northbound interface/southbound interface
What is a northbound interface/southbound interface?
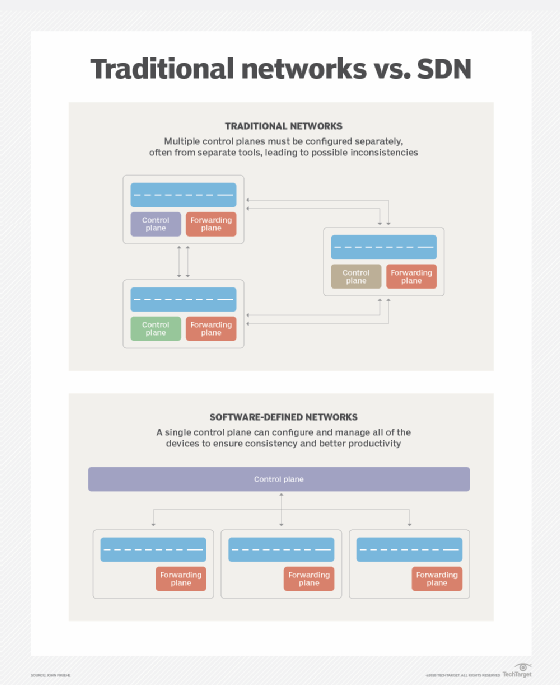
A northbound interface is an application programming interface (API) or protocol that allows a lower-level network component to communicate with a higher-level or more central component, while -- conversely -- a southbound interface allows a higher-level component to send commands to lower-level network components. Northbound and southbound interfaces are most associated with software-defined networking (SDN), but can also be used in any system that uses a hub-and-spoke or controller-and-nodes architecture.
North and south in this context can be thought of as on a map. The north is on the top and south on the bottom of the diagram. The higher-level elements control the lower-level ones. Some designs also have east-west interfaces for communication among peers.
It is easy to confuse northbound/southbound interface with northbound/southbound data flow or traffic. The interface defines the sender, receiver and data Format; it expresses the conceptual level of communication and covers the entire bidirectional API. Conversely, if data or traffic is said to be northbound, southbound or east-west, that merely describes whether it is going toward or away from the core. It is therefore possible to say that a southbound command went from the core to a node over the northbound interface.
Northbound and southbound interfaces in software-defined networking
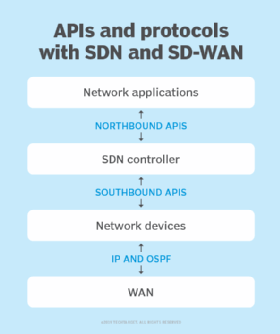
In SDN and virtualized networks, the network logical design and data flows are set by software configurations instead of through hardware or physical cabling changes. The configuration of the elements is set by the SDN controller, which sits in the control layer, at the center of the network diagram with north and south established in relation to it.
It is important to note that in SDN, the northbound and southbound interfaces are for networking control commands and APIs. The data or traffic carried by the network stays on the data layer and does not traverse the northbound and southbound interfaces.
Northbound interface in SDN
The northbound interface in SDN is the communication between the highest application layer and the SDN controller at the middle control layer. The application layer consists of network orchestration services, networking designer software, operator software or third-party applications that make decisions about the overall structure of the network.
In SDN, the operator or orchestration software does not directly issue commands or configurations to the network nodes. Instead, the operator uses the application layer to issue commands to the control layer over the northbound interface.
The northbound interface is often a REpresentational State Transfer API, or REST API, exposed by the SDN controller.
Southbound interface in SDN
The southbound interface in SDN is the communication between the SDN controller at the middle control layer and the lower networking elements at the data layer. The data layer consists of the physical or virtual network switches and ports.
The SDN controller takes the desired state of the network and translates it into specific commands and configurations that are then pushed to the network devices over the southbound interface.
Popular southbound interface standards are Simple Network Management Protocol, or SNMP; OpenFlow; and Open Shortest Path First, or OSPF.
Examples of northbound and southbound interfaces
An example use of the northbound and southbound interfaces involves a network engineer using network orchestration software to define a specific data route. The orchestration software sends the instructions to the SDN controller over the northbound interface. The SDN controller then sends the specific configurations to the physical switches over the southbound interface.
A more detailed example is Microsoft Azure software load balancing. The network controller is at the center layer and runs the software load balancer (SLB). The network operator sits at the application layer and uses Windows Admin Center to set the desired state. Windows Admin Center uses PowerShell as the northbound interface to send the commands to the SLB. The SLB then sends border gateway protocol (BGP) updates as the southbound interface to the virtual routers on the data layer. If the SLB finds an error in a router, it can automatically send the new configurations to the other routers through the southbound interface BGP, and then send a notification through the northbound interface to alert the operator of the issue.
Northbound and southbound interfaces in other systems
The concept of northbound and southbound interfaces can also be used in systems with automated control systems and nodes. It can be used when components communicate with different APIs or where an orchestrator is used. The use of separate interfaces contrasts with using a bus architecture.
See also: 12 common network protocols and their functions explained and What is open networking?
