mu
What is mu (µ)?
The lowercase Greek letter µ (pronounced mu) generally represents the prefix multiplier 0.000001, i.e., 10-6 or one millionth. For example, 0.000001 farad or 10-6 F of electrical capacitance is commonly written as 1 µF. Similarly, 0.000000001 or 10 -9 farad is written as 0.001 µF.
More about µ
The symbol μ is the lowercase representation of the 12th letter of the Greek alphabet. The uppercase representation M is the same as the Latin/English letter M. Mu originated from the Phoenician letter mem, which itself evolved from the Egyptian hieroglyphic for water.
Like many other Greek letters, μ is used to represent several real-world quantities and phenomena across multiple academic and practical streams including the following:
- Physics
- Biology
- Chemistry
- Engineering
- Pharmacology
- Computer science
- Mathematics
In some texts, the symbol µ is an abbreviation for micrometers or microns. It is used to represent many real-world quantities, including magnetic permeability, coefficient of friction, electrical mobility of charged particles and mass per unit length.
The letter µ in physics: Coefficient of friction
In physics, the letter μ is commonly used to represent the coefficient of friction and magnetic permeability.
The coefficient of friction refers to the ratio of the frictional force (F) resisting the motion of two surfaces that are in contact to the normal force (N) that's pressing the two surfaces together. The frictional force and the motion of the object are in opposite directions.
Mathematically, the coefficient of friction is represented as:
μ = F/N
The coefficient of friction is dimensionless because both F and N are measured in units of force (e.g., newtons or pounds).
The value of μ is different for static friction and kinetic friction. In static friction, the object remains at rest until the force of static friction is removed. Also, the frictional force resists force applied to the object. In contrast, in kinetic friction, the frictional force resists the motion of an object.
The letter µ in physics: Magnetic permeability
Magnetic permeability refers to the relative change (increase or decrease) in the magnetic field inside a material compared to the magnetizing field where the material is located.
It is represented mathematically as:
μ = B/H
B in this case is magnetic flux density established within the material. It depends on the concentration of magnetic field lines (flux) per unit cross-sectional area.
H is the magnetic field strength of the magnetizing field. The field is produced by the flow of electric current through a wire.
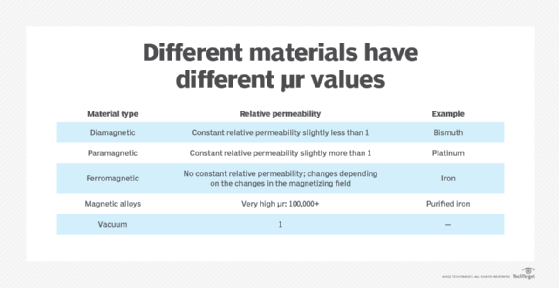
The designation μ0 (pronounced as mu naught or mu zero) refers to the permeability of free space. It is also known as the permeability of vacuum and the magnetic constant. In SI units, μ0 was earlier equal to 4π × 10-7 weber per ampere-meter. But with the redefinition of the ampere in 2019, μ0 is no longer equal to this value so it must be determined by experimentation. The relative permeability of μr is the ratio μ/μ0. In free space or a vacuum, this value is equal to 1. Like the coefficient of friction, μr is also dimensionless.
The letter µ in physics: Linear density
Linear density is the degree of mass per unit length. The value is especially useful for measuring the weight of objects that appear to be one-dimensional, such as threads, strings, yarn and wires.
Linear density is represented mathematically as:
µ = mass/length
The SI unit of linear density is kg/m.
In addition to kg/m, another unit is also used to represent mass per unit length. This is known as the tex, which is the number of grams (1 gram = 10-3 kg) per 1,000 meters. Another unit is the denier, which is the number of grams per 9,000 meters of thread. In real-world applications, a denier is a measure of the thread weight and thus, the opacity or fineness of a material.
The letter µ in chemistry
In chemistry, µ refers to the elementary particles muon and antimuon. A muon is similar to an electron. However, its mass is about 207 times the mass of the electron. It is created when an electron collides with its antiparticle positron (e+). The collision creates a photon, which subsequently forms the muon and its antiparticle, the antimuon.
A muon is represented as μ− and the antimuon as μ+. In a two-dimensional representation where the x-axis represents space and the y-axis represents time, the positron (e+) and antimuon (μ+) are shown as moving backward in time. In other words, these particles are shown as moving toward the past. Such diagrams are very useful to depict different types of particle interactions, particularly to visualize the effects of electromagnetic interactions between electrons and photons.
The letter µ in materials science
In material science, µ is used to represent magnetic moment. This vector quantity measures the tendency of an object to interact with an external magnetic field. It also represents the magnetic strength and orientation of a magnet.
Generally, an object's magnetic properties are visually represented in the form of loops emanating from a bar magnet with a north and south pole (dipoles). That's why magnetic moment is also known as magnetic dipole moment. The magnetic field of a magnetic dipole is proportional to its magnetic dipole moment.
Magnetic moment can be represented mathematically as:
µ = i . A
i = current traveling around the edge of a loop
A = cross-sectional area of the loop
The direction of the magnetic dipole moment is perpendicular to A.
All the following objects have magnetic dipole moments represented as µ:
- Electromagnets
- Permanent magnets
- Elementary particles: atoms, nuclei or subatomic particles
- Molecules
- Many planets
- Some moons
- Some stars
The letter µ in fluid mechanics
In fluid mechanics, µ represents viscosity. Viscosity measures a fluid's resistance to flow. This resistance is caused by shearing stress in the fluid as well as shearing stress between the fluid and its container.
Mathematically, viscosity is represented as the ratio of shearing stress to the rate of change of velocity (velocity gradient).
Shearing stress = τ (tau)
Rate of change of velocity = dv/dy = v
dv/dy is the derivative of velocity with respect to distance y.
Viscosity = µ = τ
dv/dy
The letter µ in electrical and electronic engineering
In electrical and electronic engineering, µ represents the electric mobility of a charged elementary particle like an electron or proton. Mobility simply means the tendency of the charged particles to move. It is proportional to the net charge of the particle.
When a uniform electric field acts upon this charged particle, it will accelerate until it reaches a constant drift velocity. This phenomenon is represented mathematically as:
µ = Vd / E
Vd = Drift velocity
E = Electric field
The SI unit of the electrical mobility is m2/ V s. This phenomenon is the basis for electrostatic precipitation which is used to remove particles from exhaust gases on a large scale.
The letter µ in thermodynamics
In thermodynamics, µ represents the chemical potential of a system or a component of a system. It refers to the chemical energy (Uc) possessed by 1 mol of the substance. Another way to describe chemical potential is "the energy added to a system when a particle is added to it."
Mathematically, chemical potential is represented as:
µ = Uc/N
When the chemical potential between two locations changes, it creates a chemical potential gradient. This forces the migration of the corresponding chemical species from the high chemical potential region to a lower chemical potential region.
The chemical potential µ can be associated with any type of substance including the following:
See also: mathematical symbols, Table of Physical Units
