mouse
What is a mouse?
A mouse is a small device that a computer user pushes across a desk surface in order to point to a place on a display screen and to select one or more actions to take from that position. The mouse first became a widely used computer tool when Apple Computer made it a standard part of the Apple Macintosh.
Today, the mouse is an integral part of the graphical user interface (GUI) of any PC. The mouse apparently got its name by being about the same size and color as a toy mouse.
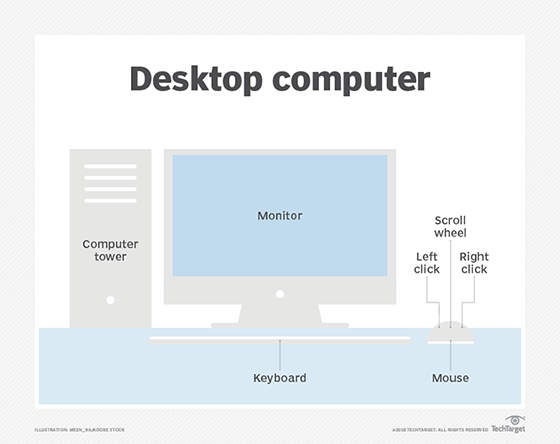
Mice typically have two buttons, a scroll wheel and a laser sensor. They are used to move the cursor on the screen, select objects and click on buttons.
History of the mouse
The first mouse was invented in 1964 by Douglas Engelbart, a computer scientist at the Stanford Research Institute. Engelbart's mouse was a wooden box with two wheels on the bottom and two buttons on top. It was connected to a computer by a wire.
The mouse was not widely adopted until the early 1980s when Apple Computer introduced the Macintosh computer with a mouse as its standard input device. The Macintosh was the first computer to use a GUI, and the mouse was essential for navigation.
Types of mice
There are two main types of mice: wired and wireless. Wired mice are connected to the computer by a cable, while wireless mice use radio waves to communicate with the computer.
Wired mice are more reliable than wireless mice, but they can be more difficult to use with laptops and other portable devices. Wireless mice are more convenient than wired mice. But they can be more expensive, and they may have a shorter battery life.
There are also a variety of other types of mice, including the following:
- Trackball mice. Trackball mice have a ball that is located on top of the mouse. The user moves the ball with their hand to move the cursor on the screen.
- Touchpad mice. Touchpad mice have a flat surface that is sensitive to touch. The user can move the cursor on the screen by dragging their finger across the touchpad.
- 3D mice. 3D mice have a sensor that enables them to track the user's hand movements in three dimensions. This lets the user interact with 3D objects on the screen.

Features and capabilities of mice
Mice have a variety of features and capabilities, including the following:
- Buttons. Mice typically have two buttons, but some mice have three or more buttons. The buttons can be used to perform different actions, such as clicking on objects, scrolling through text and opening menus.
- Scroll wheel. The scroll wheel is a wheel that is located between the two buttons on a mouse. It can be used to scroll up and down through text or images.
- Laser sensor. Laser sensors are used to track the movement of the mouse. Laser sensors are more accurate than optical sensors, but they can be more expensive.
- Wireless connectivity. Wireless mice use radio waves to communicate with the computer.
Benefits of using a mouse
There are many benefits to using a mouse, including the following:
- Accuracy. Mice are more accurate than other input devices, such as keyboards, for tasks such as clicking on small objects and selecting text.
- Speed. Mice can be used to navigate the GUI more quickly than other input devices.
- Comfort. Mice are more comfortable to use than other input devices for extended periods of time.
Mice are essential input devices for computers with GUIs. They are accurate, fast and comfortable to use.
