open source
What is open source?
The term open source refers to any program whose source code is made available for use or modification as users or other developers see fit.
Unlike proprietary software, open source software is computer software that is developed as a public, open collaboration and made freely available to the public.
The following are several FAQs about open source software.
What is the history of open source software?
During the early years of software development, programmers would often share software in order to learn from one another and grow the field of computer programming.
This spurred the creation of the Free Software Foundation (FSF) and included David Knuth's TeX typesetting program in 1979 and Richard Stallman's GNU operating system in 1983. In fact, the early web browser Netscape was a free software with source code that would later go on to help develop open source software projects like Mozilla Firefox, a web browser that is still commonly used today.
The FSF later was replaced by the Open Source Initiative (OSI) -- a group of software developers that creates software intended to be freely shared, improved and redistributed by others.
The open source movement has not been without its detractors -- for instance, Microsoft's Jim Allchin, who in 2001 stated that the OSI was an "intellectual property destroyer."
Today, however, Microsoft and many others have joined the free and open source software movement in one way or another. This has created a major shift in how open source software is viewed.
Some other open source project contributors, funders and nonprofits include The Linux Foundation, the WordPress Foundation, Creative Commons, the Android Open Source Project and the Mozilla Foundation.
What are some examples of open source software licenses?
To summarize, the open source definition designates that:
- An open source software license is free of charge and redistribution is allowed to anyone without any restriction.
- The source code must be made available so that the receiving party will be able to improve or modify it.
- The license can require improved versions of the software to carry a different name or version from the original software.
- The software may be ported to a new operating system.
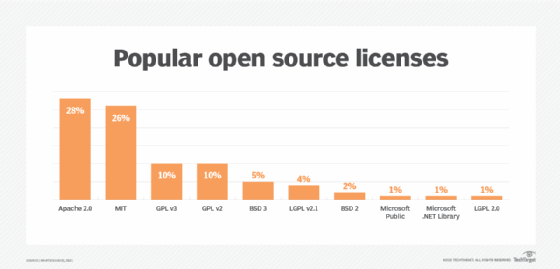
There have been many notable and widely used open source software licensing agreements to adopt the definition of open source in recent years including:
- The Apache web server license
- The Berkeley Software Distribution license
- The GNU General Public License
- The Massachusetts Institute of Technology License
- The Mozilla Public License
How is open source used in software development?
As mentioned previously, open source has played a large role in the software development community. In fact, a generation of open source tools have been developed and are used today by developers to help improve and troubleshoot issues with open source code during the early days of a software's development.
Some examples include:
- GitHub
- SourceForge
- Launchpad
What are some other open source products?
Open source technology is not limited to software development tools. There are a number of other popular software that falls under the open source umbrella. Examples include:
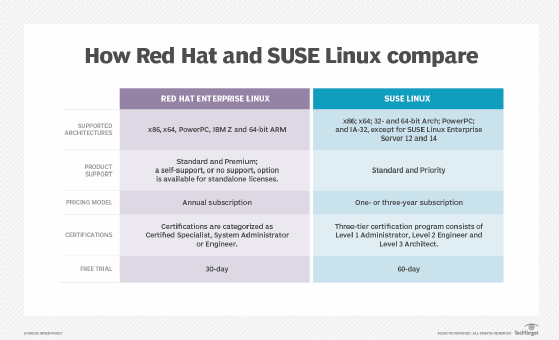
- Red Hat Software. An open source software platform, and IBM derivative, that provides a variety of enterprise-level productivity applications.
- LibreOffice. An open source office productivity suite, similar to Microsoft Office programs.
- GNU Image Manipulation Program. A GNU open source image manipulation tool with similar components to Adobe Photoshop.
- VLC Media Player. An open source audio and video file player.
What is the downside to open source programs?
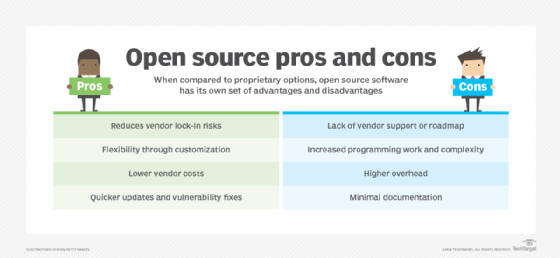
While open source licenses have made software generally more affordable and contributed immensely to the growth of software development, its widespread use is considered by many to be negative.
This is attributed to the lack of regulation that can open the door to numerous legal issues.
Furthermore, determining what should be open source and what should be closed source software remains a difficult and hotly debated topic.
To try and settle the debate, the open source community has taken to implementing classification schemes -- typically, dependent upon copyleft provisions in order to determine appropriate use cases for the open source software development model.
In 2008, the U.S. federal appeals court determined that OSS licenses must have legally binding requirements for any use of copyrighted material.
Should an end-user violate these open standards, they will lose their license and, therefore, be in violation of the copyright infringement standard, similar to if they used a proprietary license without authorization.
