some way. For example, early versions of Visual Basic and JavaScript lacked full object orientation but have added support since their introduction.
Benefits of using objects in programming
Using objects in programming has become commonplace, as most modern programming languages now support some or all of the principles of object-oriented programming. Some of the most important benefits of using objects in programming include the following:
- Code reuse is simplified using objects. Objects can be reused as is or modified slightly to enhance or modify object functions.
- Debugging is easier when objects are in use and a coding issue arises. Rather than having to review all of a codebase, developers can identify the object that is causing the issue. Debugging is simplified because a troublesome object can be replaced with a simpler object.
- Objects can be deployed without revealing details of their implementations.
- Modularity of objects means that they can be easily developed, updated and shared.
That is not to say that programming with objects does not have a downside. Some of the disadvantages of using objects in programming include the following:
- OOP concepts can be difficult to learn and learning to program with objects can be more complicated than learning to program with procedure programming languages.
- OOP programs can be significantly larger than procedural programs.
- OOP programs can run more slowly than programs written in procedural programming languages.
The differences between types of programming languages may not be as critical for simple programs, but for more complex programming projects there are differences that make one programming framework better than another.
Types of objects
Objects can be categorized based on what they do or how they work. Some of the most commonly used types of objects include the following:
- Function objects contain a single function and are used similarly to operating system or programming language functions.
- Immutable objects are not changed after their creation. Data and state of the object are fixed and are not changed by use of functions.
- Container objects may contain other objects.
- Factory objects are designed to create other objects.
These and other types of objects are based on design patterns, which represent repeatable solutions to common tasks or problems in programming. The patterns themselves are not objects but are used to develop objects that fulfill the functions of those patterns.
God objects are objects that break the rules by doing more than one thing. If you're still learning object- oriented programming, find out how to refactor the God object class antipattern. Otherwise, get started with this breakdown of object-oriented programming concepts.
Other Content Components







