mount point
What is a mount point?
A mount point is a directory on a file system that is logically linked to another file system. Mount points are used to make the data on a different physical storage drive easily available in a folder structure. Mount points are fundamental to Unix, Linux and macOS. Windows can use mount points, but it is not common.
Mount points in Unix, Linux and macOS
Mount points are fundamental to the operation of most Portable Operating System Interface-compatible operating systems, such as Unix, Linux and macOS. By using a mount point, data stored on different physical and logical volumes can be put on the same file system. This way, all the data needed on the system can be accessed from the root directory.
The mount command is used to make a device or file system accessible to the system, and then to connect its root directory to a mount point on the local file system.
The mount point location is typically an empty folder. If any files are already in that folder and it is then made into a mount point for another file system, the existing data will be no longer available, but it won't be deleted.
Linux has two default mount point locations for removable media: /dev (device) is where all physical devices are first mounted. From there, an additional link to the removable media is made in the /mnt (mount) directory. The /mnt directory and subdirectories are intended for mount points to removable or temporary files storage.
As an example of using mount points, consider plugging a USB flash drive into a Linux computer. The system detects the hardware device and puts it into the file system at /dev/sdc1. You then execute the command mount /dev/sdc1 /mnt/usb to mount the file system on the USB drive to the mount point location /mnt/usb. To make the data more convenient to use, you then create an additional mount point with the command mount /dev/sdc1 /home/john/files to put the data in the home directory.
The file for default mount points to be loaded at system startup is located in /etc/fstab for many Linux distributions.
As operating system distributions become more streamlined and user-friendly, the need for users to manually mount and unmount devices has diminished. Most desktop operating systems will care for this automatically for removable media.
Mount points in servers and containers
The need for mount points in server use is greater than ever. As data becomes more distributed and dynamic, it is increasingly common that the data a system needs is not directly attached to that system, requiring a mount point to make it accessible. For example, an application running on a server might rely on data stored on a network-attached storage device, so a mount point is made on the server pointing to the NAS data.
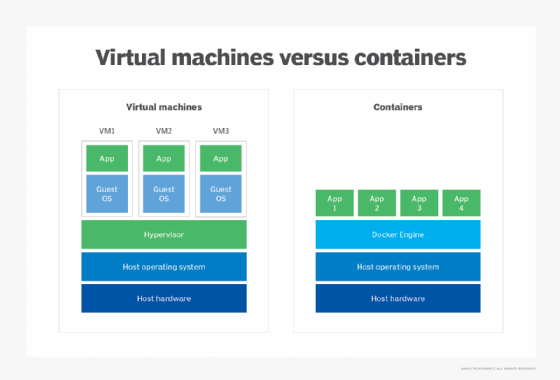
Virtual machines and containers make extensive use of mount points. These services are designed to be dynamic and ephemeral. For example, a Kubernetes instance can create and destroy Docker containers depending on the current load. These short-lived services might need to connect in order to read or write permanent data or settings, so a mount point is created that connects the external data to the service's private internal file system.
Mount points in Windows
Windows supports mount points, but they are not commonly used. The hosting parent volume must be New Technology File System (NTFS) formatted. A mount point can be created to the root of another locally attached volume. The target folder must be empty. Mount points are available from Windows 2000 onward.
NTFS symbolic links function similarly to mount points, but are much more flexible. They allow for relative paths and nonlocal storage through server message block shares. Symbolic links are available in Windows Vista and later versions.
Explore important storage administration skills, the key differences between containers and virtual machines, and the pros and cons of block vs. file vs. object storage.
