non-interlaced display
What is a non-interlaced display?
A non-interlaced display is a screen display in which the lines are scanned progressively from the top to the bottom of the screen. In a non-interlaced display, there are several hundred horizontal lines in a frame (full screen). These lines are scanned from left to right and from top to bottom.
Unlike analog cathode ray tube technology used in older displays and televisions, modern liquid crystal displays, or LCDs, are inherently progressive. They use digital signals to update every row of pixels progressively with every screen refresh.
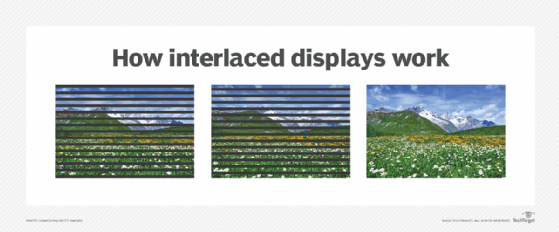
Interlaced vs. non-interlaced progressive scanning
The main difference between interlaced and non-interlaced displays is that non-interlaced displays draw all the lines on the screen in each refresh cycle, while interlaced displays only draw every other line.
With non-interlaced displays, this results in a smoother image with less flickering. However, it can also result in a lower frame rate as each frame is displayed for a longer period.
Non-interlaced displays are well suited for computer monitors as they provide a sharper image. They are also better at displaying video and other moving images than interlaced displays. Conversely, interlaced displays are better for televisions as they can provide a higher frame rate.
What is the refresh rate of a non-interlaced display screen?
The refresh rate for non-interlaced displays varies but is typically 60 hertz (Hz) or higher. This means that the screen refreshes -- draws all the lines on the screen -- 60 times per second or more.
As mentioned above, this output can work well for text and fixed graphics displays. However, with animated graphics -- especially images that move or change form rapidly -- if the refresh rate is lower than 60 Hz, users may notice a flicker on the screen. Repetitively, this flickering can cause headaches and eye fatigue.
The following are the most common refresh rates for non-interlaced displays:
- 60 Hz
- 75 Hz
- 85 Hz
- 100 Hz
- 120 Hz
- 144 Hz
- 165 Hz
- 200 Hz+

What about progressive scanning on TV monitors?
Progressively scanned displays are not limited to computer monitors. Many televisions now use progressive scanning, especially those with high-definition signals. When referring to TV signals, there are a few options identified by the number of horizontal lines scanned:
- 480p (progressive)
- 576p (progressive)
- 720p (progressive)
- 1080i (interlaced)
- 1080p (progressive)
Learn how 4K is being used in the enterprise and where it makes sense.
